[ad_1]
Three high-impact safety vulnerabilities have been disclosed in APC Good-UPS units that may very well be abused by distant adversaries as a bodily weapon to entry and management them in an unauthorized method.
Collectively dubbed TLStorm, the issues “enable for full distant takeover of Good-UPS units and the flexibility to hold out excessive cyber-physical assaults,” Ben Seri and Barak Hadad, researchers from IoT safety firm Armis, stated in a report printed Tuesday.
Uninterruptible energy provide (UPS) units perform as emergency backup energy suppliers in mission-critical environments equivalent to medical services, server rooms, and industrial programs. Many of the stricken units, totaling over 20 million, have been recognized up to now in healthcare, retail, industrial, and authorities sectors.
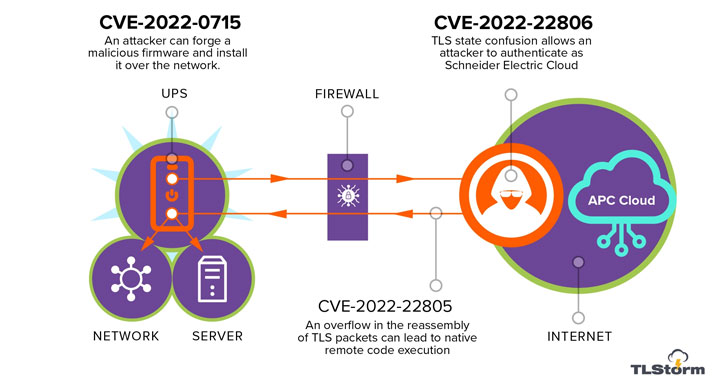
TLStorm consists of a trio of vital flaws that may be triggered by way of unauthenticated community packets with out requiring any person interplay, which means it is a zero-click assault, with two of the problems involving a case of defective TLS handshake between the UPS and the APC cloud –
- CVE-2022-22805 (CVSS rating: 9.0) – TLS buffer overflow
- CVE-2022-22806 (CVSS rating: 9.0) – TLS authentication bypass
- CVE-2022-0715 (CVSS rating: 8.9) – Unsigned firmware improve that may be up to date over the community
Profitable exploitation of any of the issues might end in distant code execution (RCE) assaults on susceptible units, which in flip may very well be weaponized to tamper with the operations of the UPS to bodily injury the machine or different property linked to it.
“Through the use of our RCE vulnerability we have been capable of bypass the software program safety and let the present spike durations run time and again till the DC hyperlink capacitor heated as much as ~150 levels celsius (~300F), which brought about the capacitor to burst and brick the UPS in a cloud of electrolyte gasoline, inflicting collateral injury to the machine,” the researchers defined.
To make issues worse, the flaw within the firmware improve mechanism may very well be leveraged to plant a malicious replace on UPS units, enabling the attackers to ascertain persistence for prolonged durations of time and use the compromised host as a gateway for additional assaults.
“Abusing flaws in firmware improve mechanisms is changing into an ordinary observe of APTs, as has been lately detailed within the evaluation of the Cyclops Blink malware, and improper signing of firmwares of embedded units is a recurring flaw in varied embedded programs,” the researchers stated.
Following accountable disclosure to Schneider Electrical on October 31, 2021, fixes have been launched as a part of Patch Tuesday updates on March 8, 2022. Prospects are really useful to put in the updates offered to cut back the chance of profitable exploitation of those vulnerabilities.
“UPS units, like many different digital infrastructure home equipment, are sometimes put in and forgotten,” the researchers concluded. “Since these units are linked to the identical inside networks because the core enterprise programs, exploitation makes an attempt can have extreme implications.”
[ad_2]