[ad_1]

Picture: Sina Drakhshani
Microsoft says Iranian-backed hacking teams have more and more tried to compromise IT providers firms this yr to steal credentials they may use to breach the techniques of downstream purchasers.
In response to safety analysts at Microsoft Menace Intelligence Heart (MSTIC) and Digital Safety Unit (DSU), this exercise is a part of a wider espionage goal to compromise entities of curiosity to the Iranian regime.
“This exercise is notable as a result of focusing on third events has the potential to take advantage of extra delicate organizations by making the most of belief and entry in a provide chain,” Microsoft stated.
“Microsoft has noticed a number of Iranian risk actors focusing on the IT providers sector in assaults that purpose to steal sign-in credentials belonging to downstream buyer networks to allow additional assaults.”
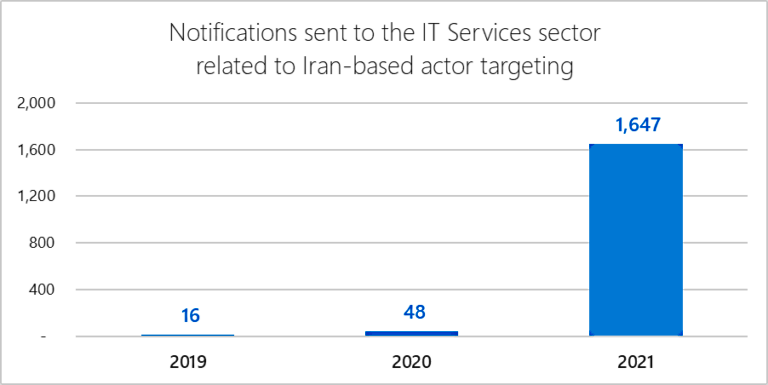
Redmond has despatched over 1,600 notifications to alert greater than 40 IT firms of hacking makes an attempt coordinated by Iranian APT teams.
This reveals a staggering improve in comparison with 2020 when Microsoft solely despatched solely 48 notifications the entire yr.
Most of those assaults are centered on Indian IT providers companies, with a few of them additionally focusing on a number of firms based mostly in Israel and the United Arab Emirates.
As Microsoft revealed, two Iranian hacking teams tracked as DEV-0228 and DEV-0056 efficiently breached IT firms from Israel and Bahrain in July and September:
- In July 2021, a gaggle that MSTIC tracks as DEV-0228 and assesses as based mostly in Iran compromised a single Israel-based IT firm that gives enterprise administration software program. Primarily based on MSTIC’s evaluation, DEV-0228 used entry to that IT firm to increase their assaults and compromise downstream prospects within the protection, power, and authorized sectors in Israel.
- In September, we detected a separate Iranian group, DEV-0056, compromising e-mail accounts at a Bahrain-based IT integration firm that works on IT integration with Bahrain Authorities purchasers, who have been seemingly DEV-0056’s final goal. DEV-0056 additionally compromised varied accounts at {a partially} government-owned group within the Center East that present info and communications know-how to the protection and transportation sectors, that are targets of curiosity to the Iranian regime. DEV-0056 maintained persistence on the IT integration group via at the very least October.
Iranian risk actors have been within the highlight over the last two weeks, with a number of advisories and studies warning of Iranian exercise focusing on organizations worldwide.
US, UK, and Australian cybersecurity businesses warned Thursday of ongoing exploitation of Microsoft Trade ProxyShell and Fortinet vulnerabilities linked to an Iranian-sponsored hacking group and ransomware assaults.
Sooner or later earlier, the Microsoft Menace Intelligence Heart (MSTIC) revealed that six Iranian hacking teams have began deploying ransomware and exfiltrating knowledge from victims’ techniques beginning in September 2020.
The FBI additionally warned in a TLP:AMBER non-public trade notification (PIN) of an Iranian risk actor trying to purchase stolen data related to US and worldwide organizations from clear and darkish net sources that might be used to breach their techniques once more.
[ad_2]
