[ad_1]

Microsoft Defender for Endpoint is presently blocking Workplace paperwork from being opened and a few executables from launching on account of a false optimistic tagging the recordsdata as probably bundling an Emotet malware payload.
Home windows system admins are reporting [1, 2, 3, 4, 5] that that is occurring since updating Microsoft’s enterprise endpoint safety platform (beforehand referred to as Microsoft Defender ATP) definitions to model 1.353.1874.0.
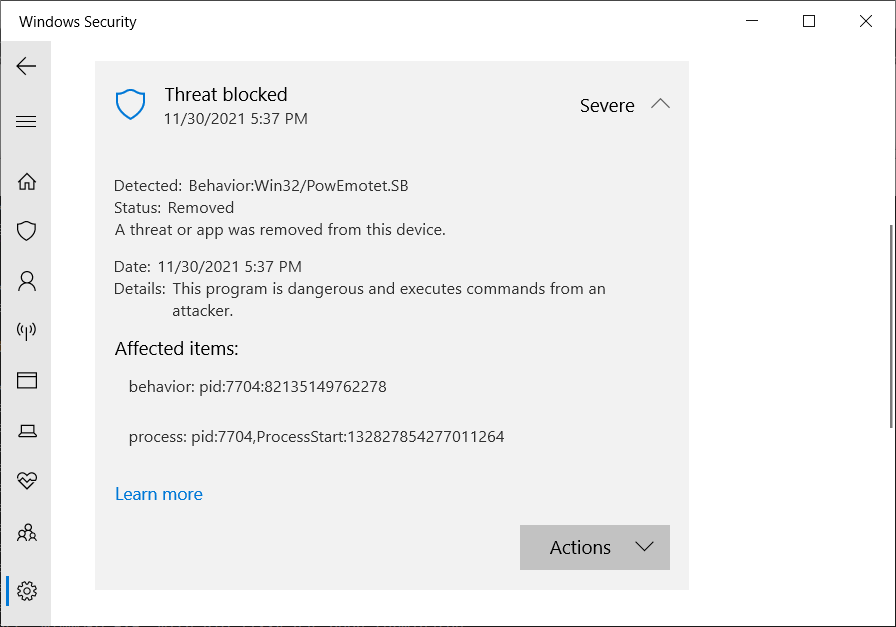
When triggered, Defender for Endpoint will block the file from opening and throw an error mentioning suspicious exercise linked to Win32/PowEmotet.SB or Win32/PowEmotet.SC.
“We’re seeing points with definition replace 1.353.1874.0 detecting printing as Win32/PowEmotet.SB this afternoon,” one admin mentioned.
“We’re seeing this detected for Excel, any Workplace app utilizing MSIP.ExecutionHost.exe ( AIP Sensitivity Shopper ) and splwow64.exe,” one other added.
A 3rd one confirmed the problems with as we speak’s definition updates: “We’re seeing the identical habits particularly with v.1.353.1874.0 of the definitions, which was launched as we speak, & included a definition for Habits:Win32/PowEmotet.SB & Habits:Win32/PowEmotet.SC.”
Whereas Microsoft hasn’t but shared any information on what causes this, the most probably cause is that the corporate has elevated the sensitivity for detecting Emotet-like habits in updates launched as we speak, which makes Defender’s generic behavioral detection engine too delicate susceptible to false positives.
The change was seemingly prompted by the latest revival of the Emotet botnet from two weeks in the past, after Emotet analysis group Cryptolaemus, GData, and Superior Intel started seeing TrickBot dropping Emotet loaders on contaminated units.
Though that is nearly certainly not the true factor, the timing is certainly unlucky with Emotet coming again and most Home windows admins already on their toes.
As a few of them have reported, they nearly took their knowledge facilities offline to cease a potential Emotet an infection from spreading earlier than realizing that what they had been seeing had been seemingly false positives.
Since October 2020, Home windows admins needed to cope with different Defender for Endpoint together with one which confirmed community units contaminated with Cobalt Strike and one other that marked Chrome updates as PHP backdoors.
BleepingComputer has reached out to Microsoft for extra data and to substantiate that this behavioral detection concern triggers a false optimistic however has not heard again.
[ad_2]
