[ad_1]
With all of the hype round low-code/no-code platforms, many are actually touting the advantages of adopting low-code/no-code growth. Let’s tackle the (safety) elephant within the room: Anybody can spin up purposes utilizing these instruments, however who’s liable for the safety of those purposes?
If, just like cloud computing, it’s a shared-responsibility mannequin, then the place can we draw the traces of duty among the many totally different events concerned?
One Measurement Does Not Match All
Low-code purposes are various: They arrive in several types, range in how they’re deployed, and resolve a broad vary of issues. When discussing the safety duty mannequin for low-code purposes, we’ve to first perceive the totally different layers of a low-code utility. Here’s a temporary abstract:
- Layer 1: The infrastructure on which the low-code utility is working on, which incorporates the servers working the working system, the community through which the servers are deployed, the underlying working system(s), and virtualization layers, containers, and container orchestration getting used.
- Layer 2: The runtime setting used for working the low-code utility.
- Layer 3: The appliance itself, which incorporates the enterprise logic of the appliance; any widgets, elements, and connectors supplied by the low-code platform; customized widgets/elements created by the app proprietor’s group; third-party widgets, elements, and connectors, reminiscent of these obtainable via the totally different public marketplaces; any ancillary companies being utilized by the low-code utility, reminiscent of public cloud companies (e.g., storage buckets, message queues, IoT units) and SaaS situations (e.g., Salesforce, ServiceNow, Slack); and id and entry administration instruments getting used.
- Layer 4: The info being utilized by the appliance. Information will be saved in several areas — generally within the cloud and generally on-premise.
We will additionally contemplate the low-code platform growth setting used to develop the appliance as Layer 0. Even when you do every thing crucial to carefully safe your utility, if a malicious person will get entry to your growth console — that’s simply as dangerous.
Safety Is a Shared Duty
Cloud computing’s strategy to the shared-responsibility mannequin is simple: As you advance in your cloud journey and undertake increased ranges of abstraction, the safety duty shifts away from you and towards the cloud supplier.
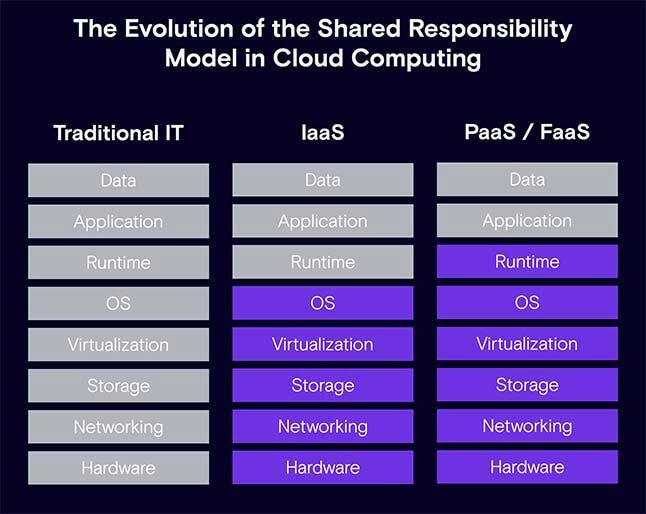
Ought to we contemplate low-code/no-code purposes as yet one more step on this evolution?
It relies upon. The place the duty lies is dependent upon the alternatives you make when adopting low-code growth. For instance, with the infrastructure layer, are you planning on internet hosting your utility in a personal cloud or a public knowledge middle? Some low-code/no-code platforms are designed particularly for on-premises or hybrid cloud/on-premises deployments. In the event you resolve to host your individual purposes, you should have full management over the underlying infrastructure, however that additionally means you’re liable for securing each side of the setting.
Software-Layer Decisions
What are some growth decisions in regards to the utility layer that have an effect on the safety duty?
If the low-code utility is strictly made up of low-code platform native capabilities or companies, you solely have to fret in regards to the fundamentals. That features utility design and enterprise logic flaws, securing your knowledge in transit and at relaxation, safety misconfigurations, authentication, authorizing and adhering to the precept of least-privilege, offering safety coaching on your citizen builders, and sustaining a safe deployment setting. These are the identical parts any developer — low-code or conventional — would want to consider with the intention to safe the appliance. All the pieces else is dealt with by the low-code platform itself.
That’s as primary because it will get.
However what if you’re making use of further widgets, elements, or connectors supplied by the low-code platform? These elements — and the code used to construct them — are undoubtedly out of your jurisdiction of duty. It’s possible you’ll want to contemplate how they’re configured or utilized in your utility, although. It’s potential that an incorrectly used part might result in a possible vulnerability in your utility.
For instance, most low-code platforms present a SQL database connector, which permits low-code app builders to run SQL queries to entry the information saved within the databases. In some frequent SQL connectors that we checked out, we noticed a number of strategies for interacting with databases: Some supplied strict safety and allowed much less flexibility to builders, whereas others had been extra versatile. If used incorrectly, these connectors with versatile strategies might result in a disastrous SQL injection (SQLi) vulnerability. For instance, a profitable SQLi assault in opposition to a low-code utility can lead to unauthorized entry to the information. The attacker could possibly manipulate the information and even execute shell instructions on the database server.
The third alternative is to increase the elements library with customized elements as a result of the low-code/no-code platform of alternative doesn’t present all of the wanted (or desired) performance. For instance, you could create Mendix customized widgets to create dynamic menus in your utility, Appian customized plug-in elements to render a Google Maps object, or Canvas Apps in Microsoft Energy Apps to combine knowledge from different Microsoft purposes.
Whereas customized constructed elements present extensibility and the liberty to create performance as you see match, additionally they introduce extra code and logic to your utility. Similar to with historically developed software program, extra code and logic means a better probability of introducing defects, design flaws, and safety vulnerabilities. When growing customized elements, even within the low-code/no-code world, be sure to have the right SDLC and safety processes in place. Builders ought to observe your group’s safety coverage and tips for growing and deploying purposes.
Lastly, you might have to depend on third-party elements as a result of the performance you’re on the lookout for doesn’t exist as a local service or is obtainable as an add-on part by your low-code platform. On this case, you’ll be liable for vetting and selecting third-party elements primarily based on a number of components:
- Is the supply code obtainable for evaluation?
- How typically is the part up to date?
- Does the part come from a good writer or group?
- Is the part linked to a third-party service, and, if that’s the case, is it safe?
- Does the low-code platform supplier carry out any form of safety validation on elements within the market?
Much like vetting third-party open supply packages, you will need to have a course of in place to be sure to are usually not turning these elements into the weakest hyperlink of your utility safety chain.
Selecting Between the Cloud and On-Premises
It’s fairly frequent to combine low-code purposes with present public cloud accounts with the intention to eat public cloud companies, reminiscent of storage buckets, message queues, databases, and so forth. If that’s the case, it’s important to add cloud safety as an extra issue to the general safety posture of your utility. It is best to be sure to are adopting a mature cloud safety posture administration strategy.
Many low-code/no-code platforms supply connectivity to on-premises knowledge and purposes. For instance, organizations that use the Microsoft Energy Apps low-code platform have the choice to make use of an on-premises knowledge gateway, which acts as a bridge to offer fast and safe knowledge switch between on-premises knowledge (knowledge not within the cloud) and several other Microsoft cloud companies. One other instance is when utilizing the Appian low-code platform with robotic course of automation (RPA), which helps a hybrid cloud/on-premises deployment mannequin.
When making a bridge between the cloud and your group’s on-premises infrastructure, knowledge, and purposes, you’re basically opening up your personal belongings to entry from the general public Web. Evidently, in such instances safety and privateness needs to be top-of-mind, and entry needs to be as restricted as potential — encrypted and monitored always.
Who Is Accountable? The Verdict
Given all of the totally different choices for low-code utility growth, there’s actually no easy reply. Neither is there a straight line we will attract some low-code stack safety chart that may be clear-cut. Low-code/no-code is a paradigm shift in the way in which software program is developed, from monolithic, to microservices, and now — low-code/no-code. It shouldn’t be seen as a option to summary away {hardware} and deployment fashions as a part of the following part within the evolution of cloud computing.
The underside line is that low-code/no-code purposes are one other type of software program. It’s inevitable they may comprise bugs, design flaws, vulnerabilities, and misconfigurations that may introduce danger. Even if you’re giving freely a few of the management and duty to a low-code/no-code platform supplier or different provider, you’re nonetheless the proprietor of your utility and its knowledge. You stay liable for ensuring the purposes are safe and cling to your company safety insurance policies and requirements.
No matter how a lot abstraction you employ, and the way a lot management you’re giving up, at all times bear in mind the next two points: know your apps, and safe your small business logic. You have to totally perceive how your low-code purposes are developed, deployed and maintained. At all times be sure to have full visibility to your low-code purposes, and tackle any safety issues raised right here. And no matter how your utility is developed, you need to at all times just remember to utilized safe design, growth and utility safety finest practices. A easy flaw in enterprise logic can take advantage of resilient utility weak.
[ad_2]

