[ad_1]
A rising distant workforce and a wave of resignations in recent times have exacerbated dangers to an organization’s confidential info from insider threats. A current report from Workforce Safety Software program supplier DTEX Methods highlights the rise of insider threats on account of the development towards working from anyplace, catalyzed by the pandemic. In accordance with current information, 5 million Individuals at present outline themselves as digital nomads or gig employees, and surveys constantly discover that staff are opting to maintain their versatile working patterns after the pandemic.
These tendencies current cybersecurity challenges, notably with respect to insider menace. “Whereas most industries made the shift to distant work because of the pandemic, it created new assault surfaces for cybercriminals to benefit from, akin to dwelling gadgets getting used for enterprise functions,” Microsoft defined of their current Digital Protection Report.
The SEI CERT Division defines insider menace as “the potential for a person who has or had approved entry to a corporation’s vital belongings to make use of their entry, both maliciously or unintentionally, to behave in a approach that might negatively have an effect on the group.” Though the strategies of assault can fluctuate, the first forms of incidents—theft of mental property (IP), sabotage, fraud, espionage, unintentional incidents, and misuse—proceed to place organizations in danger. In our work with private and non-private trade, we proceed to see that insider threats are influenced by a mixture of technical, behavioral, and organizational points.
On this weblog submit, I introduce our newly revealed seventh version of the Widespread Sense Information to Mitigating Insider Threats, and spotlight and summarize a brand new greatest observe that we have now added to this version of the information: Observe 22, Be taught from Previous Insider Risk Incidents. Gathering such information, analyzing it, and interesting with exterior information-sharing our bodies can bolster a corporation’s insider risk-mitigation program. This exercise is important to making sure that analytics function successfully and that threat determinations are being made utilizing one of the best accessible information. It additionally varieties the muse for return-on-investment instances to be made for insider menace packages.
What’s New within the Newest Information
The Widespread Sense Information consists largely of twenty-two greatest practices that organizations can use to handle insider threat. Every observe contains suggestions for fast wins and high-impact options, implementation steerage, and extra assets. The practices are additionally mapped to the CERT Resilience Administration Mannequin (CERT-RMM) and safety and privateness requirements akin to, amongst others, ISO/IEC 27002, the Nationwide Institute of Requirements and Expertise (NIST) Cybersecurity Framework, and—new to this version—the NIST Privateness Framework. These mappings assist establish the alignment between insider menace packages and broader cybersecurity, privateness, and risk-management frameworks, which is vital to fostering enterprise-wide collaboration.
The Widespread Sense Information springs from greater than 20 years of insider menace analysis on the SEI, a lot of it underpinned by the CERT Division’s insider menace database, which is drawn from public information of greater than 3,000 insider menace incidents. In 2005, the U.S. Secret Service sponsored the SEI’s first revealed research of the subject. Since then, CERT analysis has helped mature the organizational practices for mitigating insider threats and managing their threat. The information has developed with modifications within the menace panorama, technological mitigations, and shifts in data-privacy insurance policies. The seventh version continues this evolution with new and up to date practices, improved structure and imagery to boost usability, and extra refined phrases. It has additionally added analysis from administration science to its multidisciplinary strategy.
Studying from Previous Insider Risk Incidents
New to the seventh version of the information is Greatest Observe 22, Be taught from Previous Insider Risk Incidents. The observe provides steerage for growing a repository of insider tendencies inside a corporation and its sector. Within the the rest of this submit, I current excerpts and summaries from the complete description of the observe within the information.
Organizations that study from the previous are higher ready for the longer term. Understanding how earlier incidents unfolded, whether or not within the group or elsewhere, supplies essential perception into the efficacy of present insider risk-management practices; potential gaps in prevention, detection, and response controls; and areas of emphasis for insider menace consciousness and coaching efforts.
Creating the potential to gather and analyze insider incident information is a key element of an efficient insider threat administration program (IRMP) and may inform its operations, together with threat quantification, evaluation, and incident response.
Designing an Insider Incident Repository
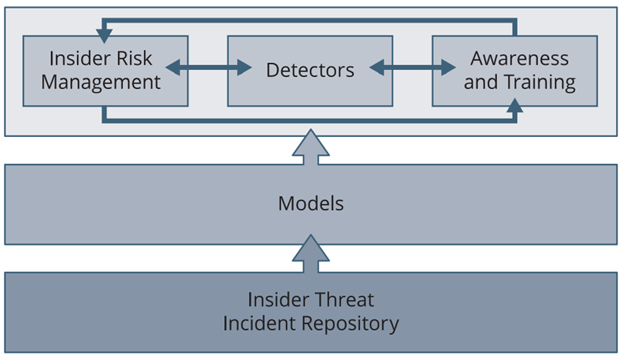
Determine 1 beneath exhibits how an insider menace incident repository supplies a basis for organizational preparedness.
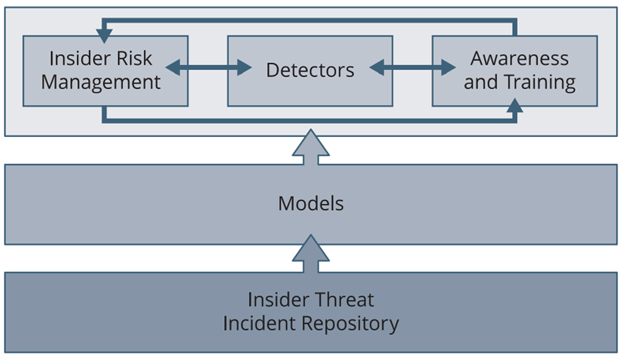
Determine 1: How Knowledge About Earlier Insider Incidents Drives Organizational Preparedness
Having info accessible about earlier insider incidents allows the group to derive insider menace fashions, make threat choices based mostly on historic info, and use examples of insider menace incidents for consciousness campaigns and coaching. Those that are accountable for threat administration should acquire this info. They usually seek for examples as the necessity arises. This reactive strategy is time consuming, nonetheless, and can lead to duplication of effort each time earlier incident information is required. To minimize these points, the group ought to design its personal insider menace incident repository.
Inner growth of an insider menace incident repository helps inform IRMP operations and, in flip, improves operational resilience extra broadly. For instance, supply-chain safety administration processes may also be knowledgeable by earlier incidents captured in an insider menace incident repository. Furthermore, the repository may help restrict repute threat by supporting the sooner detection of incidents. Aggregated information from an insider menace incident repository can spotlight potential high-risk networks or environments the place enhanced monitoring or specialised instruments ought to be deployed, or the place extra mitigations ought to be carried out.
Creating and sustaining an insider menace incident repository may be as easy or complicated as required to fulfill the group’s wants. In all instances, leveraging current requirements and practices to implement incident assortment and data sharing makes the trouble related to these actions extra manageable.
Within the easiest kind, an insider menace incident repository is a group of knowledge (e.g., recordsdata, media experiences) that’s organized in a repository. For instance, some organizations have a de-facto incident repository of inside incidents of their case-management system. A extra complicated repository instance is when the group makes use of the formal knowledge-management roles and obligations of its workforce to gather and retailer info in a devoted repository.
No matter its format, a number of knowledge-management actions are concerned in growing and sustaining an insider menace incident repository:
- Outline the aim and use instances for the insider menace incident repository—The repository is a device for assembly operational wants. These wants ought to be documented in order that the repository stewards can be sure that the repository is developed and maintained to fulfill these wants. Designers of the preliminary repository should think about each the insights wanted from the information within the repository and use instances that present how customers must work together with the repository (e.g., analyze information straight on the repository platform, pull info into separate evaluation instruments).
- Construct a container for an insider menace incident repository—The repository’s container could be a database, code repository, doc repository, or incident tracker/administration system. The container ought to have a documented construction that displays the information wants to be used instances. These use instances ought to be documented in an information code e-book that (1) describes the information in order that customers can perceive what it tells them and (2) defines the information expectations for the repository. For instance, if the repository is a database, then the code e-book ought to present structural details about every area (e.g., datatype). If the repository incorporates solely recordsdata, then the code e-book ought to outline expectations for various file sorts. The group must also set up expectations for the repository’s use and upkeep (e.g., entry management, replace schedules, information cleansing, and allowed and prohibited info akin to whether or not or not personally identifiable info or disciplinary actions are permissible information factors).
- Acquire info—To totally help the IRMP, the data collected ought to embrace each inside and exterior sources. Examples of exterior sources which might be publicly accessible embrace court docket information, media experiences, social media on-line boards, and information-security bulletins. This info would possibly embrace incident-specific info, or greatest observe or development info that may be utilized to updating repository administration. For inside info, the group ought to seize info from incident investigations and insights gathered from autopsy evaluations of responses to incidents.
- Share incident information as acceptable—Because the objective of the insider menace incident repository is to assist the group and its members make higher insider threat choices, it is crucial that the repository be used to derive insights, and that these insights are shared with the individuals who want them. Since info from the group is seldom sufficient to know the breadth of insider threats, you will need to additionally collect and share incident information with the broader counter-insider menace practitioner group. Along with offering normal insider threat insights, sharing this info can result in the trade of indicators of compromise, instruments, ways, or procedures, and even approaches for prevention, detection, mitigation, or response.
Perception that advantages the group may be derived from an insider menace incident repository in some ways. Essentially the most simple approach is utilizing incidents as case research or examples for rising workforce consciousness of insider menace and coaching the workforce to acknowledge and reply to insider menace. Different methods embrace root-cause evaluation, abstract statistics, development identification, and correlations. Every of those has its personal use instances for the insights they supply.
Every group ought to carry out some foundational analyses of its repository information, particularly the components which might be associated to incidents contained in the group and inside its information-sharing partnerships. Foundational practices for deriving insights from repository information may be qualitative or quantitative. An instance of a qualitative foundational observe is creating incident-repository case research to be used in coaching and consciousness actions. A quantitative instance is offering tendencies on how the quantity and severity of insider incidents are altering over time, which might affect menace probability and influence calculations.
Performing superior evaluation practices requires specialised information or instruments. These practices can allow robotically processing (e.g., ingesting) of incident information into the insider menace incident repository. They’ll additionally present insights which might be extra complicated to derive, akin to complicated (or hidden) correlations between information factors. For organizations utilizing technical controls, akin to consumer exercise monitoring or consumer and entity behavioral analytics, superior analyses ought to be used to refine and implement the menace fashions and risk-scoring algorithms the controls present.
Many organizations that depend on out-of-the-box configurations of those controls rapidly discover that they need to tailor them to their group’s particular threat urge for food, priorities, and cultural norms. An insider menace incident repository is a crucial useful resource that a corporation can use to make sure that the IRMP’s detective functionality aligns (and continues to remain aligned) with the repeatedly altering menace panorama.
Stopping Insider Incidents
Within the COVID period, with rising numbers of staff working remotely, mitigating insider menace is extra essential than ever. The 22 suggestions within the Information—together with the one described on this submit—are designed for choice makers and stakeholders to work collectively to successfully stop, detect, and reply to insider threats. In a future submit, I’ll map the Information to the NIST Privateness Framework.
[ad_2]