[ad_1]
Information pushed organizations acknowledge the intrinsic worth of knowledge and understand that monetizing information is not only about promoting information to subscribers. They perceive the oblique financial affect of knowledge and the worth that good information brings to the group. They need to democratize information and make it accessible for enterprise determination makers to understand its advantages. Immediately, this is able to imply replicating information throughout a number of disparate databases, which requires shifting the information throughout varied platforms.
Amazon Redshift information sharing allows you to securely and simply share stay information throughout Amazon Redshift clusters or AWS accounts for learn functions. Information sharing can enhance the agility of your group by providing you with on the spot, granular, and high-performance entry to information throughout Amazon Redshift clusters with out manually copying or shifting it. Information sharing supplies you with stay entry to information in order that your customers can see essentially the most up-to-date and constant data because it’s up to date in Amazon Redshift clusters.
Cross-account information sharing allows you to share information throughout a number of accounts. The accounts may be throughout the similar group or throughout totally different organizations. We have now in-built extra authorization steps for safety management, since sharing information throughout accounts might additionally imply sharing information throughout totally different organizations. Please assessment AWS documentation on cross-account information sharing and a weblog from our colleague for detailed steps. We even have a YouTube video on establishing cross-account information sharing for a enterprise use case which you’ll be able to refer as properly.
Cross-account information sharing state of affairs
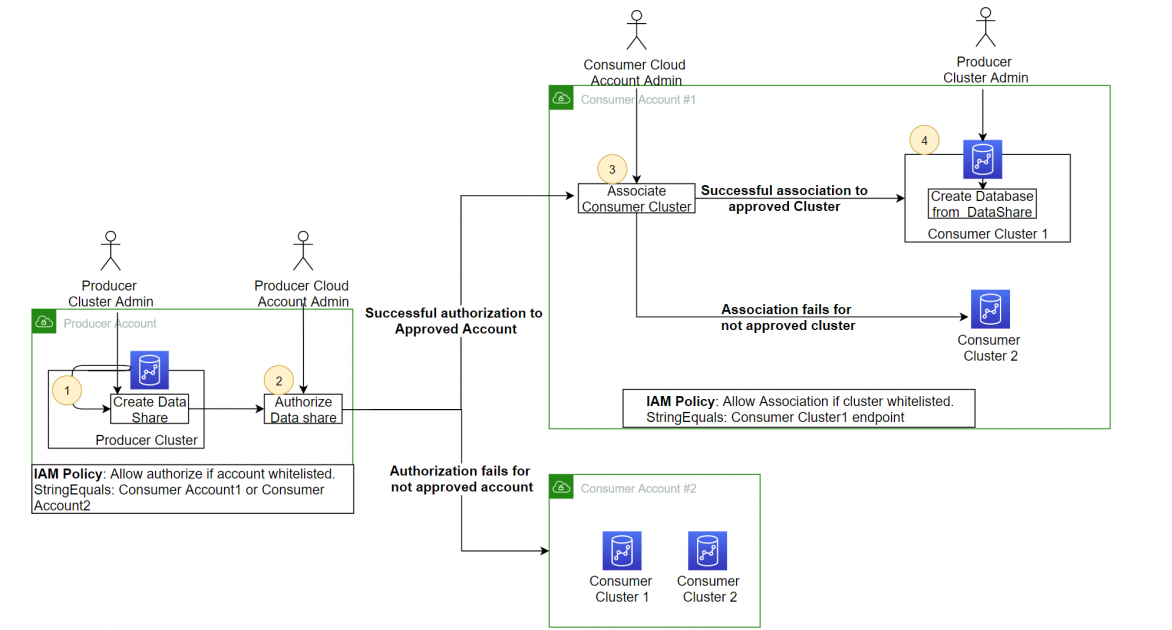
For this publish, we’ll use this use case to display how you possibly can setup cross-account information sharing with the choice to regulate information sharing to particular shopper accounts from the producer account. The producer group has one AWS account and one Redshift cluster. The patron group has two AWS accounts and three Redshift clusters in every of the accounts. The producer group needs to share information from the producer cluster to one of many shopper accounts “ConsumerAWSAccount1”, and the buyer group needs to limit entry to the information share to a particular Redshift cluster, “ConsumerCluster1”. Sharing to the second shopper account “ConsumerAWSAccount2” ought to be disallowed. Equally, entry to the information share ought to be restricted to the primary shopper cluster, “ConsumerCluster1”.
Walkthrough
You may setup this conduct utilizing the next steps:
Setup on the producer account:
- Create an information share within the Producer cluster and add schema and tables.
- Setup IAM coverage to regulate which shopper accounts may be approved for information share.
- Grant information share utilization to a shopper AWS account.
Setup on the buyer account:
- Setup IAM coverage to regulate which of the buyer Redshift clusters may be related to the producer information share.
- Affiliate shopper cluster to the information share created on the producer cluster.
- Create database referencing the related information share.
Stipulations
To arrange cross-account information sharing, you need to have the next conditions:
- Three AWS accounts. As soon as for producer < ProducerAWSAccount1>, and two shopper accounts – <ConsumerAWSAccount1> and < ConsumerAWSAccount2>.
- AWS permissions to provision Amazon Redshift and create an IAM position and coverage.
We assume you may have provisioned the required Redshift clusters: one for the producer within the producer AWS Account, two Redshift clusters in ConsumerCluster1, and optionally one Redshift cluster in ConsumerCluster2
- Two customers in producer account, and two customers in shopper account 1
- ProducerClusterAdmin
- ProducerCloudAdmin
- Consumer1ClusterAdmin
- Consumer1CloudAdmin
Safety controls from producer and shopper
Accredited record of shopper accounts from the producer account
Once you share information throughout accounts, the producer admin can grant utilization of the information share to a particular account. For extra safety to permit the separation of responsibility between the database admin and the cloud safety administrator, organizations would possibly need to have an authorized record of AWS accounts that may be granted entry. You may obtain this by creating an IAM coverage itemizing all the authorized accounts, after which add this coverage to the position connected to the producer cluster.
Creating the IAM Coverage for the authorized record of shopper accounts
- On the AWS IAM Console, select Insurance policies.
- Select Create coverage.

- On the JSON tab, enter the next coverage:
That is the producer facet coverage. Word: you need to exchange the next textual content with the particular particulars to your cluster and account.
- From the Amazon Redshift console within the producer AWS Account, select Question Editor V2 and hook up with the producer cluster utilizing non permanent credentials.

- After connecting to the producer cluster, create the information share and add the schema and tables to the information share. Then, grant utilization to the buyer accounts<ConsumerAWSAccount1> and <ConsumerAWSAccount2>
Word: the GRANT shall be profitable despite the fact that the account shouldn’t be listed within the IAM coverage. However the Authorize step will validate in opposition to the record of authorized accounts within the IAM coverage, and it’ll fail if the account shouldn’t be within the authorized record.
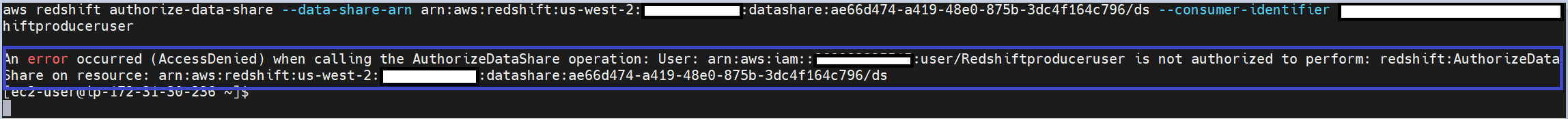
- Now the producer admin can authorize the information share through the use of the AWS CLI command line interface or the console. Once you authorize the information share to <ConsumerAWSAccount1>, then the authorization is profitable.
- Once you authorize the information share to <ConsumerAWSAccount2>, the authorization fails, because the IAM coverage we setup within the earlier step doesn’t enable information share to <ConsumerAWSAccount2>.
We have now demonstrated how one can prohibit entry to the information share created on the producer cluster to particular shopper accounts through the use of a conditional assemble with an authorized account record within the IAM coverage.
Accredited record of Redshift clusters on shopper account
Once you grant entry to an information share to a shopper account, the buyer admin can decide which Redshift clusters can learn the information share by associating it with the suitable cluster. If the group needs to regulate which of the Redshift clusters the admin can affiliate with the information share, then you’ll be able to specify the authorized record of Redshift clusters through the use of the cluster ARN in an IAM coverage.
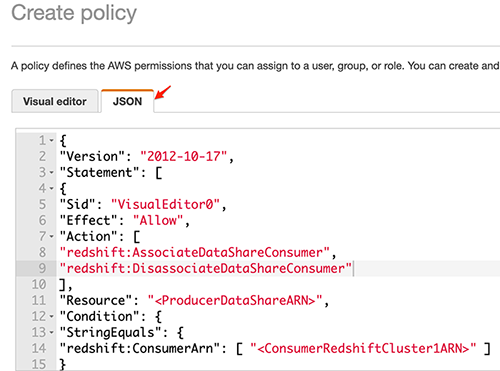
- On the AWS IAM Console, select Insurance policies.
- Select Create coverage.

- On the JSON tab, enter the next coverage:
That is the buyer facet coverage. Word: you need to exchange the next textual content with the particular particulars to your cluster and account.
-
- “Useful resource”: “*” – Substitute “*” with the ARN of the particular information share.
- Substitute “<ProducerDataShareARN>” with the ARN of the information share created within the Redshift cluster in AWS Client account 1.
- Substitute “<ConsumerRedshiftCluster1ARN>” with the ARN of the primary Redshift cluster in AWS Client account 1.
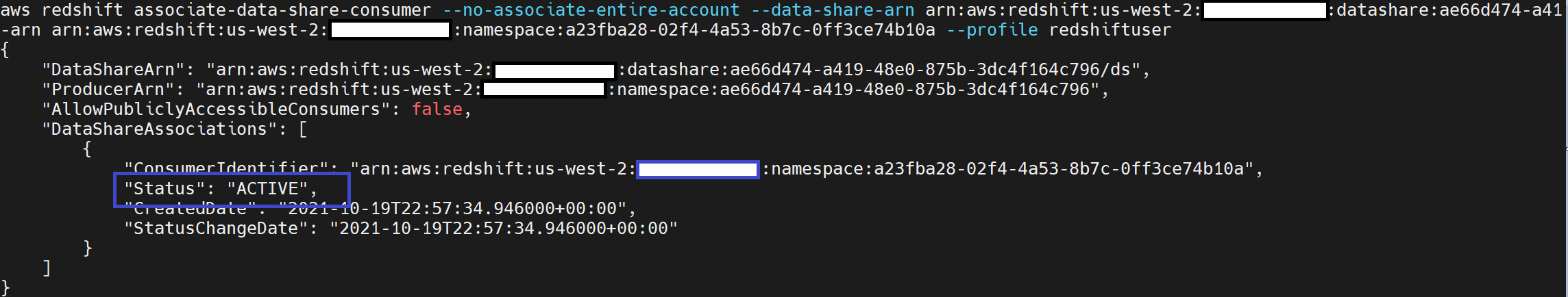
- Now the buyer admin can affiliate the information share utilizing the AWS CLI command line interface or the console. Once you affiliate the Redshift cluster 1
<ConsumerRedshiftCluster1ARN >, the affiliation is profitable.
- Now the buyer admin can affiliate the information share through the use of the AWS CLI command line interface or the console. Once you affiliate the Redshift cluster 2
<ConsumerRedshiftCluster2ARN >, the affiliation fails.
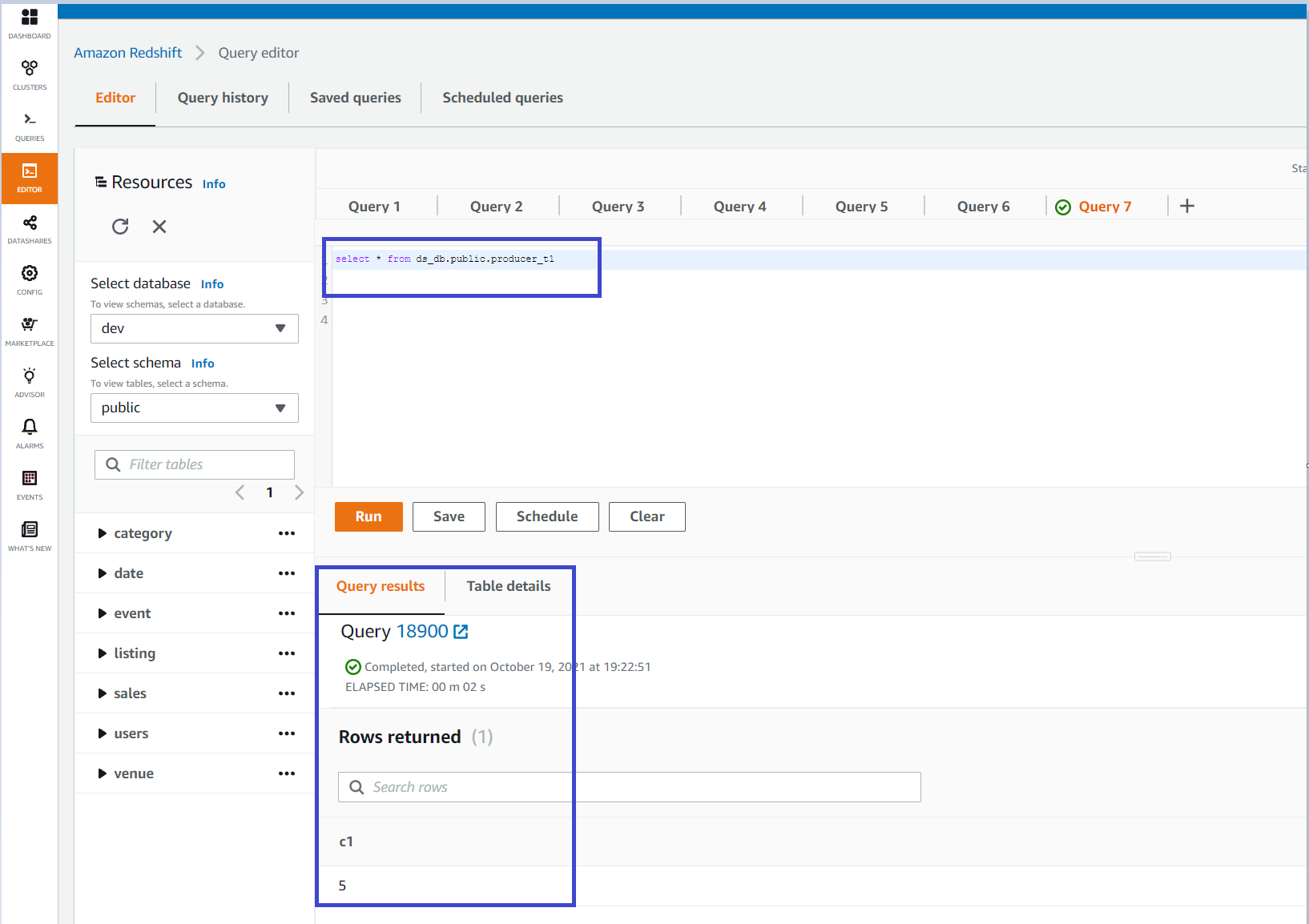
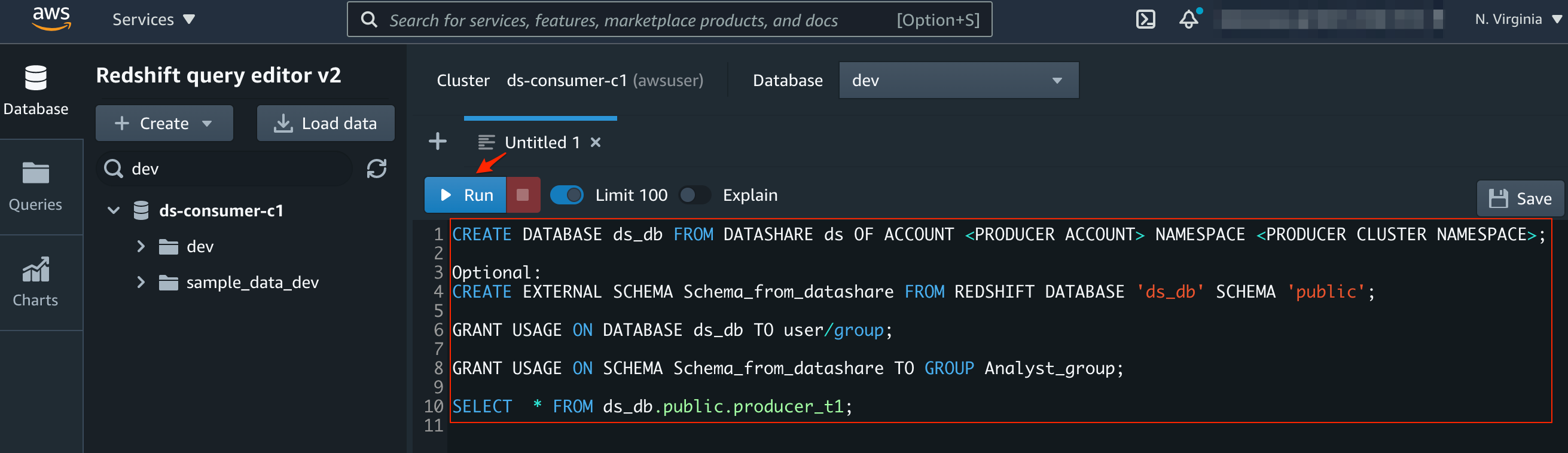
- After associating the Client Redshift cluster 1 to the producer information share, from the Amazon Redshift console within the Client AWS Account, select Question Editor V2 and hook up with the buyer cluster utilizing non permanent credentials.
- After connecting to the buyer cluster, you’ll be able to create a database referencing the information share on the producer cluster, after which begin querying the information.
You need to use the question editor or the brand new Amazon Redshift Question Editor V2 to run the statements above to learn the shared information from the producer by creating an exterior database reference from the buyer cluster.
Conclusion
We have now demonstrated how one can prohibit entry to the information share created on the producer cluster to particular shopper accounts by itemizing authorized accounts within the IAM coverage.
On the buyer facet, we now have additionally demonstrated how one can prohibit entry to a selected Redshift cluster on the buyer account for the information share created on the producer cluster by itemizing authorized Redshift cluster(s) within the IAM coverage. Enterprises and companies can use this strategy to regulate the boundaries of Redshift information sharing at account and cluster granularity.
We encourage you to strive cross-account information sharing with these extra safety controls to securely share information throughout Amazon Redshift clusters each inside your organizations and together with your clients or companions.
Concerning the Authors
 Rajesh Francis is a Senior Analytics Buyer Expertise Specialist at AWS. He makes a speciality of Amazon Redshift and focuses on serving to to drive AWS market and technical technique for information warehousing and analytics. Rajesh works carefully with massive strategic clients to assist them undertake our new providers and options, develop long-term partnerships, and feed buyer necessities again to our product growth groups to information the course of our product choices.
Rajesh Francis is a Senior Analytics Buyer Expertise Specialist at AWS. He makes a speciality of Amazon Redshift and focuses on serving to to drive AWS market and technical technique for information warehousing and analytics. Rajesh works carefully with massive strategic clients to assist them undertake our new providers and options, develop long-term partnerships, and feed buyer necessities again to our product growth groups to information the course of our product choices.
 Kiran Sharma is a Senior Huge Information Marketing consultant for AWS Skilled Companies. She works with our clients to architect and implement Huge Information Options on number of tasks on AWS.
Kiran Sharma is a Senior Huge Information Marketing consultant for AWS Skilled Companies. She works with our clients to architect and implement Huge Information Options on number of tasks on AWS.
 Eric Hotinger is a Software program Engineer at AWS. He enjoys fixing seemingly inconceivable issues within the areas of analytics, streaming, containers, and serverless.
Eric Hotinger is a Software program Engineer at AWS. He enjoys fixing seemingly inconceivable issues within the areas of analytics, streaming, containers, and serverless.
[ad_2]