[ad_1]
A brand new evaluation of web site fingerprinting (WF) assaults aimed on the Tor internet browser has revealed that it is potential for an adversary to glean an internet site frequented by a sufferer, however solely in eventualities the place the risk actor is curious about a selected subset of the web sites visited by customers.
“Whereas assaults can exceed 95% accuracy when monitoring a small set of 5 well-liked web sites, indiscriminate (non-targeted) assaults towards units of 25 and 100 web sites fail to exceed an accuracy of 80% and 60%, respectively,” researchers Giovanni Cherubin, Rob Jansen, and Carmela Troncoso stated in a newly printed paper.
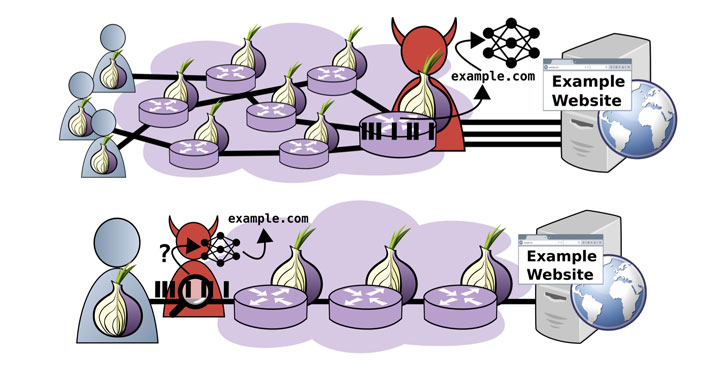
Tor browser provides “unlinkable communication” to its customers by routing web site visitors by means of an overlay community, consisting of greater than six thousand relays, with the purpose of anonymizing the originating location and utilization from third events conducting community surveillance or site visitors evaluation. It achieves this by constructing a circuit that traverses through an entry, center, and exit relay, earlier than forwarding the requests to the vacation spot IP addresses.
On high of that, the requests are encrypted as soon as for every relay to additional hinder evaluation and keep away from data leakage. Whereas the Tor purchasers themselves aren’t nameless with respect to their entry relays, as a result of the site visitors is encrypted and the requests soar by means of a number of hops, the entry relays can not determine the purchasers’ vacation spot, simply because the exit nodes can not discern a consumer for a similar purpose.
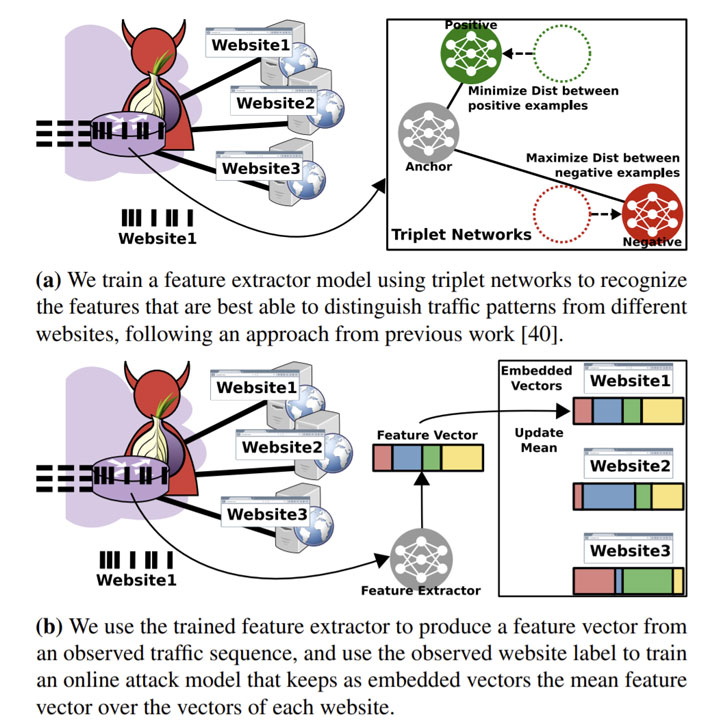
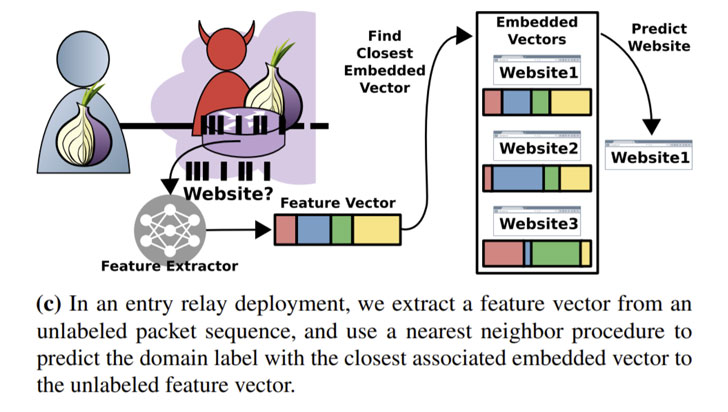
Web site fingerprinting assaults on Tor intention to interrupt these anonymity protections and allow an adversary observing the encrypted site visitors patterns between a sufferer and the Tor community to foretell the web site visited by the sufferer. The risk mannequin devised by the teachers presupposes an attacker operating an exit node — in order to seize the range of site visitors generated by actual customers — which is then used as a supply to gather Tor site visitors traces and devise a machine-learning-based classification mannequin atop the gathered data to deduce customers’ web site visits.
The adversary mannequin includes an “on-line coaching section that makes use of observations of real Tor site visitors collected from an exit relay (or relays) to constantly replace the classification mannequin over time,” defined the researchers, who ran entry and exit relays for every week in July 2020 utilizing a customized model of Tor v0.4.3.5 to extract the related exit data.
To mitigate any moral and privateness considerations arising out of the examine, the paper’s authors careworn the security precautions integrated to stop leakage of delicate web sites that customers might go to through the Tor browser.
“The outcomes of our real-world analysis show that WF assaults can solely achieve success within the wild if the adversary goals to determine web sites inside a small set,” the researchers concluded. “In different phrases, untargetted adversaries that intention to usually monitor customers’ web site visits will fail, however centered adversaries that concentrate on one explicit consumer configuration and web site might succeed.”
[ad_2]