[ad_1]
Current high-profile cybersecurity incidents such because the SolarWinds assault and the Apache Log4j vulnerability have uncovered the threats related to the software program provide chain. These can vary from pretty easy exploits of recognized vulnerabilities to very subtle assaults, sponsored by nation-state actors.
The annual spending on enterprise software program — often known as industrial off-the-shelf or COTS software program — is now approaching $600 billion with a progress price of 11.5%. But, given the magnitude of this funding, enterprises are spending a pittance on securing their software program provide chain. That is what makes COTS software program so harmful — vulnerabilities could be “hidden” in open supply elements. Nevertheless, there’s a repair for this in a software program invoice of supplies (SBOM).
Enhancing COTS Safety Posture
Historically, enterprises have trusted that software program distributors are performing the mandatory safety due diligence, following accepted software program engineering greatest practices, and disclosing the safety practices for supporting their software program. Clients, however, are left to analyze the safety of the merchandise they use by associations or person teams to share details about vendor danger and software program safety.
These approaches are clearly not sufficient as proven by the Apache Log4j vulnerability. Regardless of one of the best intentions of software program distributors, too many safety vulnerabilities are lurking in open supply elements used to construct COTS software program. This represents a software program safety blind spot that the distributors themselves could not even learn about. The important thing artifact wanted to make clear this blind spot is the SBOM.
The SBOM is a listing report of the software program elements that make up a software program product — just just like the labels on meals merchandise have an inventory of substances and dietary info.
SBOMs and Vulnerability Detection
Automating software program provide chain safety requires deep visibility into COTS functions. This consists of gaining access to a BOM in addition to detailed vulnerability info to actually perceive the safety dangers to the group.
As well as, an SBOM typically will embody licensing info to assist guarantee compliance and cut back the danger that the software program is launched or consumed with unlicensed elements. This license info may also assist with forensics when investigating which model of an open supply part is susceptible to a safety risk, as is the case with a number of releases of Apache Log4j.
Lowering Threat with SBOM Outputs
There are a number of methods to make use of the info offered by an SBOM as soon as a vulnerability is found. First, consider the outcomes by way of chance and impression. Chances are a willpower of the chance of an assault succeeding utilizing the found vulnerability. Influence ought to contemplate each the quick injury and long-term impression to the corporate model, backside line, and buyer expertise.
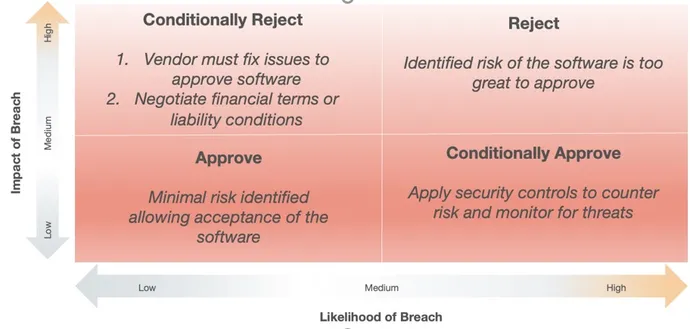
The quadrant method under is one efficient strategy to consider open supply vulnerabilities present in COTS software program. For instance, software program with some vulnerabilities, deemed unlikely to be exploited with low impression, could possibly be accepted for buy, renewal, or upkeep contract by merely accepting the low danger stage. Clearly, software program with a excessive impression, excessive chance of assault vulnerabilities could must be rejected.
Nevertheless, it’s typically not attainable to easily reject software program that’s essential to the enterprise. Whereas utilizing SBOM information within the COTS procurement course of is a comparatively new self-discipline, the belief right here is that each the shopper and the seller will act in good religion to enhance the safety of the product and cut back safety danger over time. This evaluation course of can be utilized to at present deployed software program. The illustration under exhibits a extra nuanced resolution workflow to observe as soon as SBOM outcomes are in-hand.
-Approve/Reject
If the SBOM and vulnerability report point out an unacceptable variety of excessive severity vulnerabilities and the danger is simply too excessive, then the product ought to be rejected (high left above). Equally, if the product reveals solely minor danger, then it may be accepted.
–Conditionally Approve
In instances the place a product introduces safety points (high proper above) however the enterprise wants for the software program outweigh the dangers, the product could be conditionally accepted. In these instances, the safety group can implement compensating safety controls earlier than deployment and monitor for potential risk exercise focusing on recognized vulnerabilities. Moreover, working with the seller to remediate the danger is important as they could be unaware of those vulnerabilities. Disclosure and cooperation are key.
-Conditionally Reject
If the software program product is business-critical however the safety danger is simply too excessive (backside quadrants above), the product could be conditionally rejected. In such instances, the choice to proceed with deployment will depend upon simply how essential the software program is to the enterprise. In instances the place safety danger is simply too excessive, the group can insist the problems be mounted earlier than deployment or anticipate a brand new model of the software program that addresses the vulnerability.
Within the excessive case the place the software program is essential to the enterprise and required for each day operations, the group can negotiate monetary, authorized, and legal responsibility phrases for its use with the seller.
The information offered by SBOMs can be utilized to enhance software program provide chain safety from new product procurement to defending deployed functions. Within the case of COTS software program, making use of SBOM outputs to the danger quadrant mannequin introduced above can assist organizations proactively cut back danger and get rid of threats within the software program that runs their enterprise.
[ad_2]

