[ad_1]
Banking apps from Brazil are being focused by a extra elusive and stealthier model of an Android distant entry trojan (RAT) that is able to finishing up monetary fraud assaults by stealing two-factor authentication (2FA) codes and initiating rogue transactions from contaminated gadgets to switch cash from victims’ accounts to an account operated by the menace actor.
IBM X-Power dubbed the revamped banking malware BrazKing, a earlier model of which was known as PixStealer by Test Level Analysis. The cellular RAT was first seen round November 2018, in accordance to ThreatFabric.
“It seems that its builders have been engaged on making the malware extra agile than earlier than, transferring its core overlay mechanism to tug faux overlay screens from the command-and-control (C2) server in real-time,” IBM X-Power researcher Shahar Tavor famous in a technical deep dive printed final week. “The malware […] permits the attacker to log keystrokes, extract the password, take over, provoke a transaction, and seize different transaction authorization particulars to finish it.”
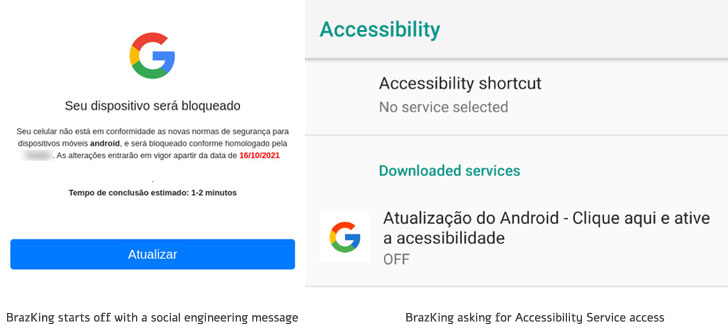
The an infection routine kicks off with a social engineering message that features a hyperlink to an HTTPS web site that warns potential victims about safety points of their gadgets, whereas prompting an choice to replace the working system to the most recent model. Nonetheless, for the assaults to succeed, customers must explicitly allow a setting to set up apps from unknown sources.
BrazKing, like its predecessor, abuses accessibility permissions to carry out overlay assaults on banking apps, however as a substitute of retrieving a faux display screen from a hardcoded URL and current it on prime of the official app, the method is now performed on the server-side in order that the record of focused apps might be modified with out making adjustments to the malware itself.
“The detection of which app is being opened is now accomplished server aspect, and the malware recurrently sends on-screen content material to the C2. Credential grabbing is then activated from the C2 server, and never by an automated command from the malware,” Tavor stated.
Banking trojans like BrazKing are significantly insidious in that after set up they require solely a single motion from the sufferer, i.e., enabling Android’s Accessibility Service, to completely unleash their malicious functionalities. Armed with the required permissions, the malware gathers intel from the contaminated machine, together with studying SMS messages, capturing keystrokes, and accessing contact lists.
“Accessibility Service is lengthy identified to be the Achilles’ heel of the Android working system,” ESET researcher Lukas Stefanko stated final 12 months.
On prime of that, the malware additionally takes a number of steps to attempt to defend itself as soon as it has been put in to keep away from detection and elimination. BrazKing is designed to observe customers when they’re launching an antivirus resolution or opening the app’s uninstall display screen, and if that’s the case, swiftly return them to the house display screen earlier than any motion might be taken.
“Ought to the consumer try to revive the machine to manufactory settings, BrazKing would rapidly faucet the ‘Again’ and ‘Dwelling’ buttons sooner than a human might, stopping them from eradicating the malware in that method,” Tavor defined.
The final word purpose of the malware is to permit the adversary to work together with working apps on the machine, maintain tabs on the apps the customers are viewing at any given level of time, file keystrokes entered in banking apps, and show fraudulent overlay screens to siphon the fee card’s PIN numbers and 2FA codes, and finally carry out unauthorized transactions.
“Main desktop banking trojans have lengthy deserted the patron banking realms for larger bounties in BEC fraud, ransomware assaults and high-value particular person heists,” Tavor stated. “This, along with the continued pattern of on-line banking transitioning to cellular, triggered a void within the underground cybercrime enviornment to be crammed by cellular banking malware.”
[ad_2]