[ad_1]
I’ve two tales to let you know. The primary is a few software program developer at an enormous monetary company. The second is in regards to the safety crew on the similar firm. We are going to undergo the identical cyber incident, from these two views, to get a great perceive of how a malicious actor may attempt to infiltrate a banking utility by means of an admin person, and how the corporate can detect this malicious conduct – utilizing automation as a lot as doable.
The mistaken hyperlink
Let’s begin by taking a look at how an attacker may attempt to infiltrate a banking utility from the within. What’s the easiest method? Sadly, the reply is sort of all the time by means of a person that has entry to the infrastructure and code repositories: an administrator or a developer.
Often, an assault consists of a few phases, popularly generally known as the “kill chain” mannequin:
- Reconnaissance: An attacker selects a goal, for instance our financial institution, and particularly a developer who’s engaged on a selected element of the banking utility that’s of curiosity. The attacker may discover out that he’s utilizing Gmail as private e-mail (by means of a LinkedIn submit). Additionally, he is aware of that GitHub is getting used to commit code, and AWS EKS is used to deploy the code in manufacturing.
- Weaponization: The attacker designs a malware file, which can take over the laptop computer of the developer.
- Supply: Everybody has a weak spot. The attacker designs an e-mail, with a selected attachment, which can trick the developer into opening the file.
- Exploitation: The malware executes upon the developer opening the attachment.
- Set up: The malware installs a backdoor, usable by the attacker.
- Command and Management: The malware permits attacker to have “palms on the keyboard” persistent entry to focus on community.
- Actions on Goal: The attacker will get entry to the backend of the banking utility, for the reason that developer has admin privileges.
Part 7 is clearly the payoff. Earlier than that calamity, there are a number of defenses that must be in place:
- Detect: Decide whether or not an attacker is current.
- Deny: Forestall info disclosure and unauthorized entry.
- Disrupt: Cease or change outbound site visitors (to attacker).
- Degrade: Counter-attack command and management.
- Deceive: Intrude with command and management.
- Include: Community segmentation adjustments
Now trying on the above, you’ll be able to in all probability think about that we need to detect whether or not an attacker is current as quickly as doable. If we don’t know the attacker is there, that’s after we are most weak. There are a lot of prevention and detection options on the market that you should utilize to guard your customers and purposes, nevertheless none might be 100% efficient. That is largely why the pc safety trade exists. And for this reason you will need to use good sources of menace intelligence and expert menace hunters. Let’s dive a bit deeper.
What’s menace intelligence?
Cyber menace intelligence is what cyber menace info turns into as soon as it has been collected, evaluated within the context of its supply and reliability, and analyzed by means of rigorous and structured tradecraft strategies by these with substantive experience and entry to all-source info. Mainly, any info can turn into menace intelligence, and there are various methods to mannequin this info as knowledge construction. One of many extra well-known strategies is STIX (Structured Risk Data Expression), which is a structured language for describing cyber menace info so it may be shared, saved, and analyzed in a constant method. Why is all of this necessary? We are going to cowl that subsequent!
What’s menace searching?
Risk searching is the method of proactively and iteratively looking by means of environments to detect and isolate superior threats that evaded present safety options. Risk Searching is a steady course of, not a one-off process that you just do now and again. The method mainly entails making a speculation over a possible cyber incident, investigating this, uncovering patterns, and eventually enriching your investigation. The speculation will be both confirmed or denied, and the method begins over once more with a brand new or comparable speculation.
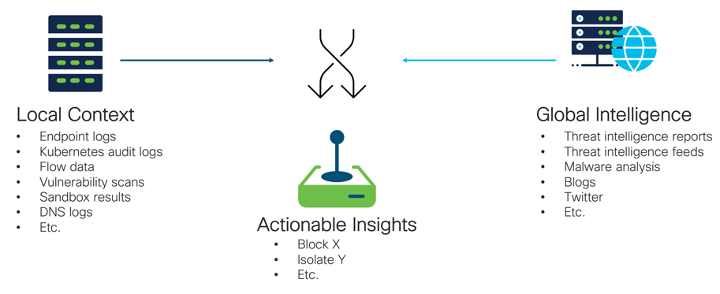
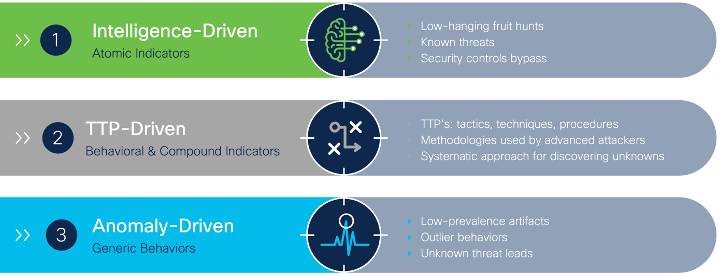
There are three various kinds of menace searching: Intelligence-Pushed, TTP-Pushed (Techniques, Strategies and Procedures), and Anomaly-driven (during which you search for outlier conduct on networks and hosts). The primary relies on atomic indicators (additionally known as observables), like an IP tackle, area identify, file hash, and so on. These are comparatively easy to hunt for, since all you need to search is your logging and inner monitoring methods for a selected indicator. TTP- or anomaly-driven are harder, since you’re looking for a selected or outlying sample of conduct. That is clearly extra advanced than simply looking your logging for a selected indicator. Let’s concentrate on intelligence-driven menace hunts for now.
Since Risk Searching is all about gathering knowledge from native/inner monitoring methods and cross-referencing this with international menace intelligence, it’s of upmost significance that you would be able to mix totally different units of data sources, whether or not you’re looking out for an SHA256 file hash or a conduct sample. There are a lot of instruments, like Cisco SecureX, that may assist with this. For instance, SecureX integrates with many Cisco and third-party safety instruments, and interprets returned knowledge right into a coherent knowledge mannequin known as Cisco Risk Intelligence Mannequin (CTIM). CTIM is a simplified model of the earlier-mentioned STIX (there’s additionally a CTIM-STIX converter accessible). This translation element is essential within the fast investigation of incidents, or when menace searching. SecureX presents a built-in device, Risk Response, to do that in a graphical manner, however it additionally presents wealthy APIs which might automate components of the menace searching course of.
Discovering contemporary indicators of compromise on your hypotheses
The web comprises many free sources of menace intelligence that can be utilized, along with Cisco’s menace intelligence analysis group, Talos. There’s a large group on the market that shares new indicators associated to new cyber assaults and malware campaigns. There’s loads on the market, and it’s necessary to maintain updated with this intelligence. However how?
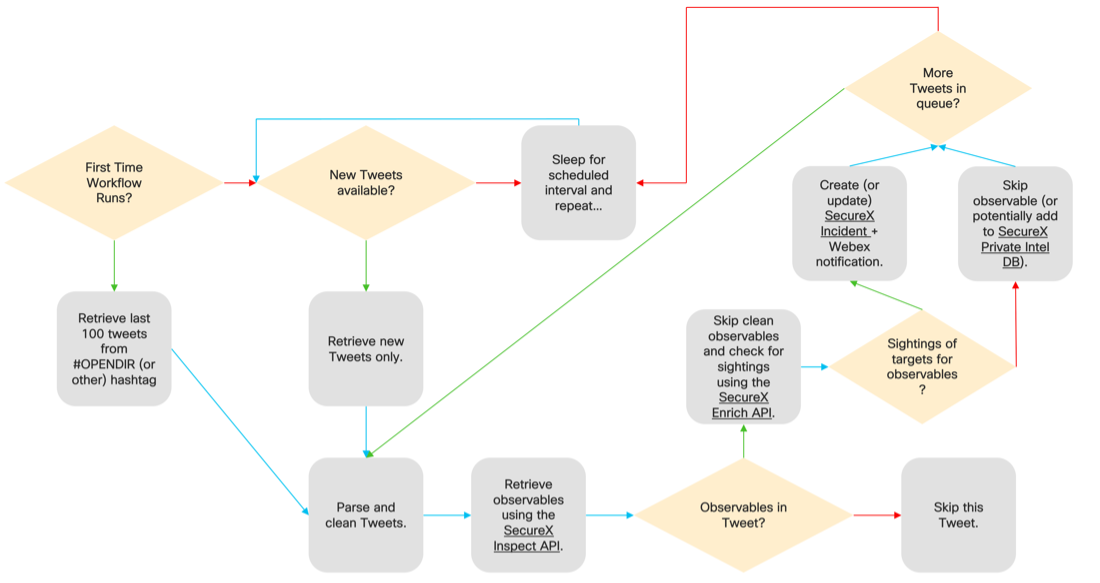
A method is to make use of the SecureX API (Examine and Enrichment). It may well “harvest” contemporary indicators, and in addition uncover inner safety occasions from many sources – like Twitter. Over on Twitter, the #opendir Twitter hashtag is utilized by many menace intelligence researchers to submit their findings on new threats. It is a good instance of a type of free sources of menace intelligence that may be discovered on the web.
Since nobody has the time to learn all of those Tweets, verify all of their safety instruments for hits, and take motion on them, I need to present you an automatic manner of doing this, utilizing SecureX Orchestration. However first, let’s get again to our story of the developer on the banking company.
Suppose that our developer certainly fell for the e-mail that was crafted by the attacker, and by chance executed malware on his laptop computer. The file appeared to be innocent, and the developer didn’t see this as something malicious and continues together with his day. In the meantime, the attacker is now inside, and is ready for the correct second to leap over from the laptop computer into the appliance infrastructure of the banking utility. When the developer connects to their AWS EKS cluster, that is the place the an infection occurs. The attacker connects to his command and management server and begins to exfiltrate knowledge, or different malicious actions. Now since his command and management server isn’t recognized but as being a malicious vacation spot, no safety controls are blocking this connection. Fortunately a safety researcher simply discovered about this by means of an investigation and tweets about it. That is the place our automations kick in!
Automating your menace hunts
Utilizing the Twitter Search API we are able to truly retrieve the most recent tweets that use the #opendir hashtag. Utilizing this, together with the SecureX API to extract and enrich observables, we are able to discover out if now we have sightings of this in our environments. Under is an summary of this automation workflow in a movement diagram:
As you’ll be able to see, we are actually utterly automating our menace searching, by robotically ingesting attention-grabbing tweets, parsing them and checking our surroundings. Based mostly on this, the safety crew of the monetary company will get an alert that considered one of their companies made a connection to an observable which is talked about in a tweet. What to do subsequent to nip this within the bud, although? That we’ll discover out in Half 2 of this story, coming quickly!
We’d love to listen to what you suppose. Ask a query or go away a remark beneath.
And keep linked with Cisco DevNet on social!
LinkedIn | Twitter @CiscoDevNet | Fb | Developer Video Channel
Share:
[ad_2]