[ad_1]
Researchers have unearthed a brand new distant entry trojan (RAT) for Linux that employs a never-before-seen stealth method that entails masking its malicious actions by scheduling them for execution on February thirty first, a non-existent calendar day.
Dubbed CronRAT, the sneaky malware “allows server-side Magecart knowledge theft which bypasses browser-based safety options,” Sansec Menace Analysis stated. The Dutch cybersecurity agency stated it discovered samples of the RAT on a number of on-line shops, together with an unnamed nation’s largest outlet.
CronRAT’s standout function is its skill to leverage the cron job-scheduler utility for Unix to cover malicious payloads utilizing job names programmed to execute on February thirty first. Not solely does this enable the malware to evade detection from safety software program, but it surely additionally allows it to launch an array of assault instructions that might put Linux eCommerce servers in danger.
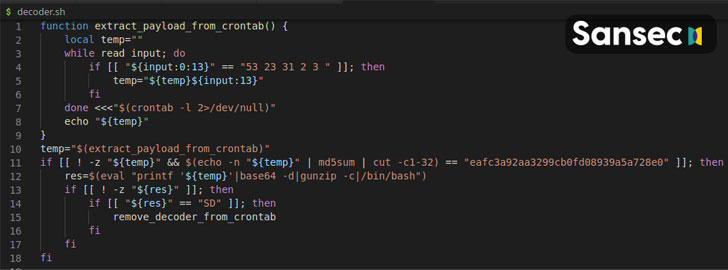
“The CronRAT provides various duties to crontab with a curious date specification: 52 23 31 2 3,” the researchers defined. “These traces are syntactically legitimate, however would generate a run time error when executed. Nevertheless, this may by no means occur as they’re scheduled to run on February thirty first.”
The RAT — a “subtle Bash program” — additionally makes use of many ranges of obfuscation to make evaluation troublesome, reminiscent of inserting code behind encoding and compression limitations, and implementing a customized binary protocol with random checksums to slide previous firewalls and packet inspectors, earlier than establishing communications with a distant management server to await additional directions.
Armed with this backdoor entry, the attackers related to CronRAT can run any code on the compromised system, the researchers famous.
“Digital skimming is shifting from the browser to the server and that is one more instance,” Sansec’s Director of Menace Analysis, Willem de Groot, stated. “Most on-line shops have solely applied browser-based defenses, and criminals capitalize on the unprotected back-end. Safety professionals ought to actually think about the complete assault floor.”
[ad_2]