[ad_1]

Researchers arrange 320 honeypots to see how shortly menace actors would goal uncovered cloud providers and report that 80% of them had been compromised in below 24 hours.
Malicious actors are continuously scanning the Web for uncovered providers that might be exploited to entry inside networks or carry out different malicious exercise.
To trace what software program and providers are focused by menace actors, researchers create publicly accessible honeypots. Honeypots are servers configured to seem as if they’re operating numerous software program as lures to observe menace actors’ techniques.
A tempting lure
In a brand new examine performed by Palo Altos Networks’ Unit 42, researchers arrange 320 honeypots and located that 80% of the honeypots had been compromised throughout the first 24 hours.
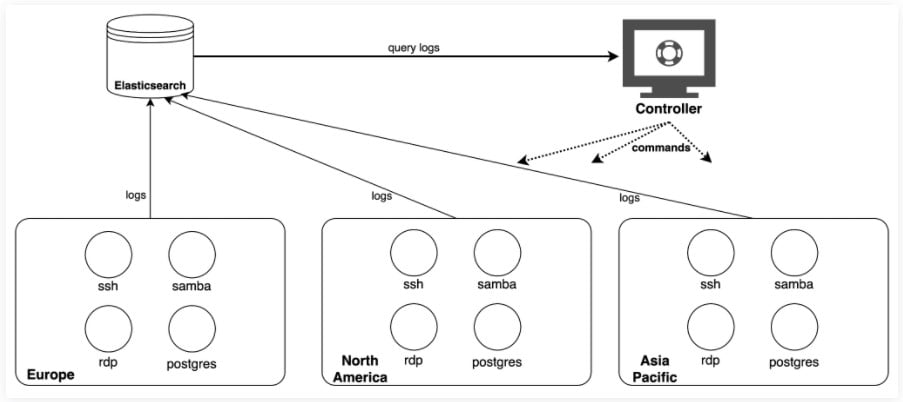
The deployed honeypots included ones with distant desktop protocol (RDP), safe shell protocol (SSH), server message block (SMB), and Postgres database providers and had been stored alive from July to August 2021.
These honeypots had been deployed worldwide, with cases in North America, Asian Pacific, and Europe.
Supply: Unit 42
How attackers transfer
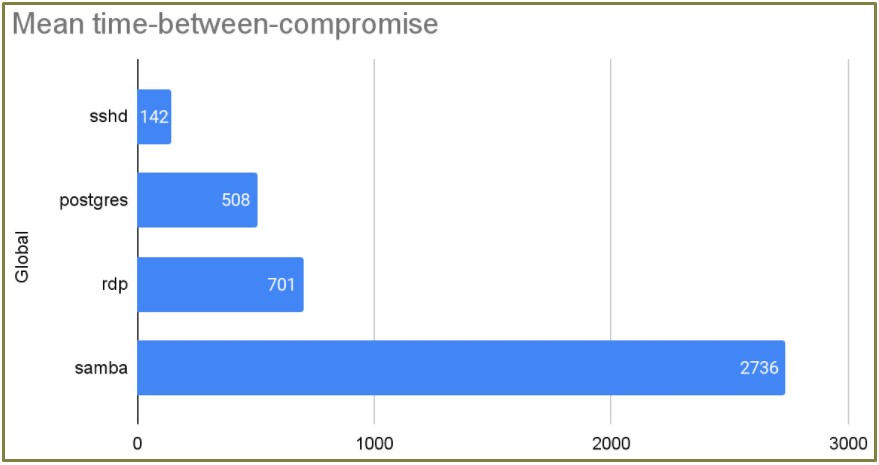
The time to first compromise is analogous to how a lot the service sort is focused.
For SSH honeypots which had been essentially the most focused, the imply time for the primary compromise was three hours, and the imply time between two consecutive assaults was about 2 hours.
Supply: Unit 42
Unit 42 additionally noticed a notable case of a menace actor compromising 96% of the experiment’s 80 Postgres honeypots in simply 30 seconds.
This discovering could be very regarding because it may take days, if not longer, to deploy new safety updates as they’re launched, whereas menace actors simply want hours to use uncovered providers.
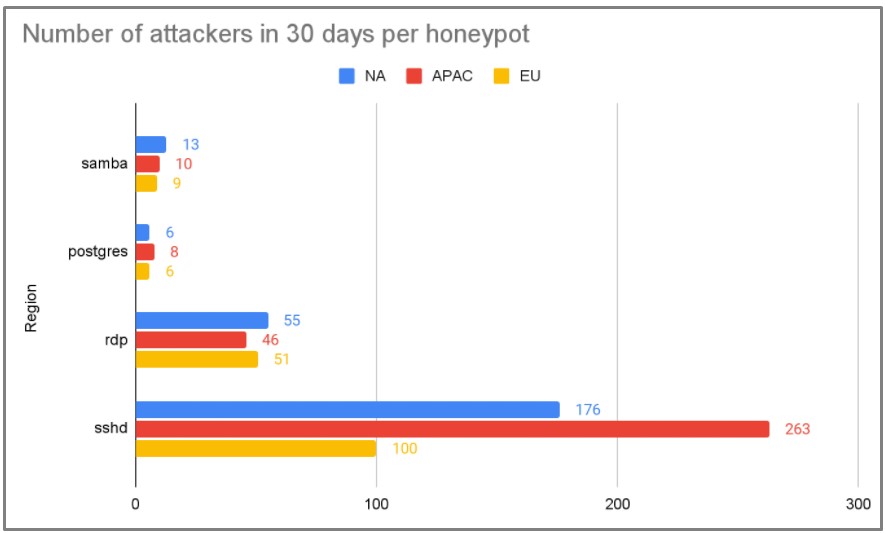
Lastly, relating to whether or not the situation makes any distinction, the APAC area acquired essentially the most consideration from menace actors.
Supply: Unit 42
Do firewalls assist?
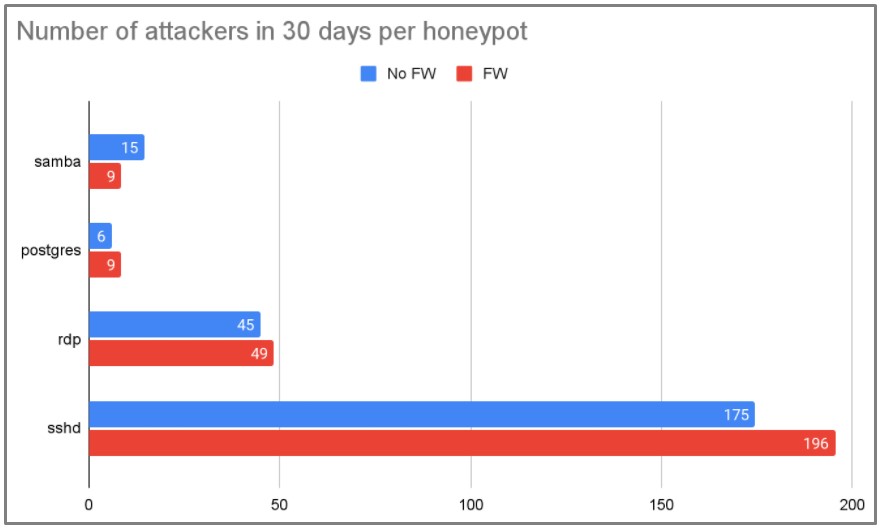
The overwhelming majority (85%) of attacker IPs had been noticed on a single day, which implies that actors hardly ever (15%) reuse the identical IP on subsequent assaults.
This fixed IP change makes ‘layer 3’ firewall guidelines ineffective towards nearly all of menace actors.
What may have higher possibilities of mitigating the assaults is to dam IPs by drawing information from community scanning initiatives which establish tons of of 1000’s of malicious IPs day by day.
Nonetheless, Unit 42 examined this speculation on a sub-group of 48 honeypots and located that blocking over 700,000 IPs had no vital distinction within the variety of assaults between the sub-group and the management group.
Supply: Unit 42
To guard cloud providers successfully, Unit 42 recommends that admins do the next:
- Create a guardrail to forestall privileged ports from being open.
- Create audit guidelines to observe all of the open ports and uncovered providers.
- Create automated response and remediation guidelines to repair misconfigurations mechanically.
- Deploy next-generation firewalls (WFA or VM-Sequence) in entrance of the functions.
Lastly, at all times set up the newest safety updates as they turn into obtainable as menace actors rush to make the most of exploits for brand new vulnerabilities as they’re printed.
[ad_2]

