[ad_1]
Microsoft says it discovered new variants of macOS malware often called WizardUpdate (additionally tracked as UpdateAgent or Vigram), up to date to make use of new evasion and persistence techniques.
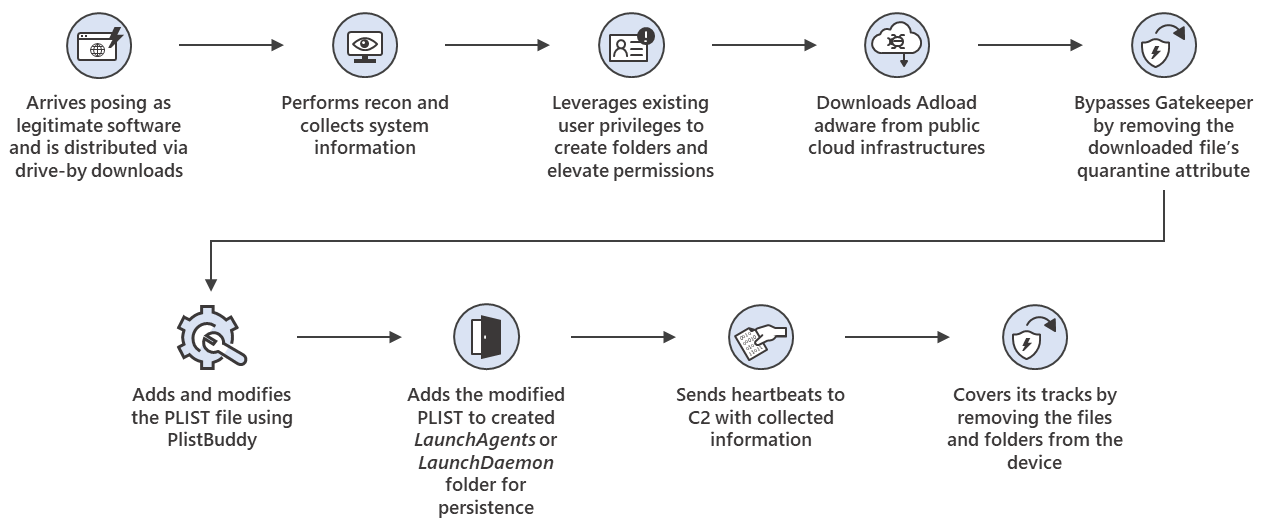
As Microsoft safety consultants discovered, the most recent variant — noticed earlier this month — is probably going being distributed by way of drive-by downloads and it impersonates authentic software program, simply because it was when risk intelligence agency Confiant found it camouflaged as Flash installers in January.
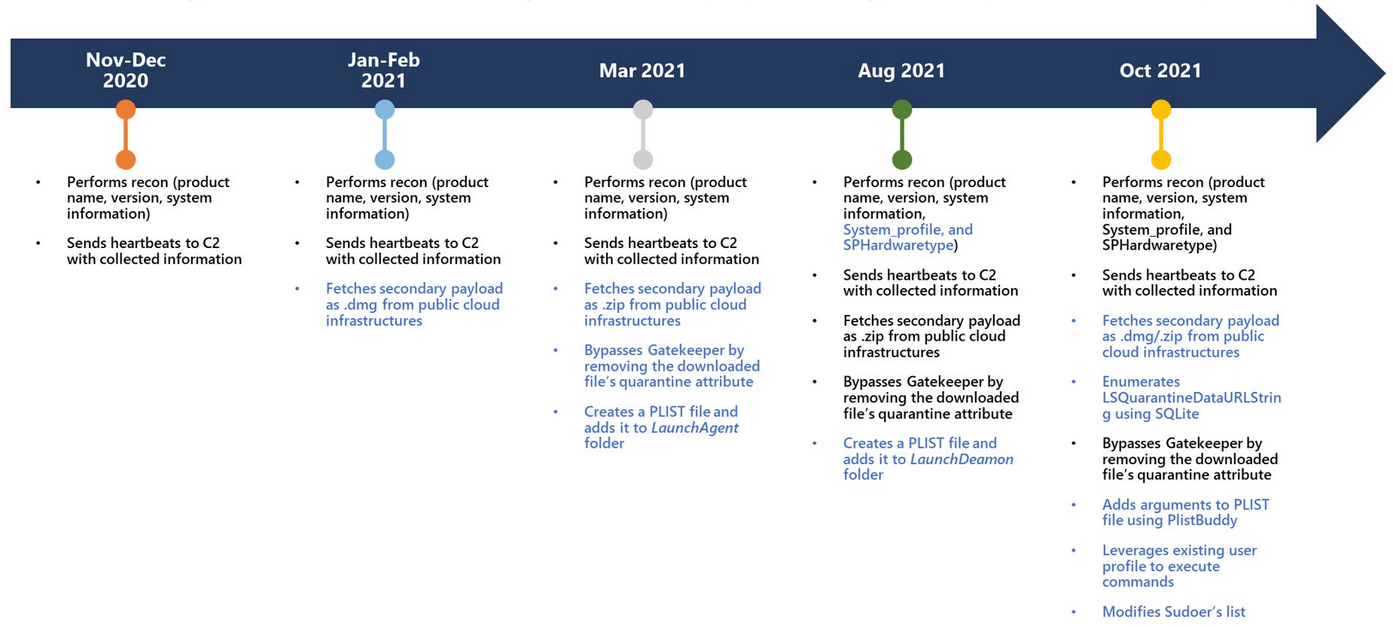
Because the first variants had been noticed in November 2020, when it was solely able to amassing and exfiltrating system data, WizardUpdate was up to date a number of instances by its builders.
The pattern collected by Microsoft researchers in October comes with a number of upgrades, together with the flexibility to:
- deploy secondary payloads downloaded from cloud infrastructure
- seize the full obtain historical past for contaminated Macs by enumerating LSQuarantineDataURLString utilizing SQLite
- bypass Gatekeeper by eradicating quarantine attributes from downloaded payloads
- modify PLIST information utilizing PlistBuddy
- leverage current person profiles to execute instructions
- change the sudoers checklist to give admin permissions to common customers
After it infects a goal’s Mac, the malware begins scanning for and amassing system data that will get despatched to its command-and-control (C2) server.
The trojan will deploy second-stage malware payloads, together with a malware variant tracked as Adload, energetic since late 2017 and identified for with the ability to slip by Apple’s YARA signature-based XProtect built-in antivirus to contaminate Macs.
“UpdateAgent abuses public cloud infrastructure to host further payloads and makes an attempt to bypass Gatekeeper, which is designed to make sure that solely trusted apps run on Mac gadgets, by eradicating the downloaded file’s quarantine attribute,” Microsoft mentioned.
“It additionally leverages current person permissions to create folders on the affected gadget. It makes use of PlistBuddy to create and modify Plists in LaunchAgent/ LaunchDeamon for persistence.”
WizardUpdate’s builders have additionally included evasion options within the newest variant, which might cowl its tracks by deleting created folders, information, and different artifacts created on the contaminated Macs
Malware on the Mac “worse than iOS”
AdLoad, one of many second-stage payloads delivered by WizardUpdate on compromised Macs, additionally hijacks search engine outcomes and injects commercials into internet pages for financial achieve utilizing a Man-in-The-Center (MiTM) internet proxy
It additionally positive aspects persistence by including LaunchAgents and LaunchDaemons and, in some circumstances, person cronjobs scheduled to run each two and a half hours.
Whereas monitoring AdLoad campaigns energetic since November 2020, when WizardUpdate was additionally first noticed, SentinelOne risk researcher Phil Stokes discovered a whole bunch of samples, roughly 150 of them distinctive and undetected by Apple’s built-in antivirus.
Most of the samples detected by Stokes had been additionally signed with legitimate Apple-issued Developer ID certificates, whereas others had been notarized to run below default Gatekeeper settings.
Though each WizardUpdate and AdLoad now solely deploy adware and bundleware as secondary payloads, they will swap at any time to extra harmful malware comparable to wipers or ransomware.
“Immediately, we now have a degree of malware on the Mac that we do not discover acceptable and that’s a lot worse than iOS,” mentioned Craig Federighi, Apple’s head of software program, in Might 2021 below oath whereas testifying within the Epic Video games vs. Apple trial.
[ad_2]
