[ad_1]
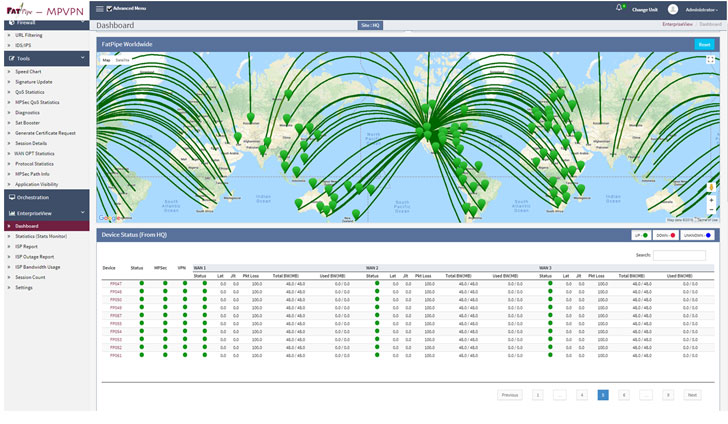
The U.S. Federal Bureau of Investigation (FBI) has disclosed that an unidentified risk actor has been exploiting a beforehand unknown weak spot within the FatPipe MPVPN networking gadgets not less than since Might 2021 to acquire an preliminary foothold and preserve persistent entry into weak networks, making it the most recent firm to affix the likes of Cisco, Fortinet, Citrix, Pulse Safe which have had their methods exploited within the wild.
“The vulnerability allowed APT actors to realize entry to an unrestricted file add operate to drop an internet shell for exploitation exercise with root entry, resulting in elevated privileges and potential follow-on exercise,” the company stated in an alert revealed this week. “Exploitation of this vulnerability then served as a leaping off level into different infrastructure for the APT actors.”
In different phrases, the zero-day vulnerability permits a distant attacker to add a file to any location on the filesystem on an affected machine. The safety flaw impacts the online administration interface of FatPipe WARP, MPVPN, and IPVPN router clustering and VPN load-balancing gadgets working software program previous to the most recent model releases 10.1.2r60p93 and 10.2.2r44p1.
The FBI, in its flash alert, famous that the risk actor leveraged the online shell to maneuver laterally and strike extra U.S. infrastructure by establishing a malicious SSH service, following it up with quite a lot of steps designed to cover the intrusions and defend their exploit till it is wanted once more.
In an unbiased bulletin (FPSA006), FatPipe stated that the bug stems from an absence of enter validation mechanism for particular HTTP requests, thus enabling an attacker to use the difficulty by sending a specifically crafted HTTP request to the affected machine. Whereas there are not any workarounds that deal with the flaw, the corporate stated it may be mitigated by disabling UI and SSH entry on the WAN interface or configuring Entry Lists to allow entry solely from trusted sources.
[ad_2]