[ad_1]
Microsoft on Monday introduced the seizure of 42 domains utilized by a China-based cyber espionage group that set its sights on organizations within the U.S. and 28 different nations pursuant to a authorized warrant issued by a federal courtroom within the U.S. state of Virginia.
The Redmond firm attributed the malicious actions to a bunch it pursues as Nickel, and by the broader cybersecurity trade underneath the monikers APT15, Bronze Palace, Ke3Chang, Mirage, Playful Dragon, and Vixen Panda. The superior persistent menace (APT) actor is believed to have been energetic since not less than 2012.
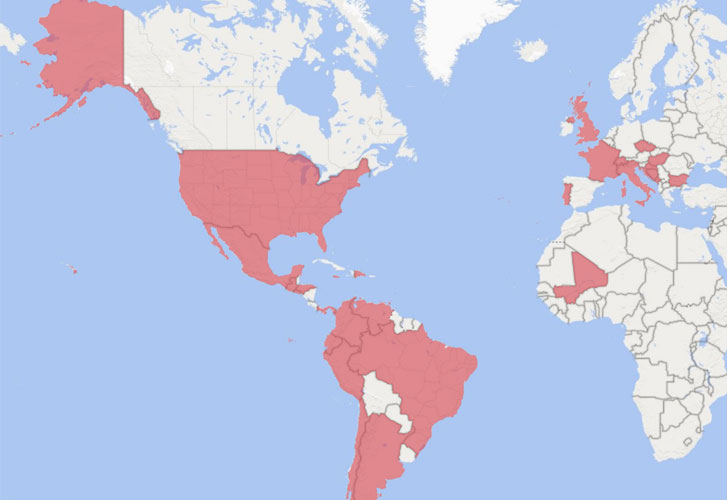
“Nickel has focused organizations in each the non-public and public sectors, together with diplomatic organizations and ministries of overseas affairs in North America, Central America, South America, the Caribbean, Europe and Africa,” Microsoft’s Company Vice President for Buyer Safety and Belief, Tom Burt, stated. “There may be usually a correlation between Nickel’s targets and China’s geopolitical pursuits.”
The rogue infrastructure enabled the hacking crew to take care of long-term entry to the compromised machines and execute assaults for intelligence gathering functions focusing on unnamed authorities businesses, suppose tanks, and human rights organizations as a part of a digital espionage marketing campaign courting again to September 2019.
Microsoft painted the cyber assaults as “extremely refined” that used a large number of strategies, together with breaching distant entry companies and exploiting vulnerabilities in unpatched VPN home equipment in addition to Trade Server and SharePoint techniques to “insert hard-to-detect malware that facilitates intrusion, surveillance and information theft.”
Upon gaining an preliminary foothold, Nickel has been discovered deploying credential dumping instruments and stealers similar to Mimikatz and WDigest to hack into sufferer accounts, adopted by delivering customized malware that allowed the actor to take care of persistence on sufferer networks over prolonged intervals of time and conduct repeatedly scheduled exfiltration of recordsdata, execute arbitrary shellcode, and acquire emails from Microsoft 365 accounts utilizing compromised credentials.
The a number of backdoor households used for command and management are being tracked as Neoichor, Leeson, NumbIdea, NullItch, and Rokum.
The most recent wave of assaults provides to an intensive listing of surveillanceware campaigns mounted by the APT15 group lately. In July 2020, cell safety agency Lookout disclosed 4 trojanized official apps — named SilkBean, DoubleAgent, CarbonSteal, and GoldenEagle — that focused the Uyghur ethnic minority and the Tibetan neighborhood with the aim of gathering and transmitting private person information to adversary-operated command-and-control servers.
“As China’s affect around the globe continues to develop and the nation establishes bilateral relations with extra nations and extends partnerships in assist of China’s Belt and Highway Initiative, we assess that China-based menace actors will proceed to focus on clients in authorities, diplomatic, and NGO sectors to realize new insights, seemingly in pursuit of financial espionage or conventional intelligence assortment goals,” Microsoft stated.
[ad_2]