[ad_1]
The financially motivated FIN7 cybercrime gang has masqueraded as one more fictitious cybersecurity firm referred to as “Bastion Safe” to recruit unwitting software program engineers below the guise of penetration testing in a probable lead-up to a ransomware scheme.
“With FIN7’s newest faux firm, the prison group leveraged true, publicly out there info from varied reputable cybersecurity corporations to create a skinny veil of legitimacy round Bastion Safe,” Recorded Future’s Gemini Advisory unit mentioned in a report. “FIN7 is adopting disinformation techniques in order that if a possible rent or get together had been to truth verify Bastion Safe, then a cursory search on Google would return ‘true’ info for corporations with the same identify or trade to FIN7’s Bastion Safe.”
FIN7, also called Carbanak, Carbon Spider, and Anunak, has a monitor document of placing restaurant, playing, and hospitality industries within the U.S. to contaminate point-of-sale (POS) programs with malware designed to reap credit score and debit card numbers which might be then used or bought for revenue on underground marketplaces. The most recent improvement exhibits the group’s enlargement into the extremely worthwhile ransomware panorama.
Establishing faux entrance corporations is nothing new for FIN7, which has been beforehand linked to a different sham cybersecurity agency dubbed Combi Safety that claimed to supply penetration testing providers to prospects. Considered in that gentle, Bastion Safe is not any completely different.
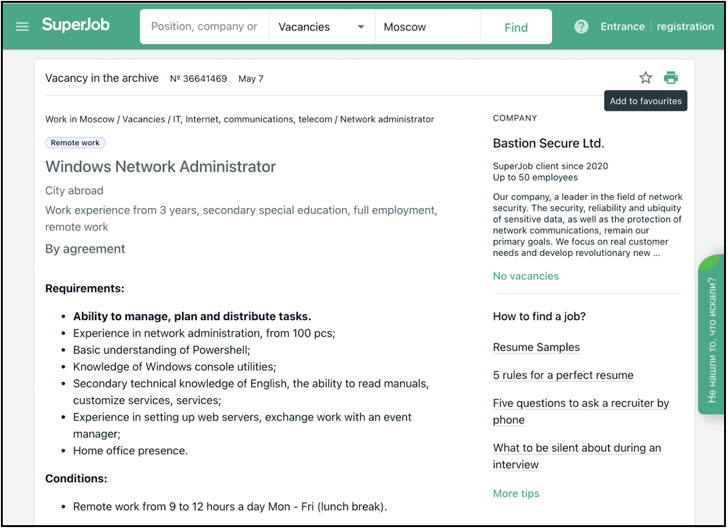
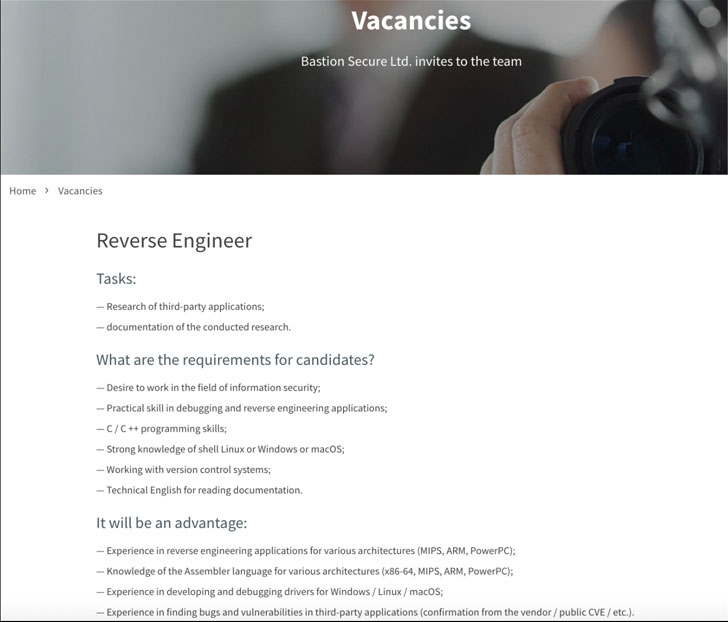
Not solely does the brand new web site characteristic stolen content material compiled from different reputable cybersecurity corporations — primarily Convergent Community Options — the operators marketed seemingly real hiring alternatives for C++, PHP, and Python programmers, system directors, and reverse-engineers on well-liked job boards, providing them a number of instruments for follow assignments in the course of the interview course of.
These instruments had been analyzed and located to be parts of the post-exploitation toolkits Carbanak and Lizar/Tirion, each of which have been beforehand attributed to the group and might be leveraged to compromise POS programs and deploy ransomware.
It is, nevertheless, within the subsequent stage of the hiring course of that Bastion Safe’s involvement in prison exercise grew to become evident, what with the corporate’s representatives offering entry to a so-called shopper firm’s community and asking potential candidates to assemble info on area directors, file programs, and backups, signalling a robust inclination in the direction of conducting ransomware assaults.
“Bastion Safe’s job provides for IT specialist positions ranged between $800 and $1,200 USD a month, which is a viable beginning wage for this sort of place in post-Soviet states,” the researchers mentioned. “Nonetheless, this ‘wage’ could be a small fraction of a cybercriminal’s portion of the prison earnings from a profitable ransomware extortion or large-scale fee card-stealing operation.”
By paying “unwitting ‘staff’ far lower than it must pay knowledgeable prison accomplices for its ransomware schemes, […] FIN7’s faux firm scheme allows the operators of FIN7 to acquire the expertise that the group wants to hold out its prison actions, whereas concurrently retaining a bigger share of the earnings,” the researchers added.
Moreover posing as a company entity, a further step taken by the actor to provide it a hoop of authenticity is the truth that one of many firm’s workplace addresses is identical as that of a now-defunct, U.Okay.-based firm named Bastion Safety (North) Restricted. Internet browsers akin to Apple Safari and Google Chrome have since blocked entry to the misleading website.
“Though cybercriminals in search of unwitting accomplices on reputable job websites is nothing new, the sheer scale and blatancy with which FIN7 operates proceed to surpass the habits proven by different cybercriminal teams,” the researchers mentioned, including the group is “making an attempt to obfuscate its true identification as a prolific cybercriminal and ransomware group by making a fabricated net presence by means of a largely legitimate-appearing web site, skilled job postings, and firm information pages on Russian-language enterprise improvement websites.”
[ad_2]