[ad_1]
Overview
Builders now not simply construct purposes, but additionally play important roles for infrastructure operations in DevOps and infrastructure as code (IaC) areas. In these conditions, you may additionally be chargeable for the operation of take a look at infrastructure that runs on a managed service comparable to Pink Hat OpenShift on IBM Cloud. Guaranteeing its safety and regulatory compliance can also be vital and chances are you’ll wish to automate such work. That automation might be facilitated by an OpenShift Operator known as Compliance Operator, which is a compliance standing examine engine for OpenShift clusters.
Nevertheless, it’s not easy to make use of Compliance Operator for an OpenShift cluster operating on IBM Cloud as a result of its set up is custom-made to supply it as managed service. Because of this, a few of default guidelines and parameters don’t match the precise state and such mismatches trigger false positives. Due to this fact, it’s essential to create a tailor-made profile to align the custom-made set up.
Half 1: Introduction of guidelines, variables, profiles, and tailor-made profiles
Guidelines and variables
All the foundations verified by the Compliance Operator are outlined within the ComplianceAsCode/content material mission repository. For instance, think about the rule with the kubelet_eviction_thresholds_set_hard_imagefs_available ID as follows:
git clone https://github.com/ComplianceAsCode/content material
...
cd content material
tree purposes/openshift/kubelet
purposes/openshift/kubelet
...
├── kubelet_eviction_thresholds_set_hard_imagefs_available
│ ├── rule.yml
│ └── checks
...
├── var_kubelet_evictionhard_imagefs_available.var
...
The rule ID is represented by the listing title, whereas the precise rule is outlined in rule.yml beneath the rule listing:
...
title: 'Guarantee Eviction threshold Settings Are Set - evictionHard: imagefs.out there'
...
template:
title: yamlfile_value
vars:
filepath: /and so on/kubernetes/kubelet.conf
yamlpath: ".evictionHard['imagefs.available']"
xccdf_variable: var_kubelet_evictionhard_imagefs_available
For this rule, the anticipated parameter worth within the /and so on/kubernetes/kubelet.conf YAML file is specified at yamlpath with a JSONPath expression known as .evictionHard['imagefs.available'], and it ought to match the worth of the var_kubelet_evictionhard_imagefs_available configuration variable. The configuration variable worth is saved in a distinct file; on this case, the file is var_kubelet_evictionhard_imagefs_available.var beneath the kubelet listing:
...
title: 'Configure Kubelet EvictonHard Picture FS Avilable'
...
sort: string
operator: equals
choices:
default: "10%"
5pc: "5%"
10pc: "10%"
15pc: "15%"
20pc: "20%"
With the variable values illustrated above, the results of this rule evaluation is a PASS if .evictionHard['imagefs.available'] is the same as "10%" (the default worth).
Profiles
In a typical use case, an inside compliance officer or an exterior auditor requests validation towards business regulation baselines or finest practices comparable to NIST SP 800-53 reasonable or CIS Benchmarks. These regulation baselines and finest practices are represented within the ComplianceAsCode mission as a profile. For instance, you will discover the NIST 800-53 Average-Influence Baseline for Pink Hat OpenShift outlined in ocp4/profiles/reasonable.profile, and the CIS Pink Hat OpenShift Container Platform 4 Benchmark outlined in ocp4/profiles/cis-node.profile as follows:
...
title: 'CIS Pink Hat OpenShift Container Platform 4 Benchmark'
...
picks:
...
- kubelet_eviction_thresholds_set_hard_imagefs_available
...
Every profile comprises its particular algorithm. The next diagram illustrates the relationships between the foundations and the profiles.
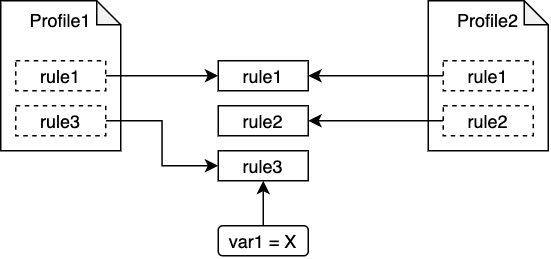
Within the ComplianceAsCode/content material repository, many profiles are already outlined for well-known, business rules. See the Compliance Operator Customized Useful resource Definitions documentation for particulars on how admins and compliance engineers can specify a profile for his or her Compliance Operator scans through the use of ComplianceScan or ComplianceSuite objects.
Verify outcomes
The examine outcomes for every profile are registered as compliancecheckresult assets. Its title consists of the next three components:
${profile_name}-${role_name}-${rule_name}
profile_nameis the title of theProfileorTailoredProfilespecified within theScanSettingBinding,ComplianceScan, orComplianceSuiteuseful resource.role_nameis the.roleswithin theScanSettinguseful resource.rule_nameis the rule ID the place its underscores (_) had been changed with hyphens (-).
Due to this fact, for instance, a compliancecheckresult useful resource named ocp-worker-kubelet-eviction-thresholds-set-hard-imagefs-available is the results of a rule during which the rule_id is kubelet_eviction_thresholds_set_hard_imagefs_available.
You may specify a number of profiles (and tailor-made profiles) for a single cluster. For instance, if you configure the profiles named profile1 and profile2 for a rule known as rule1, you will note two compliancecheckresult assets with names which can be profile1_rule1 and profile2_rule1 for every profile. The outcomes might differ as a result of every profile has its personal customized variables, which we’ll talk about in Half 3.
TailoredProfile
As you could have seen, the Compliance Operator guidelines and profiles are written in YAML format. Nevertheless, the Compliance Operator scans are executed in a Kubernetes cluster and its nodes with the oscap command, which solely accepts guidelines and profiles outlined in XCCDF format. Due to this fact, it’s essential to compile the foundations and the profiles which can be in YAML format into an XCCDF knowledge stream file previous to utilizing Compliance Operator, and package deal the compiled contents as a Docker picture, which is sometimes called the content material picture. While you try to customise the foundations and the profiles, it’s essential to rebuild the XCCDF knowledge stream information as a content material picture along with modifying the contents.
To mitigate the customization workload, you possibly can customise the profile and the variables through the use of a Compliance Operator mechanism known as TailoredProfile, which takes much less work than constructing your personal content material picture. With a tailor-made profile, you possibly can disable guidelines chosen in predefined profiles and set customized values for XCCDF variables. The next diagram describes the relationships between a predefined profile, a tailor-made profile, guidelines, and variables. On this instance, solely rule3 and the var1 = Y customized variable are utilized if you use this tailor-made profile for the Compliance Operator scan.
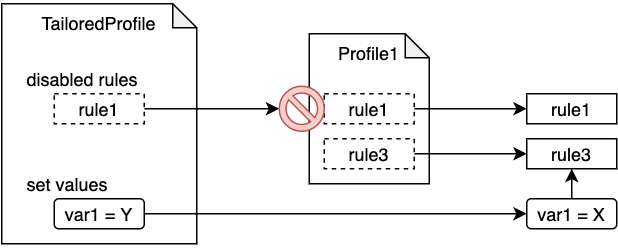
A tailor-made profile might be utilized utilizing ScanSetting and ScanSettingBinding assets. Study extra within the TailoredProfile part and ScanSetting and ScanSettingBinding part of the Customized Useful resource Definitions documentation for Compliance Operator.
Half 2: Tailoring course of
The precise tailoring course of consists of the next steps:
- Choose a predefined (often known as a base) profile (for instance,
cis-node), and carry out a scan with that profile. -
Get the
FAILrule names with the next command:oc get compliancecheckresult | grep FAILIt’s best to see outcomes much like the next:
ocp-master-kubelet-eviction-thresholds-set-hard-imagefs-available FAIL medium ocp-worker-kubelet-eviction-thresholds-set-hard-imagefs-available FAIL medium -
For every
FAILrule, when the remediation is just not an possibility, think about disabling the rule itself or customizing the variables of the rule in a tailor-made profile.On this step, it’s essential to first discover the precise examine logic of a rule. As we described earlier within the Verify outcomes part, you possibly can extract
rule_idfrom the title of acompliancecheckresultuseful resource. Through the use of therule_id, now you can discoverrule.yml, which comprises the precise examine logic for that rule. To take action, use the next command:cd content material # go to ComplianceAsCode/content material listing discover . -name kubelet_eviction_thresholds_set_hard_imagefs_available./purposes/openshift/kubelet/kubelet_eviction_thresholds_set_hard_imagefs_available cat ./purposes/openshift/kubelet/kubelet_eviction_thresholds_set_hard_imagefs_available/rule.yml ... title: 'Guarantee Eviction threshold Settings Are Set - evictionHard: imagefs.out there' ... template: title: yamlfile_value vars: filepath: /and so on/kubernetes/kubelet.conf yamlpath: ".evictionHard['imagefs.available']" xccdf_variable: var_kubelet_evictionhard_imagefs_availableIf a examine logic comprises references to a variable, you will discover the file that defines the variable by linking collectively the
xccdf_variablestring with the.varsuffix. For instance, the XCCDF variable known asvar_kubelet_evictionhard_imagefs_availablemight be discovered within thevar_kubelet_evictionhard_imagefs_available.varfile:cd content material # go to ComplianceAsCode/content material listing discover . -name var_kubelet_evictionhard_imagefs_available.var./purposes/openshift/kubelet/var_kubelet_evictionhard_imagefs_available.varLastly, create the tailor-made profile useful resource by specifying the disabled guidelines and new anticipated values. The rule title conference is
${profile_bundle_name}-${rule_name}:${profile_bundle_name}is oftenocp4as a result of OpenShift guidelines are owned by anocp4profile bundle by default.-
${rule_name}is a hyphen-joined title (for instance,kubelet-eviction-thresholds-set-hard-imagefs-available), whereas a rule ID is a underscore-joined title (for instance,kubelet_eviction_thresholds_set_hard_imagefs_available).The next
TailoredProfileinstance reveals how one can specify a customized worth for thevar_kubelet_evictionhard_imagefs_availablevariable and how one can disable thefile_permissions_kube_apiserverrule. Observe that the rule and variable names begin withocp4-, whereas the underscores (_) within the names are changed with hyphens (-).apiVersion: compliance.openshift.io/v1alpha1 type: TailoredProfile metadata: title: my-tailored-profile spec: setValues: - title: ocp4-var-kubelet-evictionhard-imagefs-available rationale: "stricter than default" worth: "5%" disableRules: - title: ocp4-file-permissions-kube-apiserver rationale: Goal file is hidden and no have to examine extends: ocp4-cis-node title: CIS Benchmark for OpenShift on IBM Cloud
Half 3: Executing concurrent scans of tailor-made profiles of the identical base profile
Assume that two compliance engineers tailor-made the identical base profile, cis-node.profile, as mycis-node-tailored-profile1 and mycis-node-tailored-profile2 with completely different values for the ocp4-var-kubelet-evictionhard-imagefs-available variable. The Compliance Operator checks the foundations in each tailor-made profiles based on the set anticipated variable values, and shops two outcomes for one rule as ComplianceCheckResults assets.
For instance, the examine outcomes for the kubelet-eviction-thresholds-set-hard-imagefs-available rule are saved as follows (word that the naming conference of ComplianceCheckResults is ${profile_name}-${role_name}-${rule_name} as described above):
NAME STATUS SEVERITY
mycis-node-tailored-profile1-worker-kubelet-eviction-thresholds-set-hard-imagefs-available PASS medium
...
mycis-node-tailored-profile2-worker-kubelet-eviction-thresholds-set-hard-imagefs-available FAIL medium
Conclusion
The OpenShift Compliance Operator offers an adaptive means for an infrastructure operator to run compliance scans and confirm whether or not a Kubernetes cluster and its underlying nodes adjust to a number of specified regulatory profiles.
Our subsequent step is to facilitate the combination of Compliance Operator into the IBM Cloud Safety and Compliance Heart for a compliance officer to handle safety and compliance controls and regulatory profiles throughout the IBM Cloud platform, together with Kubernetes, from a unified dashboard.
[ad_2]