[ad_1]
AWS Management Tower makes it simpler to arrange and handle a safe, multi-account AWS surroundings. AWS Management Tower makes use of AWS Organizations to create what is known as a touchdown zone, bringing ongoing account administration and governance based mostly on our expertise working with 1000’s of consumers.
In the event you use AWS CloudFormation to handle your infrastructure as code, you’ll be able to customise your AWS Management Tower touchdown zone utilizing Customizations for AWS Management Tower, an answer that helps you deploy customized templates and insurance policies to particular person accounts and organizational models (OUs) inside your group.
However what if you happen to use Terraform to handle your AWS infrastructure?
At present, I’m completely happy to share the provision of AWS Management Tower Account Manufacturing unit for Terraform (AFT), a brand new Terraform module maintained by the AWS Management Tower crew that permits you to provision and customise AWS accounts via Terraform utilizing a deployment pipeline. The supply code for the event pipeline could be saved in AWS CodeCommit, GitHub, GitHub Enterprise, or BitBucket. With AFT, you’ll be able to automate the creation of absolutely useful accounts which have entry to all of the assets they should be productive. The module works with Terraform open supply, Terraform Enterprise, and Terraform Cloud.
Let’s see how this works in follow.
Utilizing AWS Management Tower Account Manufacturing unit for Terraform
First, I create a primary.tf file that makes use of the AWS Management Tower Account Manufacturing unit for Terraform (AFT) module:
The primary six parameters are required. As a prerequisite, I have to cross the ID of 4 AWS accounts in my AWS group:
ct_management_account_id– AWS Management Tower administration accountlog_archive_account_id– Log Archive accountaudit_account_id– Audit accountaft_management_account_id– AFT administration account
Then, I’ve to cross two AWS Areas:
ct_home_region– The Area from which this module can be executed. This have to be the identical Area the place AWS Management Tower is deployed.tf_backend_secondary_region– The backend major Area is identical because the AFT Area. This parameter defines the secondary Area to duplicate to. AFT creates a backend for state monitoring for its personal state. It is usually used for Terraform when utilizing the open-source model.
The opposite parameters are optionally available and are set to their default worth within the earlier primary.tf file:
terraform_distribution– To pick out between Terraform open supply (default), Enterprise, or Cloudvcs_provider– To decide on the model management system to make use of between AWS CodeCommit (default), GitHub, GitHub Enterprise, or BitBucket.
These characteristic flags are disabled by default and could be omitted except you wish to allow them:
aft_feature_delete_default_vpcs_enabled– To robotically delete the default VPC for brand spanking new accounts.aft_feature_cloudtrail_data_events– To allow AWS CloudTrail information occasions for brand spanking new accounts. Remember that this feature, often required for compliance in extremely regulated environments, can have an effect in your prices.aft_feature_enterprise_support– To robotically enroll new accounts with Enterprise Help (you probably have an Enterprise Help Plan).
First, I initialize the mission and obtain the plugins:
Then, I take advantage of AWS Single Signal-On to log in with the AWS Management Tower administration account and begin the deployment:
I affirm with a sure and, after a while, the deployment is full.
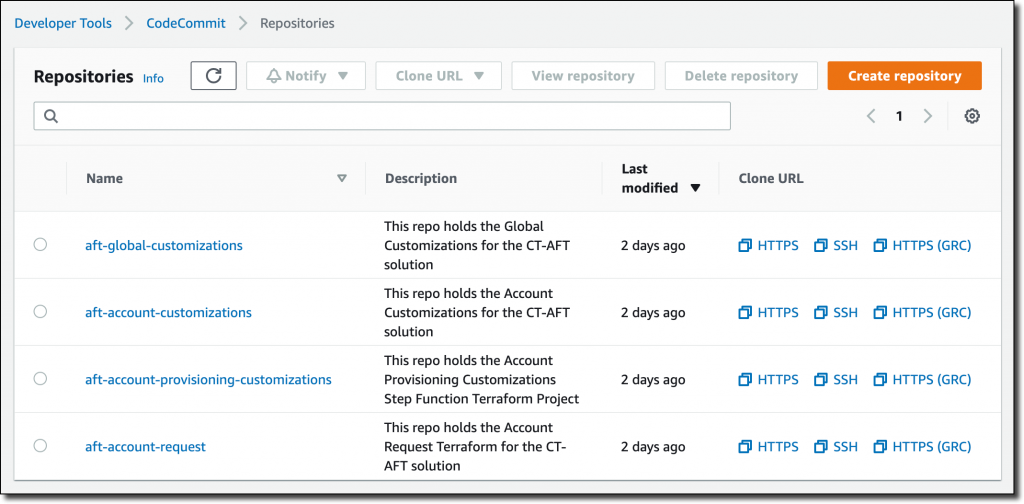
Now, I take advantage of AWS SSO once more to log in with the AFT administration account. Within the AWS CodeCommit console, I discover 4 repositories that I can use to customise the accounts created with AFT.
These repositories are utilized by pipelines managed by AWS CodePipeline to automate the account creation:
aft-account-request– That is the place I place requests for accounts provisioned and managed by AFT.aft-global-customizations– I can use this repository to customise all provisioned accounts with customer-defined assets. The assets could be created via Terraform or via Python.aft-account-customizations– Right here, I can customise provisioned accounts relying on the worth of theaccount_customizations_nameparameter within theaft-account-requestrepository. On this method, I can create totally different units of customizations relying on the position the account can be used for.aft-account-provisioning-customizations– This repository makes use of AWS Step Capabilities to customise the provisioning course of for brand spanking new accounts and simplify the combination with further environments. State machines can use AWS Lambda capabilities, Amazon Elastic Container Service (Amazon ECS) or AWS Fargate duties, customized actions hosted both on AWS or on-premises, or Amazon Easy Notification Service (SNS) and Amazon Easy Queue Service (SQS) to speak with exterior functions.
Presently, these 4 repositories are all empty. To begin, I take advantage of the code within the sources/aft-customizations-repos folder within the GitHub repo of the AFT Terraform module.
Utilizing the instance within the aft-account-request repository, I put together a template to create a few AWS accounts. One of many two accounts is for a software program developer.
To assist software program builders be productive rapidly, I create a selected account customization. Within the template, I set the parameter account_customizations_name equal to developer-customization.
Then, within the aft-account-customizations repository, I create a developer-customization folder the place I put a Terraform template to robotically create an AWS Cloud9 EC2-based growth surroundings for brand spanking new accounts of that kind. Optionally, I can prolong that with my Python code, for instance, to invoke inner or exterior APIs. Utilizing this method, all new accounts for software program builders can have their growth surroundings prepared as they undergo the supply pipeline.
I push the modifications to the primary department (first for the aft-account-customizations repository, then for the aft-account-request). This triggers the execution of the pipeline. After a couple of minutes, the 2 new accounts are prepared for use.
You’ll be able to customise accounts created by AFT based mostly in your distinctive necessities. For instance, you’ll be able to present every account with its personal particular safety setup (reminiscent of IAM roles or safety teams) and storage (for instance, pre-configured Amazon Easy Storage Service (Amazon S3) buckets).
Availability and Pricing
AWS Management Tower Account Manufacturing unit for Terraform (AFT) works in any Area the place AWS Management Tower is obtainable. There are not any further prices when utilizing AFT. You pay for the providers utilized by the answer. For instance, once you arrange AWS Management Tower, you’ll start to incur prices for AWS providers configured to arrange your touchdown zone and obligatory guardrails.
When constructing this resolution, we labored along with HashiCorp. Armon Dadgar, HashiCorp Co-Founder and CTO, instructed us: “Managing cloud environments with a whole lot or 1000’s of customers generally is a complicated and time-consuming course of. Utilizing a software program supply pipeline integrating Terraform and AWS Management Tower makes it simpler to attain constant governance and compliance necessities throughout all accounts.” For extra info on our collaboration, see HashiCorp Groups with AWS on New Management Tower Account Manufacturing unit for Terraform.
The pipeline offers an account creation course of that screens when account provisioning is full after which triggers further Terraform modules to reinforce the account with additional customizations. You’ll be able to configure the pipeline to make use of your individual customized Terraform modules or choose from pre-published Terraform modules for widespread merchandise and configurations.
— Danilo
[ad_2]