[ad_1]
Within the final three years, because the arrival of the COVID-19 pandemic in america, the character of the office has modified considerably. As of February, 76 % of the workforce with a job that may be performed from dwelling in america was working a hybrid or utterly distant schedule, in response to Pew Analysis. Of that quantity, roughly one-third is totally distant.
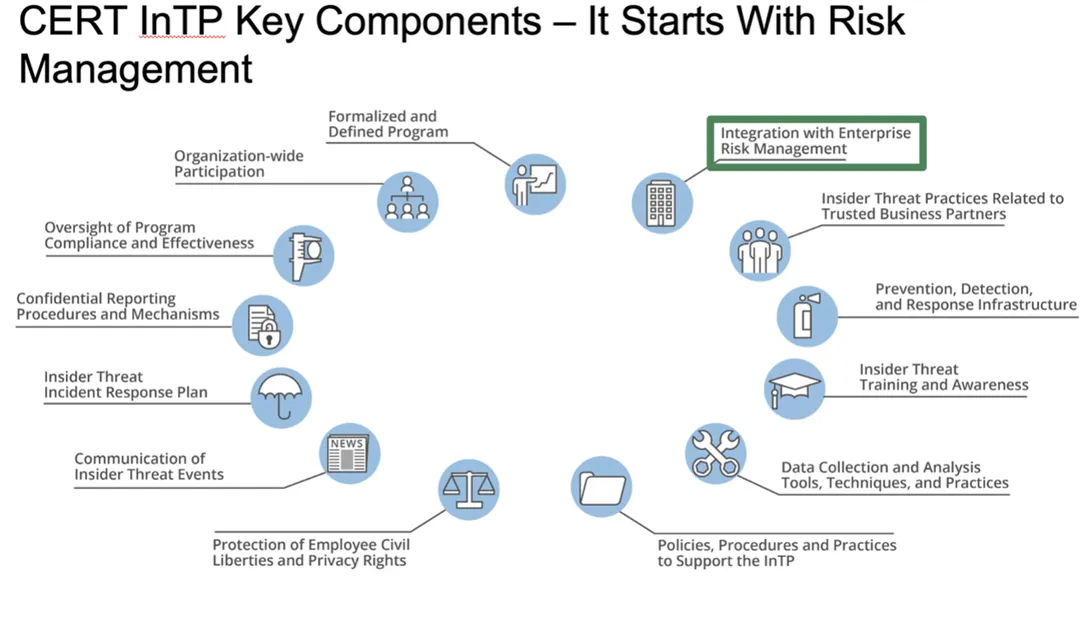
On this evolving work local weather, organizations must be more and more vigilant in opposition to malicious and unintentional (non-malicious) insider incidents. Many organizations by no means expertise a headline-grabbing, large-scale insider incident. As a substitute, many insider incidents are unintentional or non-malicious, sometimes the results of a safety incident or coverage violation. In response to our analysis, distraction is a key think about unintentional insider menace incidents. Distracted employees usually tend to make errors that may endanger a company, equivalent to failing to make use of their firm’s digital non-public community (VPN) or clicking on phishing hyperlinks in e mail. For a lot of hybrid and distant employees, distractions involving workspaces in shut proximity to kids and different members of the family can result in unintentional danger. Complete enterprise danger administration that features an insider danger program is a key part to securing organizations on this new surroundings. On this submit, we current the 13 key parts of an insider menace program.
Necessities Associated to Insider Menace
In 2011, the U.S. federal authorities launched an government order requiring authorities companies that function or entry categorised laptop networks to construct a proper insider menace detection and safety program.
The federal authorities had been beforehand charged with constructing the Nationwide Insider Menace Process Power, which develops a government-wide insider menace program for deterring, detecting, and mitigating insider threats.
In 2016, the Nationwide Industrial Safety Program Working Guide (NISPOM), which outlines authorities requirements for protection contractors, by way of NISPOM Confirming Change 2, additionally adopted a requirement that members of the Protection Industrial Base (DIB) construct insider menace detection and safety packages. DIB members, like the federal government companies, should conduct yearly self-assessments of established insider menace packages or impartial third-party assessments.
A lot of high-profile incidents have impacted for-profit corporations as effectively, leading to important momentum to construct insider menace packages within the non-public sector.
Throughout the CERT Nationwide Insider Menace Heart, we have now developed numerous sources to assist public- and private-sector organizations assess the chance posed by trusted insiders. These sources deal with serving to organizations perceive the crucial elements of an insider danger program and by what metrics a program is deemed efficient. We are able to additionally conduct third-party evaluations of insider menace packages for presidency or for-profit entities.
These sources embrace the CERT Widespread Sense Information to Mitigating Insider Menace, Seventh Version, which outlines 22 greatest practices that organizations can use to mitigate insider menace. Every greatest apply contains methods and ways for fast wins and high-impact options, mitigations to attenuate implementation challenges and roadblocks, and mappings to notable and related safety and privateness requirements. Greatest apply #2, Develop a Formalized Insider Threat Administration Program, supplies a roadmap for organizations to comply with.
Different sources embrace
The Why and When of Insider Threat Administration
Incorporating insider menace into enterprise-wide danger administration permits this system or group to leverage current sources by
- avoiding duplication of effort with current safety controls centered on exterior menace mitigation
- guaranteeing the insider danger program has participation from throughout the group, proving menace intelligence (info) from danger administration, info expertise, bodily safety, personnel administration, human sources, danger administration, basic counsel, and contours of enterprise.
When contemplating insider threats, you will need to first develop a danger administration mindset. A danger administration mindset understands that one of the best time to develop an insider danger program and a course of for mitigating incidents, each malicious and non-malicious, is earlier than an incident happens. When contemplating how one can shield organizational property, you will need to return to foundational cybersecurity rules and establish the crucial property or companies or enterprise processes that, if attacked, wouldn’t permit your group to realize its mission as outlined by Brett Tucker within the submit 10 Steps for Managing Threat: OCTAVE FORTE.
In figuring out crucial property (individuals, services, expertise, info), you will need to ask
- What services or products do we offer?
- What info are we entrusted to guard?
- What will we do to offer these companies or merchandise?
- What property will we use when performing these duties?
- What are the safety necessities of those property?
- What’s the worth of those property?
Key Components of an Insider Menace Program
Whereas info expertise (IT) is essential to an insider danger program, it is just one part. Too typically organizations fall into the lure of contemplating their program full as soon as they buy an insider danger administration device. Managing insider menace must be an ongoing, enterprise-wide effort that entails the IT division and others, equivalent to human sources, basic counsel, danger administration, and bodily safety.
This enterprise-wide method is required as a result of the flexibility to watch consumer exercise on a community doesn’t at all times assure that monitoring is permitted or that it’s not an invasion of privateness. The identical requirements and pointers that require federal companies and contractors to determine insider danger packages to watch consumer exercise on networks additionally requires privateness and civil liberty safety, which is an space the place a company’s basic counsel performs a key function. A holistic method to insider danger administration entails enterprise-wide participation into necessities, monitoring, governance, and oversight of this system—somebody watching the watchers. Oversight is a core precept in our greatest practices.
In September 2022, we revealed the seventh version of our Widespread Sense Information to Mitigating Insider Threats, which relies on analysis and evaluation of greater than 3,000 incidents. Along with greatest practices for mitigating insider threats and sources for varied stakeholders inside a company (i.e., administration, human sources, authorized counsel, bodily safety, IT, info safety, knowledge house owners, and software program), the information outlines the crucial parts of an insider danger program, proven within the determine under:
- Formalized and Outlined Insider Threat Administration Program (IRMP)—This system ought to embrace parts equivalent to directives, authorities, a mission assertion, management intent, governance, and a finances.
- Group-Vast Participation—This system ought to have energetic participation from all organizational elements that share or use program knowledge. Senior management ought to present seen help for this system, particularly when the info the IRMP wants is in siloes (i.e., knowledge lives solely in areas or departments equivalent to human sources [HR], bodily safety, info expertise [IT], or info safety).
- Oversight of Program Compliance and Effectiveness—A governance construction, equivalent to an IRMP working group or change management board, ought to assist the IRMP program supervisor formulate requirements and working procedures for the IRMP and suggest modifications to current practices and procedures. Additionally, an government council or steering committee ought to approve modifications advisable by the working group/change management board. Oversight contains annual self-assessments and exterior entity assessments that consider the compliance and effectiveness of the IRMP.
- Confidential Reporting Procedures and Mechanisms—Not solely do these mechanisms and procedures allow the reporting of suspicious exercise, however when intently coordinated with the IRMP, additionally they be sure that reliable whistleblowers usually are not inhibited or inappropriately monitored.
- Insider Menace Incident Response Plan—This plan should be greater than only a referral course of to outdoors investigators. It ought to element how alerts and anomalies are recognized, managed, and escalated, together with timelines for each motion and formal disposition procedures.
- Communication of Insider Menace Occasions—Occasion info must be appropriately shared with the right organizational elements, whereas sustaining workforce member confidentiality and privateness. This kind of communication contains insider danger traits, patterns, and potential future occasions in order that insurance policies, procedures, coaching, and so on., could be modified as acceptable.
- Safety of Workforce Member Civil Liberties and Privateness Rights—Authorized counsel ought to evaluate the IRMP’s selections and actions in any respect levels of program growth, implementation, and operation.
- Integration with Enterprise Threat Administration—The IRMP should be sure that all facets of the group’s danger administration embrace insider menace issues (not simply outdoors attackers), and the group ought to think about establishing a standalone part for insider danger administration.
- Practices Associated to Managing Trusted Exterior Entities (TEEs)—These practices embrace agreements, contracts, and processes reviewed for insider menace prevention, detection, and response capabilities.
- Prevention, Detection, and Response Infrastructure—This infrastructure contains elements, equivalent to community defenses, host defenses, bodily defenses, instruments, and processes.
- Insider Menace Coaching and Consciousness—This coaching encompasses three facets of the group: (1) insider menace consciousness coaching for the group’s whole workforce (e.g., staff, contractors, consultants), (2) coaching for IRMP personnel, and (3) role-based coaching for mission specialists who’re more likely to observe sure facets of insider menace occasions (e.g., HR, Info Safety, Counterintelligence, Administration, Finance).
- Knowledge Assortment and Evaluation Instruments, Strategies, and Practices—These instruments, methods, and practices embrace consumer exercise monitoring (UAM), knowledge assortment, and evaluation parts of this system. Detailed documentation is required for all facets of information assortment, processing, storage, and sharing to make sure compliance with workforce member privateness and civil liberties.
- IRMP Insurance policies, Procedures, and Practices—The IRMP will need to have formal paperwork that element all facets of this system, together with its mission, scope of threats, directives, directions, and customary working procedures.
- Optimistic Incentives—Organizations ought to encourage optimistic workforce habits somewhat than coerce it by leveraging positive-incentive-based organizational practices centered on rising job engagement, perceived organizational help, and connectedness at work.
Insider Threat and AI
Machine studying (ML) and synthetic intelligence (AI) have been on the forefront of insider menace anomaly detection for numerous years. Conventional safety controls have concerned instruments that may monitor consumer exercise, however solely after receiving steerage from an analyst on particular behavioral anomalies to be looking out for. This association limits the scope of monitoring to what’s accessible inside conventional controls and at an analyst’s discretion. Such an method could flag exercise if a consumer downloads 100 paperwork in a day, however what if an insider does one doc a day over 100 days?
AI and ML can delve deeper to find out probably worrisome patterns of exercise by a person by making an allowance for statistical and human anomalies.
A brand new class of insider menace instruments, which depend on consumer entity and habits analytics (UEBA), widens the aperture past technical anomalies involving an worker’s laptop use to include completely different knowledge units. If an worker is leaving a company, for instance, the instruments would pull knowledge from the HR administration system. These instruments additionally account for exercise in a company’s bodily safety programs, together with badging information or digicam programs.
UEBA instruments are utilizing AI at first by incorporating completely different knowledge from throughout a company and informing analysts of anomalies with out analysts telling the instruments what must be reported.
Most staff don’t be part of a company aspiring to do hurt, and, as we referenced earlier, most insider incidents that do happen are unintentional. No matter intent, all insider incidents contain a misuse of licensed entry to a company’s crucial property, and numerous the incidents are unintentional. We within the CERT Division of the SEI are working to grasp the underlying causes behind stressors and regarding behaviors to detect insider threats early and provide staff help earlier than they commit a dangerous act.
[ad_2]