[ad_1]
A beforehand unknown rootkit has been discovered setting its sights on Hewlett-Packard Enterprise’s Built-in Lights-Out (iLO) server administration know-how to hold out in-the-wild assaults that tamper with the firmware modules and fully wipe knowledge off the contaminated methods.
The invention, which is the primary occasion of real-world malware in iLO firmware, was documented by Iranian cybersecurity agency Amnpardaz this week.
“There are quite a few points of iLO that make it a great utopia for malware and APT teams: Extraordinarily excessive privileges (above any stage of entry within the working system), very low-level entry to the {hardware}, being completely out of the sight of the admins, and safety instruments, the overall lack of know-how and instruments for inspecting iLO and/or defending it, the persistence it offers for the malware to stay even after altering the working system, and specifically being all the time operating and by no means shutting down,” the researchers stated.
Moreover managing the servers, the truth that iLO modules have broad entry to all of the firmware, {hardware}, software program, and working system (OS) put in on the servers make them a great candidate to breach organizations utilizing HP servers, whereas additionally enabling the malware to keep up persistence after reboots and survive OS reinstallations. Nonetheless, the precise modus operandi used to infiltrate the community infrastructure and deploy the wiper stays unknown as but.
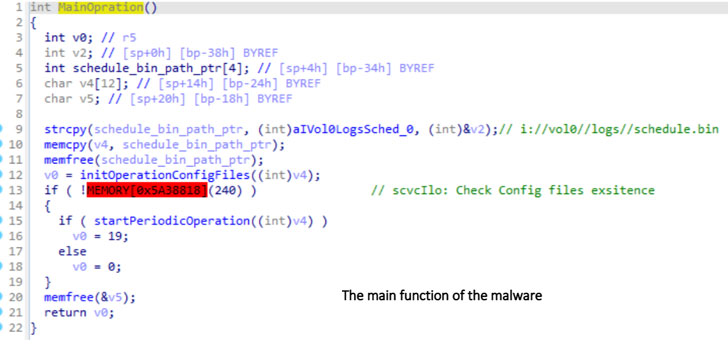
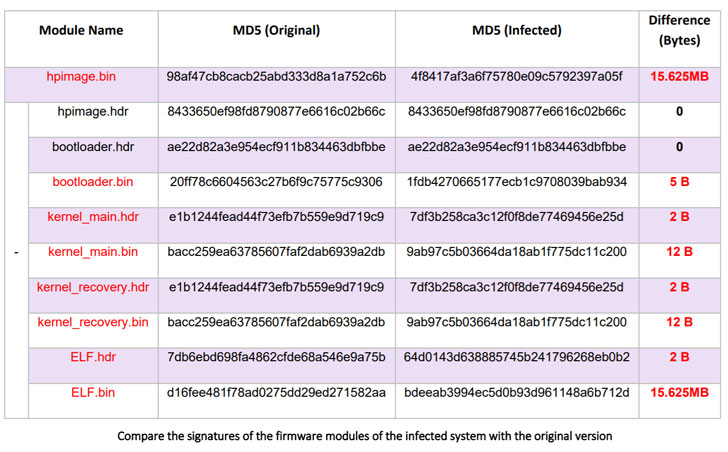
Dubbed iLOBleed, the rootkit has been put to make use of in assaults since 2020 with the aim of manipulating various authentic firmware modules so as to stealthily impede updates to the firmware. Particularly, the modifications made to the firmware routine simulates the firmware improve course of — by purportedly displaying the fitting firmware model and including related logs — when in actuality no updates are carried out.
“This alone exhibits that the aim of this malware is to be a rootkit with most stealth and to cover from all safety inspections,” the researchers stated. “A malware that, by hiding in one of the crucial highly effective processing sources (which is all the time on), is ready to execute any instructions obtained from an attacker, with out ever being detected.”
Though the adversary stays unidentified, Amnpardaz described the rootkit as seemingly the work of a sophisticated persistent menace (APT), a designation a nation-state or state-sponsored group that employs steady, clandestine, and complex hacking strategies to realize unauthorized entry to a system and stay inside for a chronic time frame with out attracting consideration.
If something, the event as soon as once more brings firmware safety into sharp focus, necessitating that firmware updates shipped by the producer are promptly utilized to mitigate potential dangers, iLO networks are segmented from the working networks, and that the firmware is periodically monitored for indicators of an infection.
“One other vital level is that there are strategies to entry and infect iLO each via the community and thru the host working system,” the researchers famous. “Which means that even when the iLO community cable is totally disconnected, there may be nonetheless the potential of an infection with the malware. Apparently, there is no such thing as a option to flip off or disable iLO fully in case it’s not wanted.”
[ad_2]