[ad_1]
An ongoing crypto mining marketing campaign has upgraded its arsenal whereas including new protection evasion techniques that allow the risk actors to hide the intrusions and fly beneath the radar, new analysis printed right this moment has revealed.
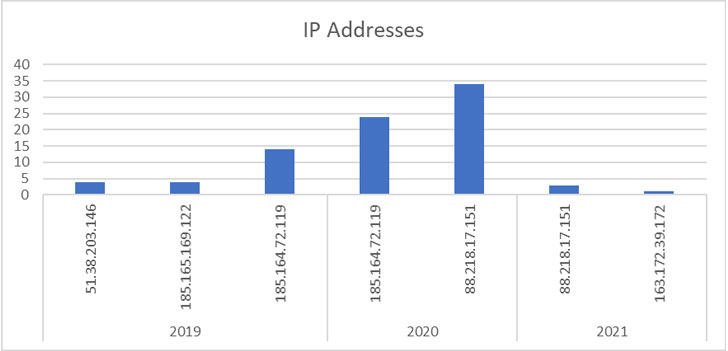
Since first detected in 2019, a complete of 84 assaults towards its honeypot servers have been recorded thus far, 4 of which transpired in 2021, in keeping with researchers from DevSecOps and cloud safety agency Aqua Safety, who’ve been monitoring the malware operation for the previous three years. That mentioned, 125 assaults have been noticed within the wild within the third quarter of 2021 alone, signaling that the assaults haven’t slowed down.
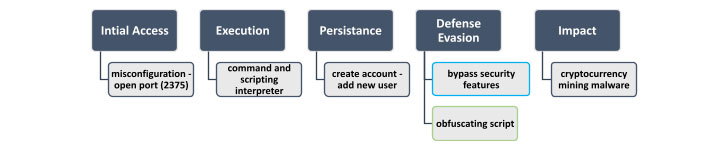
Preliminary assaults concerned executing a malicious command upon operating a vanilla picture named “alpine:newest” that resulted within the obtain of a shell script named “autom.sh.”
“Adversaries generally use vanilla photos together with malicious instructions to carry out their assaults, as a result of most organizations belief the official photos and permit their use,” the researchers mentioned in a report shared with The Hacker Information. “Over time, the malicious command that was added to the official picture to hold out the assault has barely modified. The primary distinction is the server from which the shell script autom.sh was downloaded.”
The shell script initiates the assault sequence, enabling the adversary to create a brand new consumer account beneath the identify “akay” and improve its privileges to a root consumer, utilizing which arbitrary instructions are run on the compromised machine with the purpose of mining cryptocurrency.
Whereas early phases of the marketing campaign in 2019 featured no particular methods to cover the mining exercise, later variations present the intense measures its builders have taken to maintain it invisible to detection and inspection, chief amongst them being the flexibility to disable safety mechanisms and retrieve an obfuscated mining shell script that was Base64-encoded 5 occasions to get round safety instruments.
Malware campaigns carried out to hijack computer systems to mine cryptocurrencies have been dominated by a number of risk actors comparable to Kinsing, which has been discovered scanning the web for misconfigured Docker servers to interrupt into the unprotected hosts and set up a beforehand undocumented coin miner pressure.
On high of that, a hacking group named TeamTNT has been noticed putting unsecured Redis database servers, Alibaba Elastic Computing Service (ECS) cases, uncovered Docker APIs, and susceptible Kubernetes clusters with a purpose to execute malicious code with root privileges on the focused hosts in addition to deploy cryptocurrency-mining payloads and credential stealers. As well as, compromised Docker Hub accounts have additionally been employed to host malicious photos that have been then used to distribute cryptocurrency miners.
In latest weeks, safety flaws within the Log4j logging library in addition to vulnerabilities not too long ago uncovered in Atlassian Confluence, F5 BIG-IP, VMware vCenter, and Oracle WebLogic Servers have been abused to take over machines to mine cryptocurrencies, a scheme often called cryptojacking. Earlier this month, network-attached storage (NAS) equipment maker QNAP warned of cryptocurrency mining malware concentrating on its gadgets that would occupy round 50% of the overall CPU utilization.
“Miners are a low-risk means for cybercriminals to show a vulnerability into digital money, with the best danger to their money movement being competing miners discovering the identical susceptible servers,” Sophos senior risk researcher Sean Gallagher famous in an evaluation of a Tor2Mine mining marketing campaign, which includes using a PowerShell script to disable malware safety, execute a miner payload, and harvest Home windows credentials.
“The Autom marketing campaign illustrates that attackers have gotten extra refined, frequently enhancing their methods and their potential to keep away from detection by safety options,” the researchers mentioned. To guard towards these threats, it is beneficial to watch suspicious container exercise, carry out dynamic picture evaluation, and routinely scan the environments for misconfiguration points.
[ad_2]