[ad_1]
A complicated persistent risk (APT) has been linked to cyberattacks on two biomanufacturing firms that occurred this yr with the assistance of a customized malware loader referred to as “Tardigrade.”
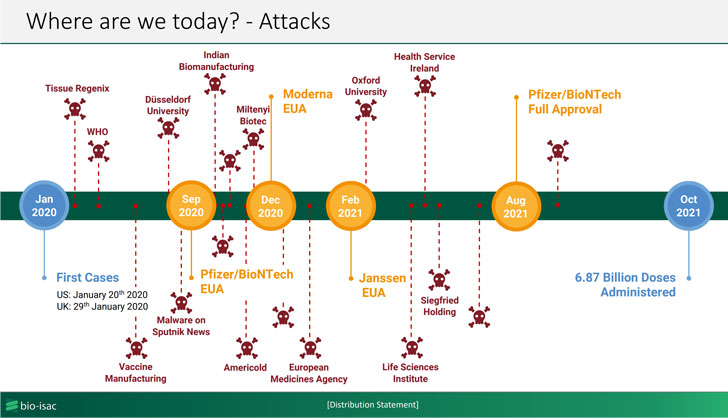
That is based on an advisory printed by Bioeconomy Data Sharing and Evaluation Heart (BIO-ISAC) this week, which famous that the malware is actively spreading throughout the sector with the probably objective of perpetrating mental property theft, sustaining persistence for prolonged intervals of time, and infecting the methods with ransomware.
BIO-ISAC, which commenced an investigation following a ransomware assault concentrating on an unnamed biomanufacturing facility earlier this spring, characterised Tardigrade as a classy piece of malware with “a excessive diploma of autonomy in addition to metamorphic capabilities.” The identical malware was then used to strike a second entity in October 2021.
The “actively spreading” intrusions haven’t been attributed to a selected risk actor or a nation, however the company informed The Hill that the efforts mirrored earlier assaults by a hacking group linked to Russia.
Unfold by way of phishing emails or contaminated USB drives, Tardigrade is a sophisticated offshoot of SmokeLoader, a Home windows-based backdoor operated by a bunch often called Smoky Spider and obtainable on the market on underground markets relationship all the way in which again to 2011, with the previous possessing capabilities to seize keystrokes, laterally transfer throughout the compromised community, and escalate privileges.
What’s extra, the malware acts as an entry level for added malware payloads and is engineered to function autonomously even when reduce off from its command-and-control server to hold out its malicious actions. Organizations within the biomanufacturing business are suggested to use software program updates, implement community segmentation, and take a look at offline backups of crucial organic infrastructure to mitigate the threats.
“This malware is extraordinarily troublesome to detect resulting from metamorphic habits. Vigilance on key personnel company computer systems is vital,” the researchers stated, including “Many machines within the sector use outdated working methods. Phase them off aggressively and speed up improve timelines.”
[ad_2]