[ad_1]
Korean researchers have developed a set of assaults in opposition to some solid-state drives (SSDs) that might enable planting malware in a location that is past the attain of the person and safety options.
The assault fashions are for drives with flex capability options and goal a hidden space on the machine referred to as over-provisioning, which is extensively utilized by SSD makers lately for efficiency optimization on NAND flash-based storage methods.
{Hardware}-level assaults supply final persistence and stealth. Refined actors have labored laborious to implement such ideas in opposition to HDDs up to now, hiding malicious code in unreachable disk sectors.
How flex capability works
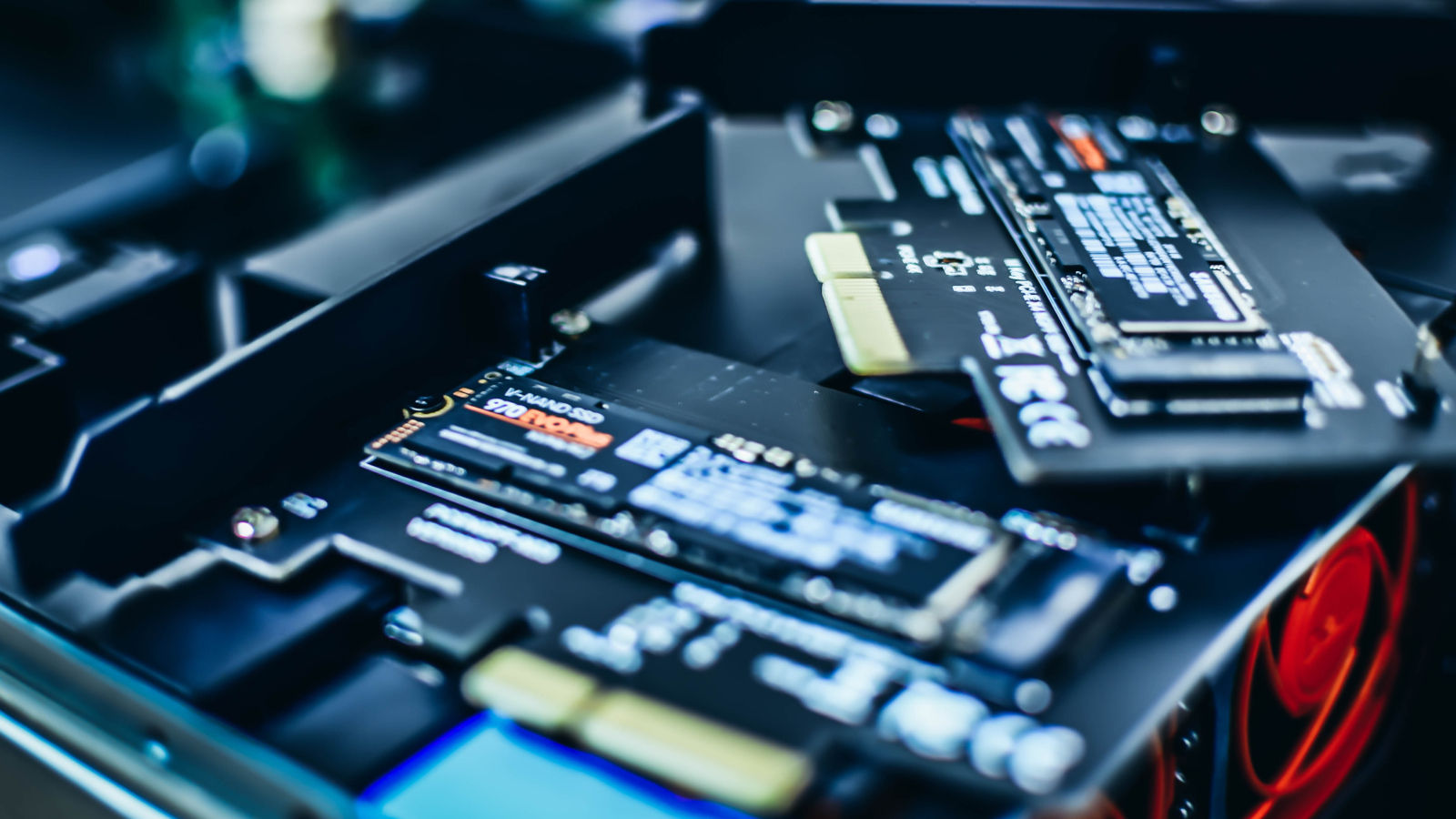
Flex capability is a characteristic in SSDs from Micron Know-how that allows storage gadgets to routinely modify the sizes of uncooked and user-allocated area to attain higher efficiency by absorbing write workload volumes.
It’s a dynamic system that creates and adjusts a buffer of area referred to as over-provisioning, usually taking between 7% and 25% of the overall disk capability.
The over-provisioning space is invisible to the working system and any purposes working on it, together with safety options and anti-virus instruments.
Because the person launches totally different purposes, the SSD supervisor adjusts this area routinely in opposition to the workloads, relying on how write or read-intensive they’re.
The assault fashions
One assault modeled by researchers at Korea College in Seoul targets an invalid information space with non-erased info that sits between the usable SSD area and the over-provisioning (OP) space, and whose measurement will depend on the 2.
The analysis paper explains {that a} hacker can change the dimensions of the OP space through the use of the firmware supervisor, thus producing exploitable invalid information area.
The issue right here is that many SSD producers select to not erase the invalid information space to avoid wasting on assets. This area stays crammed with information for in depth durations, underneath the belief that breaking the hyperlink of the mapping desk is sufficient to stop unauthorized entry.
As such, a menace actor leveraging this weak point might achieve entry to probably delicate info.
Supply: Arxiv.org
The researchers notice that forensic exercise on NAND flash reminiscence can reveal information that has not been deleted in over six months.
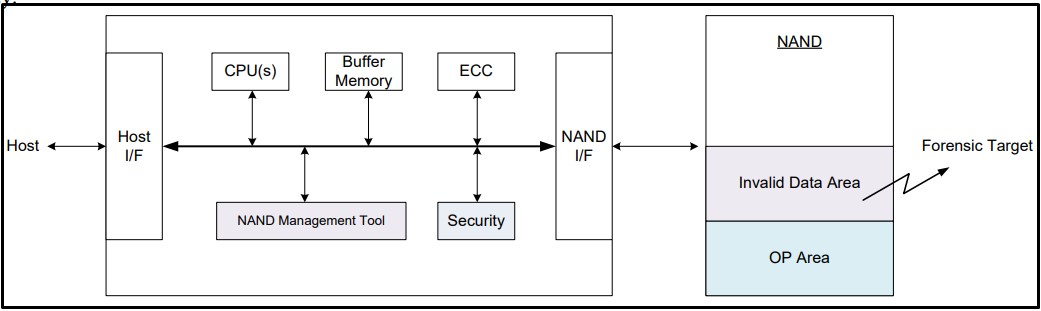
In a second assault mannequin, the OP space is used as a secret place that customers can’t monitor or wipe, the place a menace actor might disguise malware.
Supply: Arxiv.org
The paper describes this assault as follows:
It’s assumed that two storage gadgets SSD1 and SSD2 are related to a channel so as to simplify the outline. Every storage machine has 50% OP space. After the hacker shops the malware code in SSD2, they instantly scale back the OP space of SSD1 to 25% and increase the OP space of SSD2 to 75%.
At the moment, the malware code is included within the hidden space of SSD2. A hacker who positive aspects entry to the SSD can activate the embedded malware code at any time by resizing the OP space. Since regular customers keep 100% person space on the channel, it is not going to be straightforward to detect such malicious habits of hackers.
The plain benefit of such an assault is that it’s stealthy. Detecting malicious code in OP areas just isn’t solely time-consuming but in addition requires highly-specialized forensic strategies.
Countermeasures
As a protection in opposition to the primary kind of assault, the researchers suggest SSD makers wipe the OP space with a pseudo-erase algorithm that might not have an effect on real-time efficiency.
For the second kind of assault, a probably efficient safety measure in opposition to injecting malware within the OP space is to implement valid-invalid information fee monitoring methods that watch the ratio inside SSDs in real-time.
When the invalid information ratio will increase considerably hastily, the person might get a warning and the choice of a verifiable data-wiping perform within the OP area.
Lastly, entry to the SSD administration app ought to have strong defenses in opposition to unauthorized entry.
“Even if you’re not a malicious hacker, a misguided worker can simply free hidden info and leak it through the use of the OP space variable firmware/software program at any time” – the researchers clarify.
Bleeping Laptop has reached out to Micron asking for a touch upon the above, and we’ll replace this story once we obtain a response.
Whereas the analysis demonstrates that the OP space on Micron SSDs can be utilized to retailer malware, it’s unlikely that such assaults are happening within the wild proper now.
[ad_2]