[ad_1]
For the reason that public launch by the Nationwide Safety Company of the software program reverse engineering (SRE) software suite Ghidra, our crew of researchers on the SEI’s CERT Division have been working to create a brand new suite of instruments to make it simpler for analysts to benefit from Ghirdra’s capabilities and interface. This new suite of instruments, generally known as Kaiju, helps malware evaluation and reverse engineering benefit from Ghidra’s capabilities and interface, that are comparatively straightforward to make use of throughout malware evaluation. The instruments included with Kaiju give malware analysts many benefits as they’re confronted with more and more various and complicated malware threats.
One of many extra advanced plugins included in Kaiju is a Satisfiability Modulo Theories (SMT)-based path evaluation software named GhiHorn. On this publish we current and focus on using two Ghihorn instruments: API Analyzer and Path Analyzer. Each of those instruments allow analysts to search out paths in executables primarily based on quite a few standards, corresponding to user-specified begin and finish addresses or passing by means of particular program factors. Our earlier work has proven that executable path discovering can help numerous malware evaluation actions. One instance that we have now beforehand cited is a malware program that accommodates a verify for the presence of a debugger, a standard method meant to hinder evaluation. The analyst might want to know if there’s a viable execution path that circumvents this verify and, if there’s a path, what inputs and environmental situations are wanted to traverse it. Each PathAnalyzer and ApiAnalyzer can be utilized to deal with and resolve a lot of these issues.
GhiHorn Instruments: ApiAnalyzer and PathAnalyzer
On high of the GhiHorn platform we have now carried out two path evaluation instruments: PathAnalyzer and ApiAnalyzer. Each instruments use Horn encoding and fixing as their main technique for path evaluation, and each emphasize the usefulness of outcomes.
PathAnalyzer
PathAnalyzer permits an analyst to find out if a path exists between two areas in a program and, if that’s the case, what values are required to take that path. PathAnalyzer integrates with Ghidra as a plugin (Determine 1). An analyst should present begin and aim addresses to seed the evaluation. If a path is possible, PathAnalyzer returns a solution within the type of a graph containing details about the recovered path.
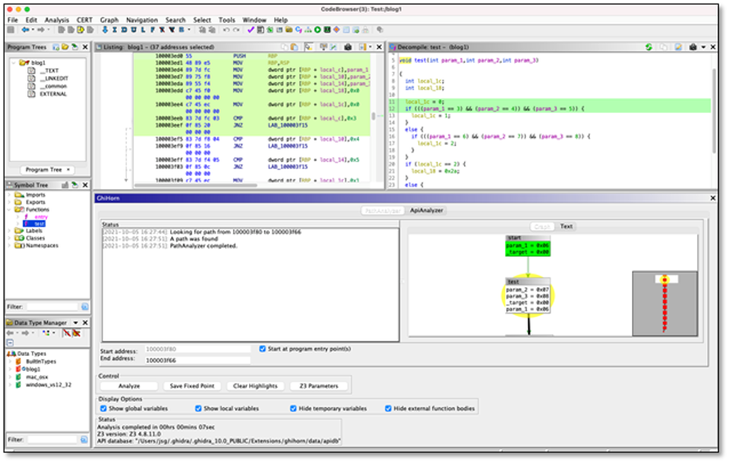
Determine 1: PathAnalyzer person interface
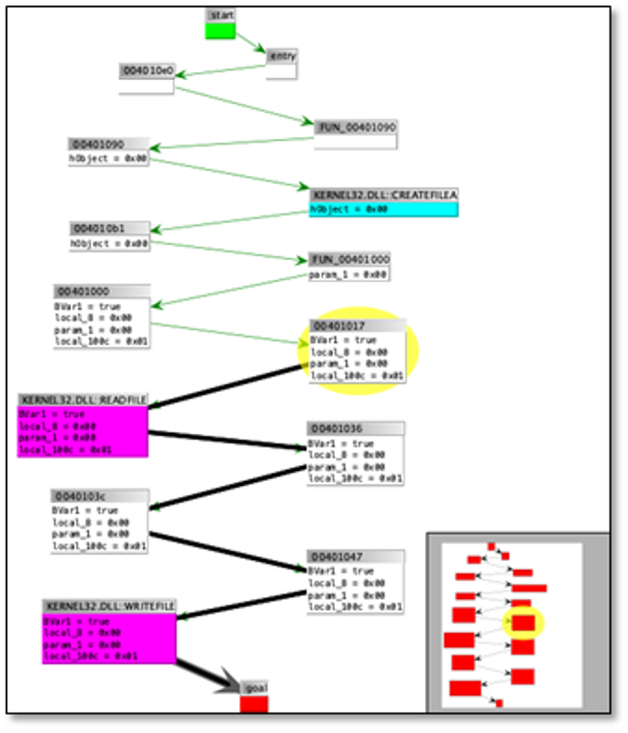
An instance of a recovered path is proven in Determine 2. Every vertex within the graph represents a fundamental block traversed. GhiHorn operates on stay variables current in every fundamental block, with an emphasis on variables which can be linked to decompilation information buildings. The variable values within the vertices are the values that Z3 chosen to achieve the aim deal with. The graph is clickable within the Ghidra person interface, which means that deciding on a node will spotlight the related decompilation and disassembly directions for the reply vertex.
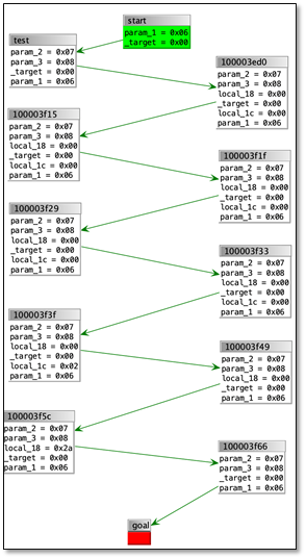
Determine 2: PathAnalyzer reply graph
If no path is discovered, then a counterexample graph is generated displaying how the question failed. On this model of GhiHorn the counterexample will not be very significant. At present, the precise outcomes for unsatisfiable queries are offered as they’re returned by Z3: as a graph with Boolean values assigned to states discovered within the encoding. For instance, Desk 1 exhibits the disassembly for a operate. Searching for a path from the start of the operate at deal with 0x100003f50 to the deal with 0x100003f9d is unsatisfiable as a result of local_1c is all the time a fair quantity, and the situation guarding the instruction at 0x100003f9d checks for an odd quantity. The disassembly is proven as a result of the default outcome for an unsatisfiable reply is to return Boolean values (true or false) for block addresses. Apart from studying that this explicit try and discover a path is infeasible, we’re nonetheless working to make counterexamples extra helpful.
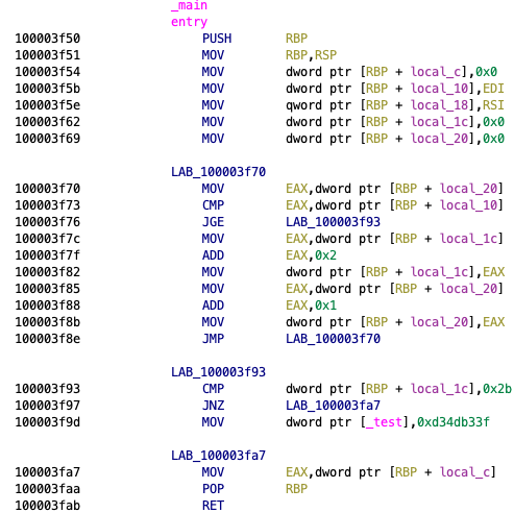
Desk 1: Unsatisfiable instance
ApiAnalyzer
The second software primarily based on GhiHorn, named ApiAnalyzer, makes use of binary path and information stream evaluation to cause about program behaviors. Like its Pharos namesake, the premise of GhiHorn ApiAnalyzer is that fascinating program behaviors will be decided by discovering API operate name sequences that share widespread information. For instance, Determine 3 under exhibits the widespread method to checklist the processes operating on a system utilizing the Home windows Software Assist Features. The API calls used are highlighted in pink.
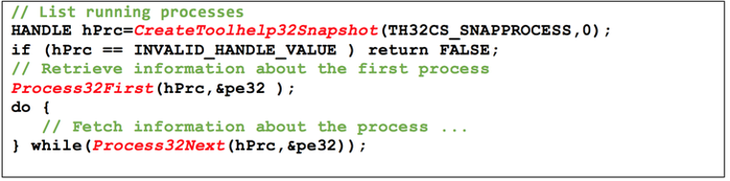
Determine 3: Supply code to iterate by means of operating processes utilizing API calls to Home windows Software Assist Features
The GhiHorn model of ApiAnalyzer formulates a program utilizing the identical hornified management stream graph as PathAnalyzer. This strategy is cheap provided that the API evaluation drawback will be framed as a path reachability drawback with a couple of further constraints particularly that the trail should traverse a selected sequence of API operate calls. Extra particularly the extra constraints are launched to tally the API operate calls coated and to trace variable values handed between API features.
The API name sequences and variables to trace are specified as signatures utilizing a JSON-based format just like that of the Pharos ApiAnalyzer. For instance, a easy signature to hyperlink the opening and shutting of the identical file is proven in Desk 2. Notice that the 2 features function on the identical information: a variable labeled HANDLE. CreateFileA returns the preliminary worth, and CloseHandle should function on that very same worth for a match to exist.
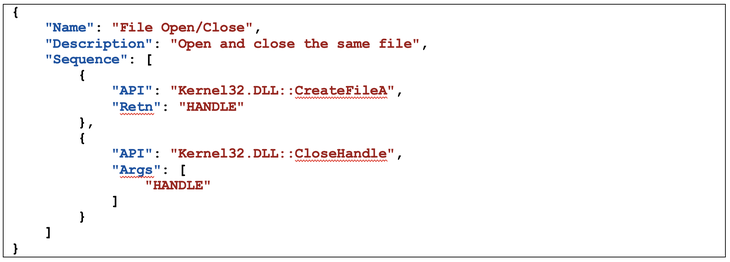
Desk 2 : API signature
The ApiAnalyzer plugin is proven in Determine 4. On this picture, two easy signatures are being looked for: studying and writing the identical file, in addition to opening and shutting the identical file. Each signatures are present in this system, and a solution graph is offered. This graph is proven in Determine 5.
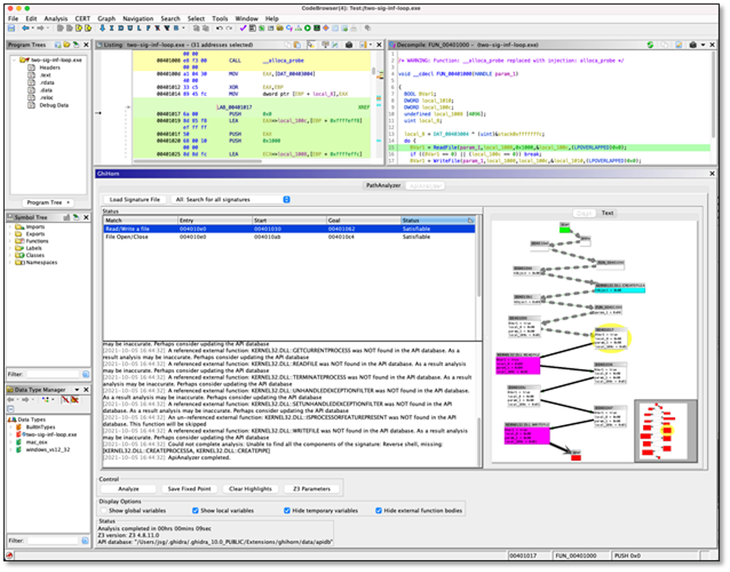
Determine 4: Ghidra ApiAnalyzer person interface
Determine 5: ApiAnalyzer reply graph
ApiAnalyzer’s reply graph is principally the identical because the graph generated by PathAnalyzer. Imported API features for which there’s an implementation are highlighted in cyan. API features for which there is no such thing as a implementation are coloured magenta. As earlier than, the graph contains variable values which can be used to assemble the trail, and the graph can be utilized for navigation within the Ghidra disassembly and decompiler home windows.
The Way forward for GhiHorn
GhiHorn offers the aptitude to cause about program paths in Ghidra. The Horn-based instruments offered by GhiHorn and the tight integration with Ghidra’s person interface makes formal program evaluation instruments accessible to malware analysts and reverse engineers. Future variations of the plugin will proceed to supply new and higher methods to devour outcomes and to mannequin extra advanced code buildings. We additionally plan on producing higher counterexamples to make it extra evident why a path couldn’t be recovered. Lastly, we’re engaged on a greater reminiscence mannequin that higher represents an actual program’s deal with house.
GhiHorn is publicly accessible as a part of the CERT Kaiju Framework. The supply code and construct directions for GhiHorn (and all Kaiju instruments) can be found on GitHub. We welcome strategies for enhancements or for brand spanking new utilities that might be helpful for constructing new instruments to help malware evaluation and reverse engineering.
[ad_2]

