[ad_1]
A current phishing marketing campaign focusing on Coinbase customers exhibits thieves are getting smarter about phishing one-time passwords (OTPs) wanted to finish the login course of. It additionally exhibits that phishers try to enroll in new Coinbase accounts by the tens of millions as a part of an effort to determine electronic mail addresses which can be already related to lively accounts.
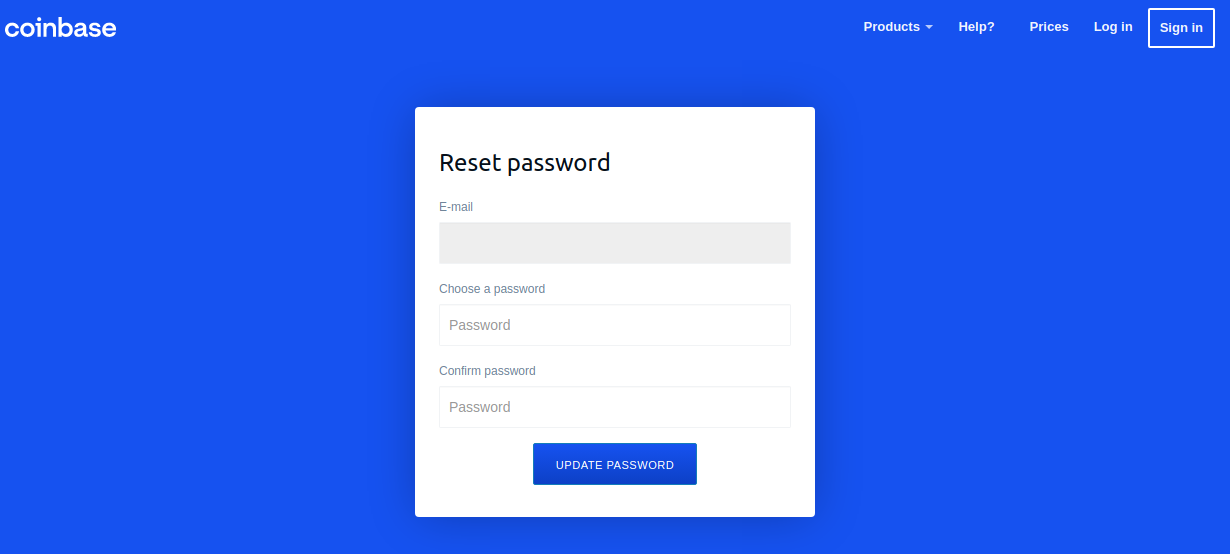
A Google-translated model of the now-defunct Coinbase phishing website, coinbase.com.password-reset[.]com
Coinbase is the world’s second-largest cryptocurrency trade, with roughly 68 million customers from over 100 international locations. The now-defunct phishing area at situation — coinbase.com.password-reset[.]com — was focusing on Italian Coinbase customers (the positioning’s default language was Italian). And it was pretty profitable, in response to Alex Holden, founding father of Milwaukee-based cybersecurity agency Maintain Safety.
Holden’s workforce managed to see inside some poorly hidden file directories related to that phishing website, together with its administration web page. That panel, pictured within the redacted screenshot under, indicated the phishing assaults netted no less than 870 units of credentials earlier than the positioning was taken offline.

The Coinbase phishing panel.
Holden stated every time a brand new sufferer submitted credentials on the Coinbase phishing website, the executive panel would make a loud “ding” — presumably to alert whoever was on the keyboard on the opposite finish of this phishing rip-off that that they had a stay one on the hook.
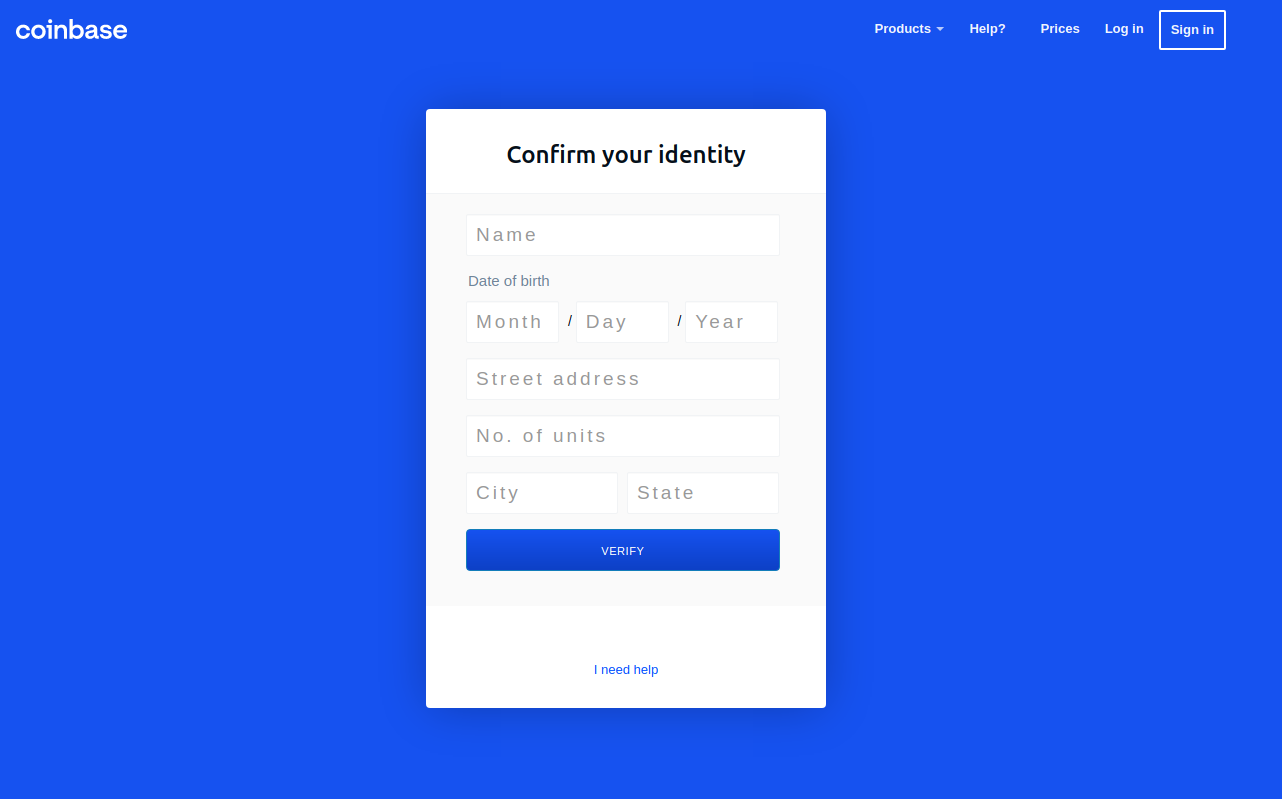
In every case, the phishers manually would push a button that triggered the phishing website to ask guests for extra data, such because the one-time password from their cellular app.
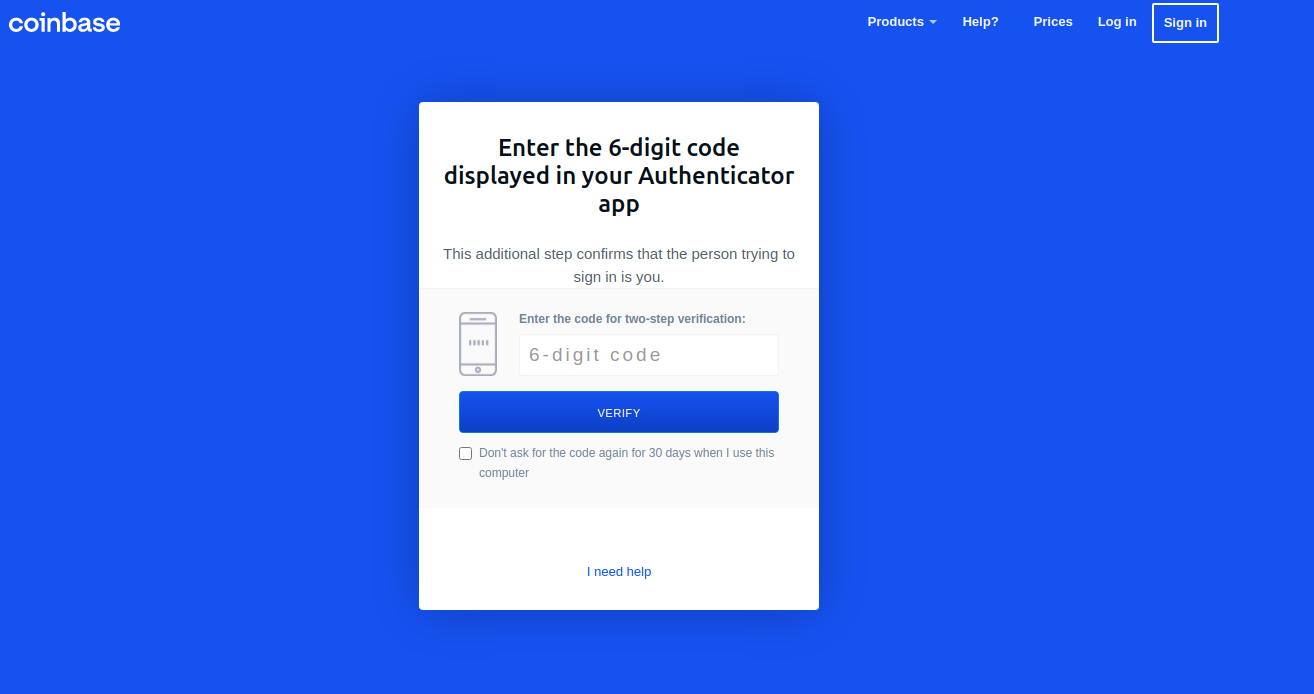
“These guys have real-time capabilities of soliciting any enter from the sufferer they should get into their Coinbase account,” Holden stated.
Urgent the “Ship Information” button prompted guests to provide extra private data, together with their title, date of start, and avenue deal with. Armed with the goal’s cellular quantity, they might additionally click on “Ship verification SMS” with a textual content message prompting them to textual content again a one-time code.
SIFTING COINBASE FOR ACTIVE USERS
Holden stated the phishing group seems to have recognized Italian Coinbase customers by making an attempt to enroll new accounts beneath the e-mail addresses of greater than 2.5 million Italians. His workforce additionally managed to recuperate the username and password information that victims submitted to the positioning, and nearly all the submitted electronic mail addresses led to “.it”.
However the phishers on this case doubtless weren’t excited by registering any accounts. Somewhat, the unhealthy guys understood that any makes an attempt to enroll utilizing an electronic mail deal with tied to an present Coinbase account would fail. After doing that a number of million occasions, the phishers would then take the e-mail addresses that failed new account signups and goal them with Coinbase-themed phishing emails.
Holden’s information exhibits this phishing gang carried out a whole lot of hundreds of halfhearted account signup makes an attempt each day. For instance, on Oct. 10 the scammers checked greater than 216,000 electronic mail addresses towards Coinbase’s methods. The next day, they tried to register 174,000 new Coinbase accounts.
In an emailed assertion shared with KrebsOnSecurity, Coinbase stated it takes “in depth safety measures to make sure our platform and buyer accounts stay as secure as doable.” Right here’s the remainder of their assertion:
“Like all main on-line platforms, Coinbase sees tried automated assaults carried out frequently. Coinbase is ready to robotically neutralize the overwhelming majority of those assaults, utilizing a combination of in-house machine studying fashions and partnerships with industry-leading bot detection and abuse prevention distributors. We repeatedly tune these fashions to dam new strategies as we uncover them. Coinbase’s Menace Intelligence and Belief & Security groups additionally work to observe new automated abuse strategies, develop and apply mitigations, and aggressively pursue takedowns towards malicious infrastructure. We acknowledge that attackers (and assault strategies) will proceed to evolve, which is why we take a multi-layered strategy to combating automated abuse.”
Final month, Coinbase disclosed that malicious hackers stole cryptocurrency from 6,000 prospects after utilizing a vulnerability to bypass the corporate’s SMS multi-factor authentication safety function.
“To conduct the assault, Coinbase says the attackers wanted to know the client’s electronic mail deal with, password, and cellphone quantity related to their Coinbase account and have entry to the sufferer’s electronic mail account,” Bleeping Laptop’s Lawrence Abrams wrote. “Whereas it’s unknown how the menace actors gained entry to this data, Coinbase believes it was by way of phishing campaigns focusing on Coinbase prospects to steal account credentials, which have grow to be frequent.”
This phishing scheme is one other instance of how crooks are developing with more and more ingenious strategies for circumventing in style multi-factor authentication choices, corresponding to one-time passwords. Final month, KrebsOnSecurity highlighted analysis into a number of new providers based mostly on Telegram-based bots that make it comparatively simple for crooks to phish OTPs from targets utilizing automated cellphone calls and textual content messages.These OTP phishing providers all assume the client already has the goal’s login credentials by way of some means — corresponding to by way of a phishing website just like the one examined on this story.
Savvy readers right here little question already know this, however to search out the true area referenced in a hyperlink, look to the best of “http(s)://” till you encounter the primary slash (/). The area on to the left of that first slash is the true vacation spot; something that precedes the second dot to the left of that first slash is a subdomain and must be ignored for the needs of figuring out the true area title.
Within the phishing area at situation right here — coinbase.com.password-reset[.]com — password-reset[.]com is the vacation spot area, and the “coinbase.com” is simply an arbitrary subdomain of password-reset[.]com. Nonetheless, when seen in a cellular machine, many guests to such a site could solely see the subdomain portion of the URL of their cellular browser’s deal with bar.
One of the best recommendation to sidestep phishing scams is to keep away from clicking on hyperlinks that arrive unbidden in emails, textual content messages or different media. Most phishing scams invoke a temporal aspect that warns of dire penalties do you have to fail to reply or act rapidly. In case you’re not sure whether or not the message is legit, take a deep breath and go to the positioning or service in query manually — ideally, utilizing a browser bookmark in order to keep away from potential typosquatting websites.
Additionally, by no means present any data in response to an unsolicited cellphone name. It doesn’t matter who claims to be calling: In case you didn’t provoke the contact, dangle up. Don’t put them on maintain when you name your financial institution; the scammers can get round that, too. Simply dangle up. Then you’ll be able to name your financial institution or wherever else you want.
By the way in which, when was the final time you reviewed your multi-factor settings and choices on the numerous web sites entrusted along with your most treasured private and monetary data? It could be price paying a go to to 2fa.listing (previously twofactorauth[.]org) for a checkup.
[ad_2]
