[ad_1]
Three totally different state-sponsored menace actors aligned with China, India, and Russia have been noticed adopting a brand new technique known as RTF (aka Wealthy Textual content Format) template injection as a part of their phishing campaigns to ship malware to focused techniques.
“RTF template injection is a novel method that’s very best for malicious phishing attachments as a result of it’s easy and permits menace actors to retrieve malicious content material from a distant URL utilizing an RTF file,” Proofpoint researchers mentioned in a brand new report shared with The Hacker Information.
On the coronary heart of the assault is an RTF file containing decoy content material that may be manipulated to allow the retrieval of content material, together with malicious payloads, hosted at an exterior URL upon opening an RTF file. Particularly, it leverages the RTF template performance to change a doc’s formatting properties utilizing a hex editor by specifying a URL useful resource as a substitute of an accessible file useful resource vacation spot from which a distant payload could also be retrieved.
Put in a different way, the concept is that attackers can ship malicious Microsoft Phrase paperwork to focused victims that seem solely innocuous however are designed to load malicious code through the template function remotely.
Thus when an altered RTF file is opened through Microsoft Phrase, the applying will proceed to obtain the useful resource from the required URL previous to displaying the lure content material of the file. It is subsequently not stunning that the method is being more and more weaponized by menace actors to distribute malware.
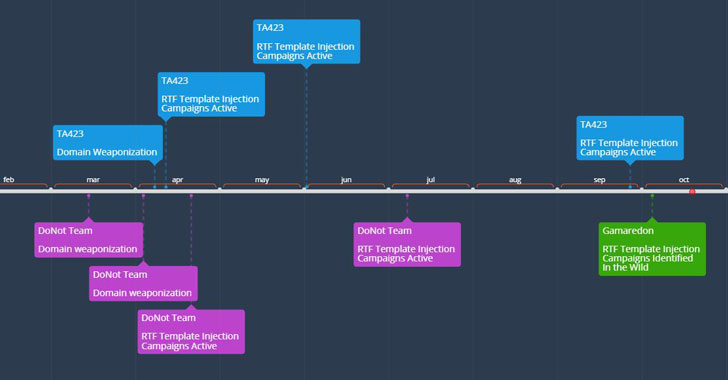
Proofpoint mentioned it noticed Template injection RTF information linked to the APT teams DoNot Crew, Gamaredon, and a Chinese language-related APT actor dubbed TA423 as early as February 2021, with the adversaries using the information to focus on entities in Pakistan, Sri Lanka, Ukraine, and people working within the deep water power exploration sector in Malaysia through defense-themed and different country-specific lures.
Whereas the DoNot Crew has been suspected of finishing up cyber assaults which are aligned with Indian-state pursuits, Gamaredon was lately outed by Ukrainian legislation enforcement as members of Russia’s Federal Safety Service (FSB) with a propensity for placing the private and non-private sector within the nation for harvesting categorised data from compromised Home windows techniques for geopolitical beneficial properties.
“The innovation by menace actors to carry this technique to a brand new file sort in RTFs represents an increasing floor space of menace for organizations worldwide,” the researchers mentioned. “Whereas this technique at present is utilized by a restricted variety of APT actors with a variety of sophistication, the method’s effectiveness mixed with its ease of use is prone to drive its adoption additional throughout the menace panorama.”
[ad_2]