[ad_1]
The variety of malicious dormant domains is on the rise, and as researchers warn, roughly 22.3% of strategically aged domains pose some type of hazard.
This was a realization that struck analysts when it was revealed that the SolarWinds menace actors relied on domains registered years earlier than their malicious actions started.
Primarily based on that, efforts in detecting strategically aged domains earlier than they get the prospect to launch assaults and help malicious actions have picked up tempo.
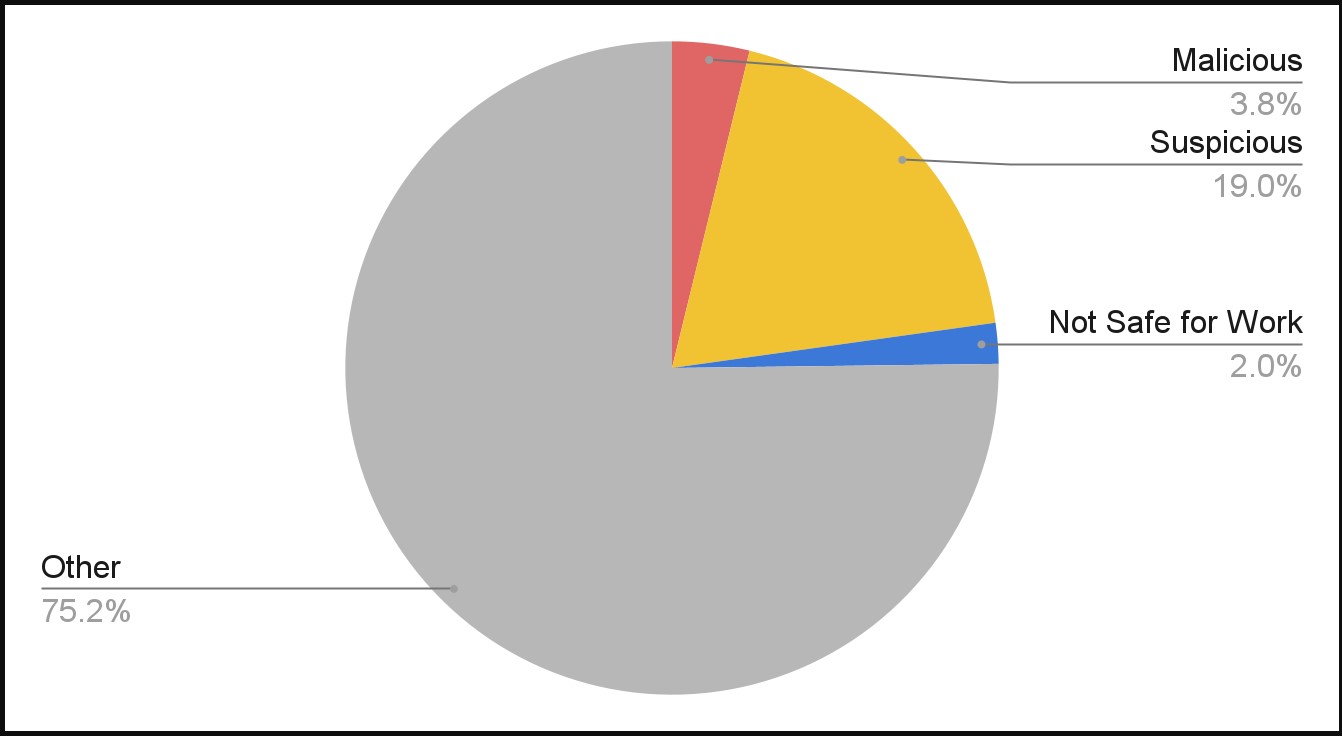
A report from Palo Alto Networks’ Unit42 reveals their researchers’ findings after taking a look at tens of hundreds of domains every day all through September 2021.
They concluded that roughly 3.8% are straight-out malicious, 19% are suspicious, and a pair of% are unsafe for work environments.
Supply: Unit42
Why let a site age
The aim behind registering a site lengthy earlier than the menace actors will use it’s to create a “clear report” that can stop safety detection programs from undermining the success of malicious campaigns.
Usually, newly registered domains (NRDs) are extra prone to be malicious, so safety options deal with them as suspicious and have extra possibilities to flag them.
Nevertheless, Unit42 explains in its report that strategically aged domains are thrice extra prone to be malicious than NRDs.
In some circumstances, these domains stayed dormant for 2 years earlier than their DNS site visitors out of the blue elevated by 165 occasions, indicating the launch of an assault.
Indicators of “snake eggs”
An apparent signal of a malicious area is the sudden spike in its site visitors. Authentic companies that registered their domains and launched companies months or years later exhibit gradual site visitors progress.
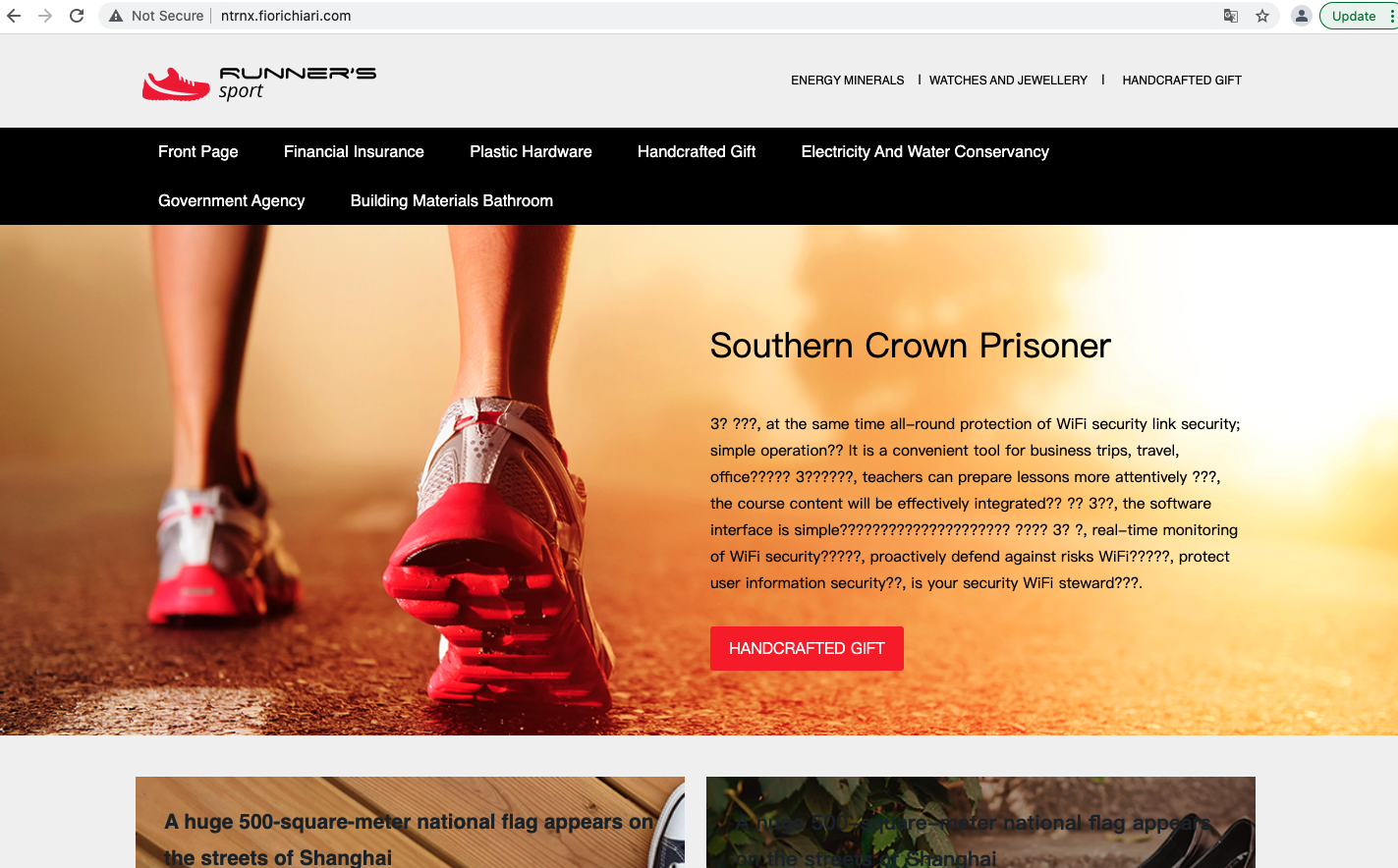
The domains that weren’t destined for reliable use usually have incomplete, cloned, or usually questionable content material. As anticipated, WHOIS registrant particulars are lacking too.
Supply: Unit42
One other clear signal of a purposefully aged area that’s meant for use in malicious campaigns is DGA subdomain technology.
DGA (area technology algorithm) is a longtime technique of producing distinctive domains and IP addresses to function new C2 communication factors. The aim is to evade detection and blocklists.
By trying on the DGA component alone, Palo Alto’s detectors recognized two suspicious domains every day, spawning tons of of hundreds of subdomains on the day of its activation.
Actual examples
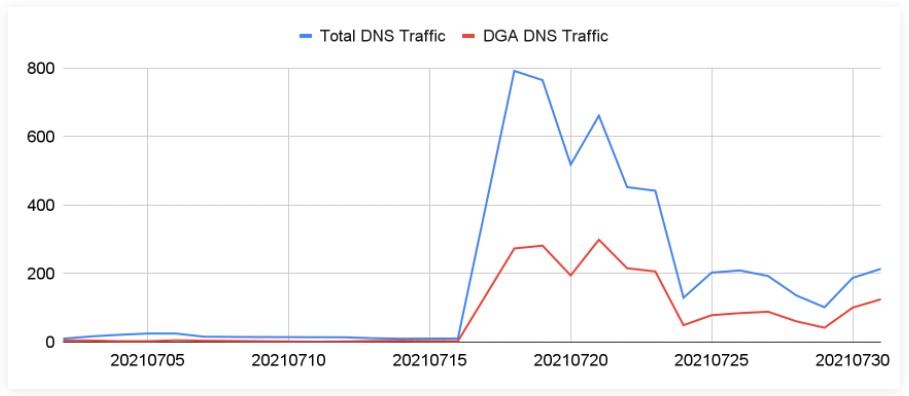
One notable case captured by Unit42 in September was a Pegasus spying marketing campaign that used two C2 domains registered in 2019 and awoke in July 2021.
DGA domains performed a significant function in that marketing campaign, carrying 23.22% of the site visitors on the activation day, which spiked 56 occasions increased than regular DNS site visitors volumes. Just a few days later, DGA site visitors reached 42.04% of the entire.
Supply: Unit42
Different real-world examples detected by the researchers embrace phishing campaigns that used DGA subdomains as cloaking layers that can direct ineligible guests and crawlers to reliable websites whereas pushing victims to the phishing pages.
This reveals that these DGAs serve not solely as C2 domains but in addition as proxy layers that may be explicitly configured to the marketing campaign’s wants.
Lastly, there have been additionally circumstances of wildcard DNS abuse, with a number of subdomains all pointing to the identical IP deal with.
“These hostnames serve randomly generated web sites that fill out some web site templates with random strings,” particulars the Unit42 report.
“They might be used for black hat search engine marketing. Particularly, these internet pages hyperlink to one another to acquire a excessive rank from search engine crawlers with out offering beneficial info.”
Normally, strategically aged domains are utilized by subtle actors who function in a extra organized context and have long-term plans.
They’re used for leveraging DGA to exfiltrate information by DNS site visitors, function proxy layers, or mimic the domains of well-known manufacturers (cybersquatting).
Though detecting DGA exercise continues to be difficult, defenders can obtain rather a lot by monitoring DNS information like queries, responses, and IP addresses and specializing in figuring out patterns.
[ad_2]
