[ad_1]
Researchers have found 14 new forms of cross-site knowledge leakage assaults towards a lot of trendy internet browsers, together with Tor Browser, Mozilla Firefox, Google Chrome, Microsoft Edge, Apple Safari, and Opera, amongst others.
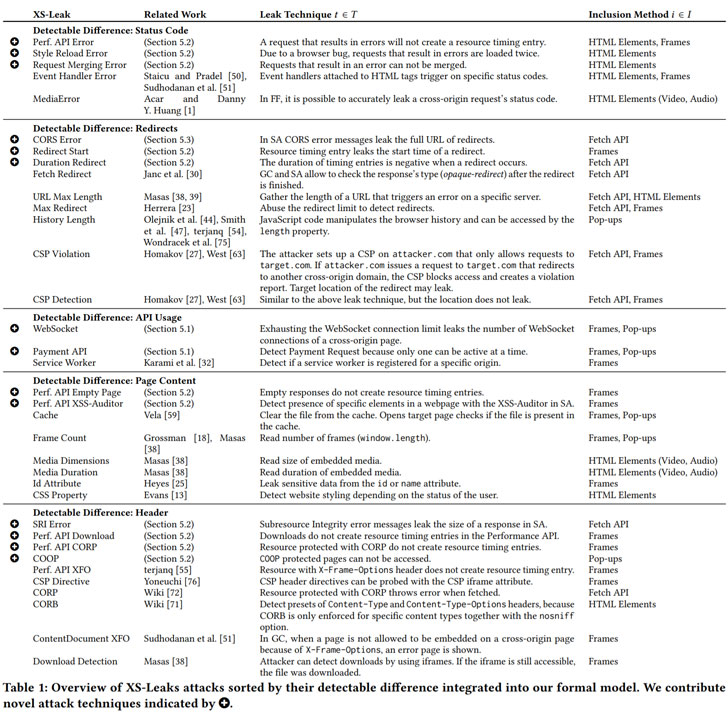
Collectively often known as “XS-Leaks,” the browser bugs allow a malicious web site to reap private knowledge from its guests as they work together with different web sites within the background with out the targets’ information. The findings are the results of a complete research of cross-site assaults undertaken by a bunch of teachers from Ruhr-Universität Bochum (RUB) and Niederrhein College.
“XS-Leaks bypass the so-called same-origin coverage, one in every of a browser’s foremost defences towards numerous forms of assaults,” the researchers mentioned in a press release. “The aim of the same-origin coverage is to stop data from being stolen from a trusted web site. Within the case of XS-Leaks, attackers can nonetheless acknowledge particular person, small particulars of an internet site. If these particulars are tied to private knowledge, these knowledge might be leaked.”
Stemming from side-channels constructed into the net platform that allows an attacker to assemble this knowledge from a cross-origin HTTP useful resource, the cross-site bugs affect an array of fashionable browsers comparable to Tor, Chrome, Edge, Opera, Safari Firefox, Samsung Web, spanning throughout completely different working programs Home windows, macOS, Android, and iOS.
The brand new class of vulnerabilities can also be completely different from a cross-site request forgery (CSRF) assault in that in contrast to the latter, which exploits an online utility’s belief in a browser shopper to execute unintended actions on behalf of the consumer, they are often weaponized to deduce details about a consumer.
“They’re a major menace to Web privateness since merely visiting an online web page could reveal if the sufferer is a drug addict or leak a sexual orientation,” the researchers defined. “XS-Leaks make the most of small items of knowledge that are uncovered throughout interactions between web sites […] to disclose delicate details about customers, comparable to their knowledge in different internet purposes, particulars about their native atmosphere, or inner networks they’re related to.”
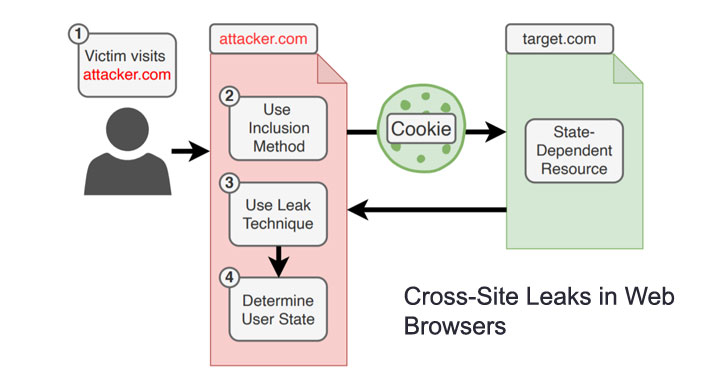
The core thought is that whereas web sites usually are not allowed to immediately entry knowledge (i.e., learn server responses) on different web sites due to same-origin constraints, a rogue on-line portal can try to load a selected useful resource or an API endpoint from an internet site, say, a web-based banking web site, on the consumer’s browser and draw inferences in regards to the sufferer’s transaction historical past. Alternatively, the supply of the leak may very well be timing-based side-channels or speculative execution assaults like Meltdown and Spectre.
As mitigations, the researchers advocate denying all occasion handler messages, minimizing error message occurrences, making use of world restrict restrictions, and creating a brand new historical past property when redirection happens. On the end-user facet, turning on first-party isolation in addition to Enhanced Monitoring Prevention in Firefox have been discovered to lower the applicability of XS-Leaks. Clever Monitoring Prevention in Safari, which blocks third-party cookies by default, additionally prevents all leaks that aren’t based mostly on a pop-up.
“The basis explanation for most XS-Leaks is inherent to the design of the net,” the researchers mentioned. “Oftentimes purposes are susceptible to some cross-site data leaks with out having executed something flawed. It’s difficult to repair the foundation explanation for XS-Leaks on the browser degree as a result of in lots of instances doing so would break present web sites.”
[ad_2]