[ad_1]
eCommerce servers are being focused with distant entry malware that hides on Nginx servers in a manner that makes it nearly invisible to safety options.
The risk obtained the title NginRAT, a mix of the appliance it targets and the distant entry capabilities it gives and is being utilized in server-side assaults to steal fee card knowledge from on-line shops.
NginRAT was discovered on eCommerce servers in North America and Europe that had been contaminated with CronRAT, a distant entry trojan (RAT) that hides payloads in duties scheduled to execute on an invalid day of the calendar.
NginRAT has contaminated servers within the U.S., Germany, and France the place it injects into Nginx processes which can be indistinguishable from respectable ones, permitting it to stay undetected.
RATs allow server-side code modification
Researchers at safety firm Sansec clarify that the brand new malware is delivered CronRAT, though each of them fulfill the identical operate: offering distant entry to the compromised system.
Willem de Groot, director of risk analysis at Sansec, instructed BleepingComputer that whereas utilizing very totally different methods to keep up their stealth, the 2 RATs seem to have the identical position, appearing as a backup for preserving distant entry.
Whoever is behind these strains of malware, is utilizing them to change server-side code that allowed them to document knowledge submitted by customers (POST requests).
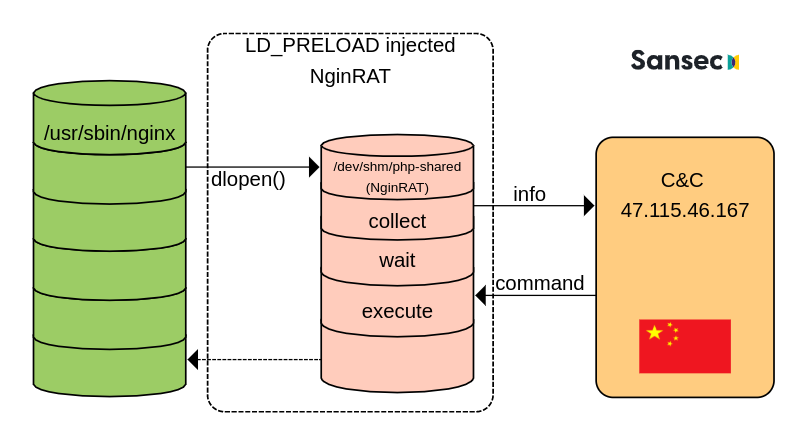
Sansec was in a position to research NginRAT after making a customized CronRAT and observing the exchanges with the command and management server (C2) positioned in China.
The researchers tricked the C2 into sending and executing a rogue shared library payload, as a part of the conventional malicious interplay, disguising the NginRAT “extra superior piece of malware.”
“NginRAT basically hijacks a number Nginx software to remain undetected. To do this, NginRAT modifies core performance of the Linux host system. When the respectable Nginx net server makes use of such performance (eg dlopen), NginRAT intercepts it to inject itself” – Sansec
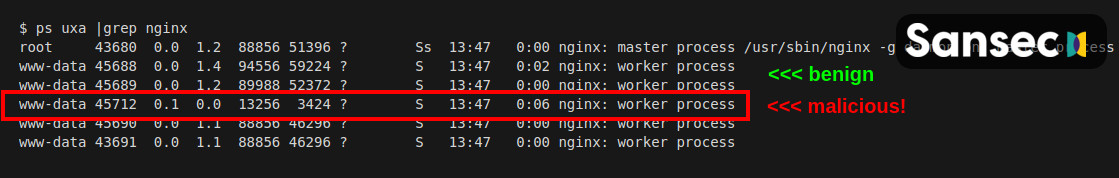
On the finish of the method, the Nginx course of embeds the distant entry malware in a manner that makes it nearly unimaginable to inform other than a respectable course of.
In a technical report right now, Sansec explains that NginRAT lands on a compromised system with the assistance of CronRAT by way of the customized “dwn” command that downloads the malicious Linux system library to the “/dev/shm/php-shared” location.
The library is then launched utilizing the LD_PRELOAD debugging characteristic in Linux that’s sometimes used to check system libraries.
More likely to masks the execution, the risk actor additionally added the “assist” possibility a number of instances on the finish. Executing the command injects the NginRAT into the host Nginx app.
As a result of NginRAT hides as a traditional Nginx course of and the code exists solely within the server’s reminiscence, detecting it might be a problem.
Nonetheless, the malware is launched utilizing two variables, LD_PRELOAD and LD_L1BRARY_PATH. Directors can use the latter, which incorporates the “typo,” to disclose the lively malicious processes by working the next command:
$ sudo grep -l LD_L1BRARY_PATH /proc/*/environ
/proc/17199/environ
/proc/25074/environSansec notes that if NginRAT is discovered on the server, directors also needs to examine the cron duties as a result of it is vitally seemingly that malware is hiding there, too, added by CronRAT.
[ad_2]
