[ad_1]
4 completely different malicious frameworks designed to assault air-gapped networks had been detected within the first half of 2020 alone, bringing the overall variety of such toolkits to 17 and providing adversaries a pathway to cyber espionage and exfiltrate labeled data.
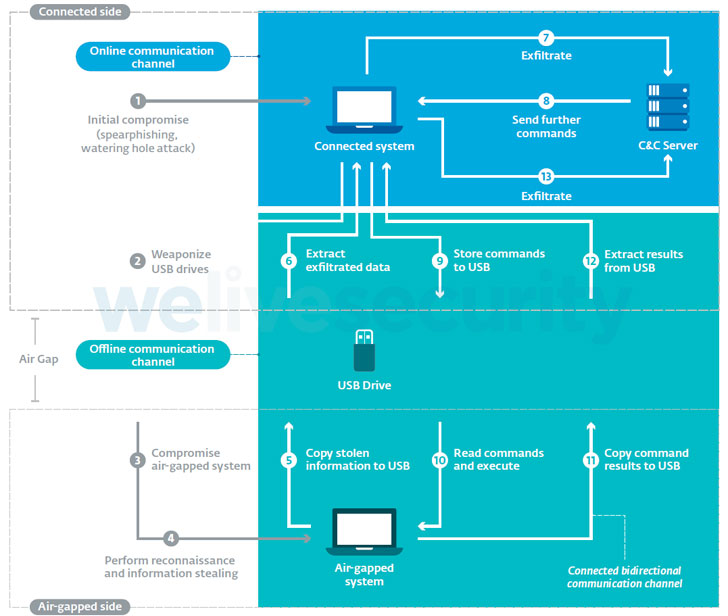
“All frameworks are designed to carry out some type of espionage, [and] all of the frameworks used USB drives because the bodily transmission medium to switch information out and in of the focused air-gapped networks,” ESET researchers Alexis Dorais-Joncas and Facundo Muñoz stated in a complete examine of the frameworks.
Air-gapping is a community safety measure designed to forestall unauthorized entry to programs by bodily isolating them from different unsecured networks, together with native space networks and the general public web. This additionally implies that the one strategy to switch information is by connecting a bodily machine to it, akin to USB drives or exterior onerous disks.
Provided that the mechanism is likely one of the commonest methods SCADA and industrial management programs (ICS) are protected, APT teams which might be sometimes sponsored or a part of nation-state efforts have more and more set their sights on the essential infrastructure in hopes of infiltrating an air-gapped community with malware in order to surveil targets of curiosity.
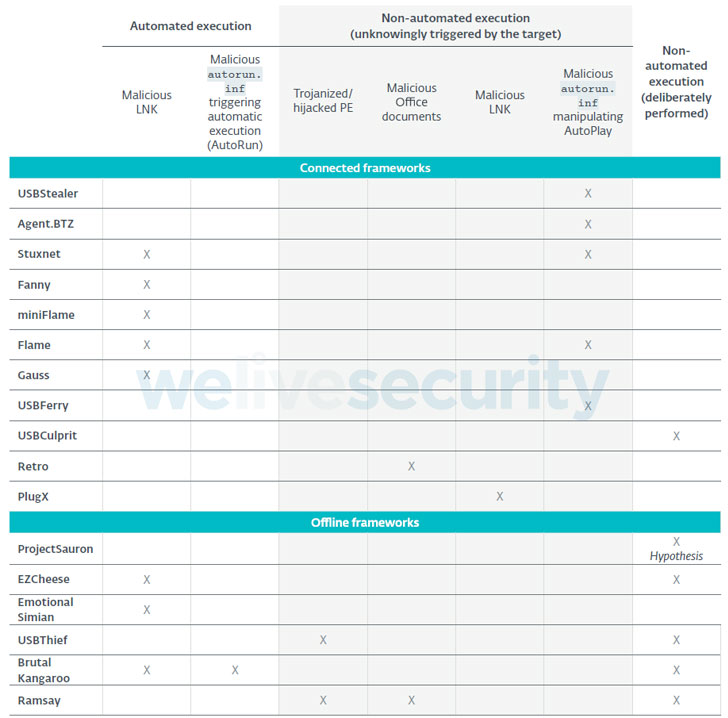
Primarily constructed to assault Home windows-based working programs, the Slovak cybersecurity agency stated that no fewer than 75% of all of the frameworks had been discovered leveraging malicious LNK or AutoRun information on USB drives to both perform the preliminary compromise of the air-gapped system or to maneuver laterally inside the air-gapped community.
Some frameworks which have been attributed to well-known menace actors are as follows —
“All frameworks have devised their very own methods, however all of them have one factor in widespread: with no exception, all of them used weaponized USB drives,” the researchers defined. “The primary distinction between linked and offline frameworks is how the drive is weaponized within the first place.”
Whereas linked frameworks work by deploying a malicious part on the linked system that screens the insertion of recent USB drives and robotically locations the assault code wanted to compromise the air-gapped system, offline frameworks like Brutal Kangaroo, EZCheese, and ProjectSauron depend on the attackers intentionally infecting their very own USB drives to backdoor the focused machine.
As precautions, organizations with essential data programs and delicate data are advisable to forestall direct e-mail entry on linked programs, disable USB ports and sanitize USB drives, limit file execution on detachable drives, and perform periodic evaluation of air-gapped programs for any indicators of suspicious exercise.
“Sustaining a totally air gapped system comes with the advantages of additional safety,” Dorais-Joncas stated. “However identical to all different safety mechanisms, air gapping just isn’t a silver bullet and doesn’t forestall malicious actors from preying on outdated programs or poor worker habits.”
[ad_2]