[ad_1]

Microsoft is warning of harmful data-wiping malware disguised as ransomware being utilized in assaults towards a number of organizations in Ukraine.
Beginning January thirteenth, Microsoft detected the brand new assaults that mixed a harmful MBRLocker with a data-corrupting malware used to destroy the sufferer’s knowledge deliberately.
A two-stage assault destroys knowledge
Microsoft calls this new malware household ‘WhisperGate’ and explains in a report that it’s performed by way of two completely different harmful malware elements.
The primary part, named stage1.exe, is launched from the C:PerfLogs, C:ProgramData, C:, or C:temp folders that overwrites the Grasp Boot Document to show a ransom observe.
An MBR locker is a program that replaces the ‘grasp boot document,’ a location on a pc’s exhausting drive that incorporates info on disk partitions and a small executable that’s used to load the working system.
MBR lockers change the loader within the grasp boot document with a program that generally encrypts the partition desk and shows a ransom observe. This prevents the working system from loading and knowledge from being accessible till a ransom is paid and a decryption secret’s obtained.
The WhisperGate ransom observe, proven beneath, tells the sufferer to ship $10,000 in bitcoin to the 1AVNM68gj6PGPFcJuftKATa4WLnzg8fpfv handle after which contact the risk actors through an included Tox chat ID.
Your exhausting drive has been corrupted.
In case you need to get well all exhausting drives
of your group,
You need to pay us $10k through bitcoin pockets
1AVNM68gj6PGPFcJuftKATa4WLnzg8fpfv and ship message through
tox ID 8BEDC411012A33BA34F49130D0F186993C6A32DAD8976F6A5D82C1ED23054C057ECED5496F65
along with your group identify.
We are going to contact you to offer additional directions.Whereas Microsoft factors to the usage of Tox as a purpose for the ransomware being faux, BleepingComputer is aware of of quite a few ransomware operations that use Tox as a communication technique, so this isn’t uncommon.
Nevertheless, the MBRLocker’s ransom observe makes use of the identical bitcoin handle for all victims and doesn’t present a way to enter a decryption key. When mixed, this sometimes signifies faux ransomware designed for harmful functions.
The second part, named stage2.exe, is executed concurrently to obtain a data-destroying malware named Tbopbh.jpg hosted on Discord that overwrites focused recordsdata with static knowledge.
“If a file carries one of many extensions above, the corrupter overwrites the contents of the file with a hard and fast variety of 0xCC bytes (whole file dimension of 1MB),” explains Microsoft’s report.
“After overwriting the contents, the destructor renames every file with a seemingly random four-byte extension.”
The file extensions focused by the stage2 part for corruption are:
.3DM .3DS .7Z .ACCDB .AI .ARC .ASC .ASM .ASP .ASPX .BACKUP .BAK .BAT .BMP .BRD .BZ .BZ2 .CGM .CLASS .CMD .CONFIG .CPP .CRT .CS .CSR .CSV .DB .DBF .DCH .DER .DIF .DIP .DJVU.SH .DOC .DOCB .DOCM .DOCX .DOT .DOTM .DOTX .DWG .EDB .EML .FRM .GIF .GO .GZ .HDD .HTM .HTML .HWP .IBD .INC .INI .ISO .JAR .JAVA .JPEG .JPG .JS .JSP .KDBX .KEY .LAY .LAY6 .LDF .LOG .MAX .MDB .MDF .MML .MSG .MYD .MYI .NEF .NVRAM .ODB .ODG .ODP .ODS .ODT .OGG .ONETOC2 .OST .OTG .OTP .OTS .OTT .P12 .PAQ .PAS .PDF .PEM .PFX .PHP .PHP3 .PHP4 .PHP5 .PHP6 .PHP7 .PHPS .PHTML .PL .PNG .POT .POTM .POTX .PPAM .PPK .PPS .PPSM .PPSX .PPT .PPTM .PPTX .PS1 .PSD .PST .PY .RAR .RAW .RB .RTF .SAV .SCH .SHTML .SLDM .SLDX .SLK .SLN .SNT .SQ3 .SQL .SQLITE3 .SQLITEDB .STC .STD .STI .STW .SUO .SVG .SXC .SXD .SXI .SXM .SXW .TAR .TBK .TGZ .TIF .TIFF .TXT .UOP .UOT .VB .VBS .VCD .VDI .VHD .VMDK .VMEM .VMSD .VMSN .VMSS .VMTM .VMTX .VMX .VMXF .VSD .VSDX .VSWP .WAR .WB2 .WK1 .WKS .XHTML .XLC .XLM .XLS .XLSB .XLSM .XLSX .XLT .XLTM .XLTX .XLW .YML .ZIPAs neither of the 2 malware elements provide means to enter decryption keys to revive the unique Grasp Boot Document and because the recordsdata are overwritten with static undecryptable knowledge, Microsoft classifies this as a harmful assault somewhat than one used to generate a ransom cost.
Indicators of compromise and obtain hyperlinks for the malware samples will be discovered within the IOC part later within the article.
Microsoft is unable to attribute the assaults to any explicit risk actor and is monitoring the hacker’s actions as DEV-0586.
With the geopolitical tensions escalating within the area between Russia and Ukraine, it’s believed that these assaults are designed to sow chaos in Ukraine.
An identical assault was performed in 2017 when hundreds of Ukrainian companies had been focused with the NotPetya ransomware.
Whereas NotPetya was based mostly on actual ransomware referred to as Petya, the NotPetya assaults had been performed as a cyberweapon towards Ukraine somewhat than to generate funds.
In 2020, the USA formally indicted Russian GRU hackers believed to be a part of the elite Russian hacking group referred to as “Sandworm” for the NotPetya assaults.
Ukraine below siege by cyberattacks
This week, at the very least fifteen web sites of Ukrainian public establishments and authorities businesses had been hacked, defaced, and subsequently taken offline.
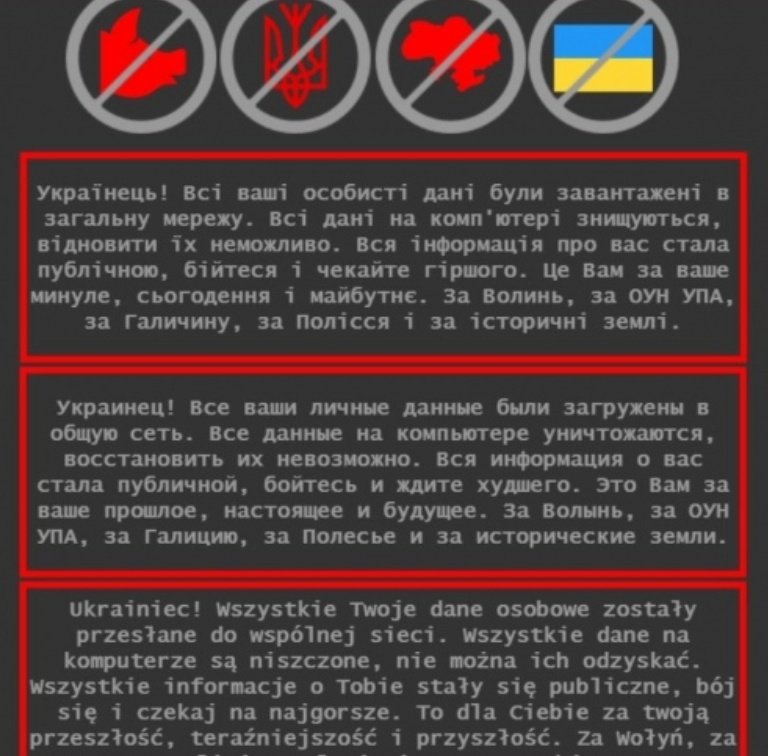
Hackers defaced these web sites to point out a message warning guests that their knowledge was stolen and publicly shared on-line.
“Ukrainian! All of your private knowledge has been uploaded to the general public community. All knowledge on the pc is destroyed, it’s unimaginable to get well them. All details about you has turn into public, be afraid and anticipate the worst. That is in your previous, current and future. For Volyn, for the OUN UPA, for Galicia, for Polissya and for historic lands,” reads the translated web site defacement.
As a part of this intimidation marketing campaign, the risk actors created new accounts on the favored RaidForums hacking discussion board to launch the allegedly stolen knowledge.
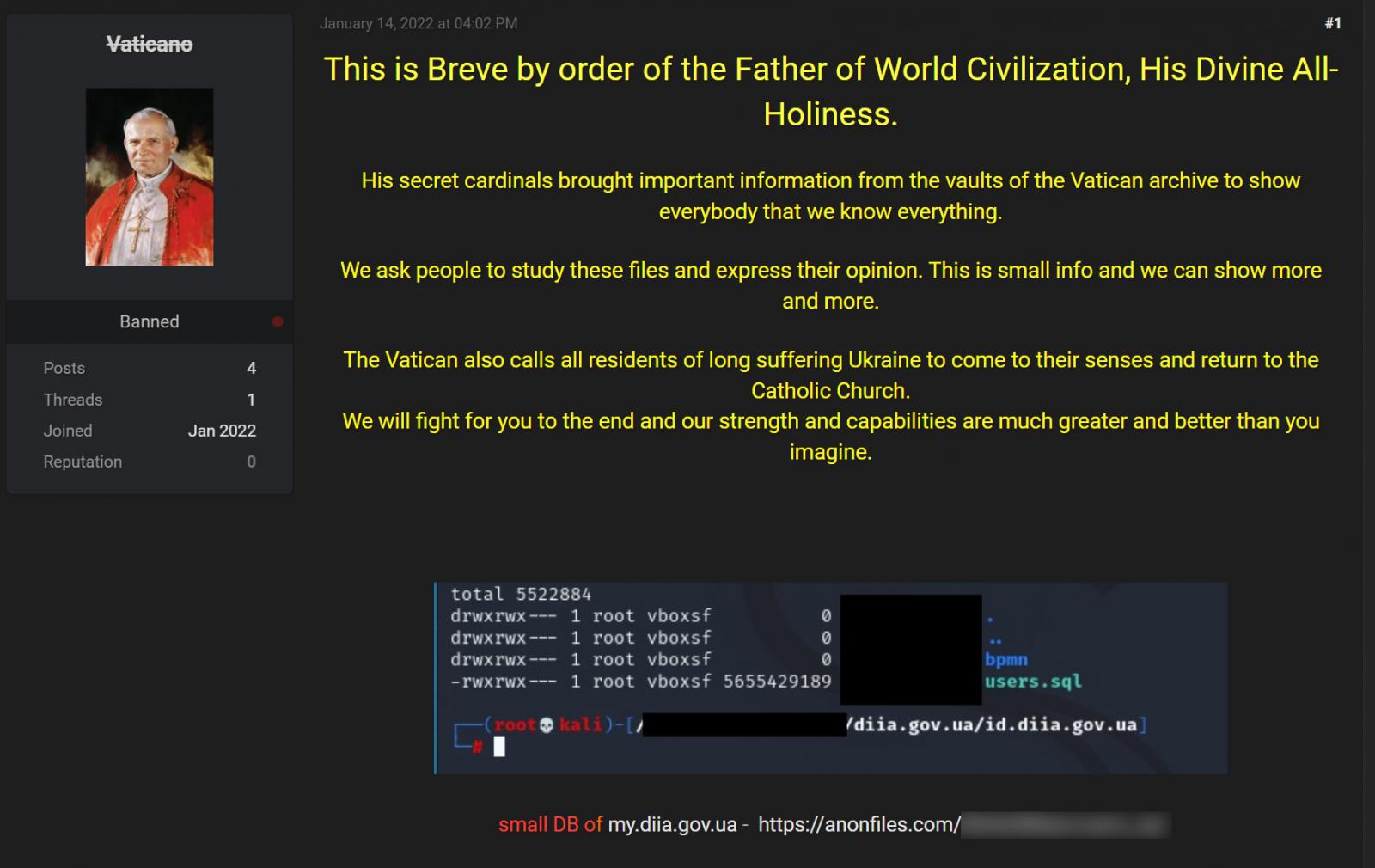
Nevertheless, risk actors who’ve reviewed the printed knowledge say it’s unrelated to Ukraine authorities businesses and incorporates knowledge from an outdated leak.
Ukraine has attributed the assaults to Russia, with the purpose of undermining the arrogance within the Ukrainian authorities.
“Russia’s cyber-troops are sometimes working towards america and Ukraine, attempting to make use of know-how to shake up the political scenario. The most recent cyber assault is likely one of the manifestations of Russia’s hybrid conflict towards Ukraine, which has been occurring since 2014,” the Ukraine authorities introduced right now.
“Its purpose shouldn’t be solely to intimidate society. And to destabilize the scenario in Ukraine by stopping the work of the general public sector and undermining the arrogance within the authorities on the a part of Ukrainians. They’ll obtain this by throwing fakes into the infospace in regards to the vulnerability of essential info infrastructure and the “drain” of non-public knowledge of Ukrainians.”
IOCs
Stage1.exe:
a196c6b8ffcb97ffb276d04f354696e2391311db3841ae16c8c9f56f36a38e92 [VirusTotal] [MalShare]
Stage2.exe:
dcbbae5a1c61dbbbb7dcd6dc5dd1eb1169f5329958d38b58c3fd9384081c9b78 [VirusTotal] [MalShare]
Tbopbh.jpg (third stage):
923eb77b3c9e11d6c56052318c119c1a22d11ab71675e6b95d05eeb73d1accd6 [VirusTotal] [MalShare]
Replace 1/16/22: Added obtain hyperlinks for malware samples.
[ad_2]
