[ad_1]

One among Iran’s largest privately-owned airways, Mahan Air, has introduced a cybersecurity incident that has resulted in its web site going offline and probably information loss.
Because the agency introduced on Twitter, coping with hacker assaults is nothing out of the unusual for them, so though some injury has been completed, the flight schedules will not be affected.
As such, though individuals cannot entry Mahan’s web site, all worldwide and home flights are operating as typical with out modifications or delays.
Furthermore, the corporate claims that the assault has been thwarted efficiently and in a short while, downplaying its significance and disregarding any actual influence.
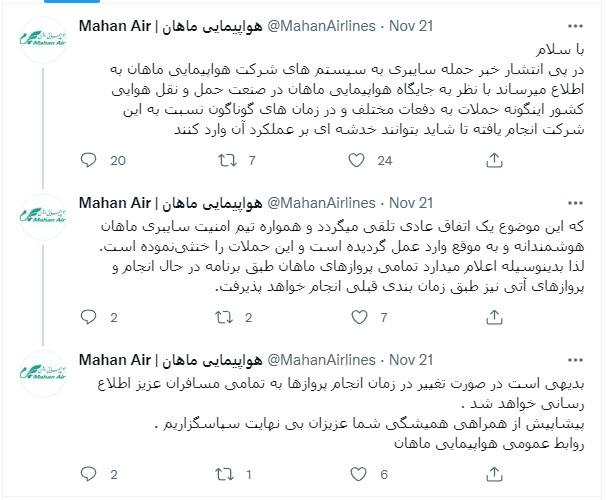
“Following the information of the cyber assault on the methods of Mahan Airways, it’s reported that because of the place of Mahan Airways within the nation’s aviation trade, such assaults have been carried out in opposition to this firm many instances and at completely different instances, in order that they could be broken,” reads the translated tweet by Mahan airways.
“That is thought of a traditional prevalence and Mahan Cyber Safety Staff has at all times acted intelligently and in a well timed method and has thwarted these assaults. Due to this fact, it hereby pronounces that every one Mahan flights might be operated in line with the schedule and future flights might be operated in line with the earlier schedule.”
Supply: Twitter
Focusing on a sanctioned entity
Mahan Air was added to the US sanctions checklist in 2011 for supporting members of Iran’s Islamic Revolutionary Guard Corps (IRGC).
In 2019, the US Treasury revealed a press release on Mahan Air’s operation, detailing the next:
“Mahan Air has transported IRGC-QF operatives, weapons, tools, and funds overseas in help of the IRGC-QF’s regional operations, and has additionally moved weapons and personnel for Hizballah.”
“For the reason that onset of the Syrian civil battle, Mahan Air has routinely flown fighters and materiel to Syria to prop up the Assad regime, which has contributed to mass atrocities and displacement of civilians.”
Though Mahan’s operations oppose American strategic pursuits, which led to precise navy motion in July 2020, the hackers accountable for the latest incident are not Individuals. q
The actor who took accountability for the cyberattack on Mahan Air is ‘Hooshyarane Vatan,’ who sees IRGC as their enemy and says they battle for the rights of the Ahwaz minority (Iranian Arab minority).
The hackers declare to have stolen confidential paperwork exposing how Mahair Air has labored with the IRGC and threatened to publish names, numbers, and proof of Mahan’s actions.
“Hacking Mahan Airways is step one of a program to cease the looting and encroachments of the corrupt corps on the town and the individuals of Ahvaz and Khuzestan. With the confidential paperwork we have now obtained from the inner community of Mahan Airways, we’ll show our declare of Mahan complicity within the legal actions of the IRGC, and we may also present that the Quds drive is looting the cash and assets of the individuals and the nation of Iran amongst rebel teams,” reads a translated textual content from the alleged hackers.
“And the international militia squanders cash and on the similar time makes use of the identical oppressed individuals as cowl for the air transport of weapons, tools and ammunition.”
Because the actors wrote on their Telegram channel, they’ve proof of the airline hiding navy shipments in civilian flights to safe them from assaults.
Iran tensions with the Western world
Final week, a crescendo of studies about Iranian hackers concentrating on American, Israeli, and European entities happened. On the similar time, Microsoft revealed a report figuring out six distinct Iranian hacking teams that look like state-sponsored.
This reporting culminated with the indictment of two Iranian cyber-actors who tried to affect American voters between September and November 2020, selling false data below the ‘Proud Boys’ apparel.
Each of the recognized actors allegedly labored for a cybersecurity firm that offered providers to the Iranian authorities.
[ad_2]


