[ad_1]
Latest occasions, resembling these affecting SolarWinds and Log4j, exhibit the size of cybersecurity disruption that may end result from an absence of vigilance in relation to the administration of third-party elements in software program techniques. As techniques have turn out to be more and more software program intensive and sophisticated, these third-party elements have turn out to be widespread, and so they require an built-in acquisition, engineering, improvement, and operational focus to make sure ample safety and resilience. Nonetheless, a latest report by SecurityScorecard examined greater than 230,000 organizations and located that the techniques of 98 p.c of them have had third-party software program elements breached inside the previous two years.
In mild of those realities, these charged with managing software program techniques should think about the dependencies and dangers of third-party software program in new methods and collaborate with enterprise consultants to develop new strategies for figuring out and managing potential dangers. A software program invoice of supplies (SBOM) can facilitate these duties. This SEI Weblog submit highlights our work to construct on the SEI’s Acquisition Safety Framework for provide chain danger administration and tailor it to be used in third-party software program administration, which resulted within the SEI SBOM Framework.
Software program and Provide Chain Cybersecurity Challenges
Third-party danger is a serious problem for organizations looking for to restrict their publicity to cybersecurity dangers. As a result of third-party software program has turn out to be such an necessary issue within the safety of enormous, complicated techniques, managing relationships with third-party distributors is vital for achievement.
Organizations usually have a restricted view into the elements, sources, and suppliers concerned in a system’s improvement and ongoing operation. An important side of addressing provider danger is having the ability to entry details about provider inputs and their relative significance, after which handle mitigations to cut back danger.
Nonetheless, a program can not successfully handle cybersecurity dangers alone, as a result of safety and provider danger administration usually lie outdoors this system’s scope. Furthermore, vital info vital for cyber danger administration is commonly distributed amongst many paperwork, resembling a program safety plan (PPP), cybersecurity plan, system improvement plan (SDP), or provide chain danger administration plan. Likewise, many actions vital to managing cyber dangers are distributed amongst models all through the group. These models should collaboratively handle cyber danger administration throughout the lifecycle and provide chain and combine this work with program danger administration (Determine 1).
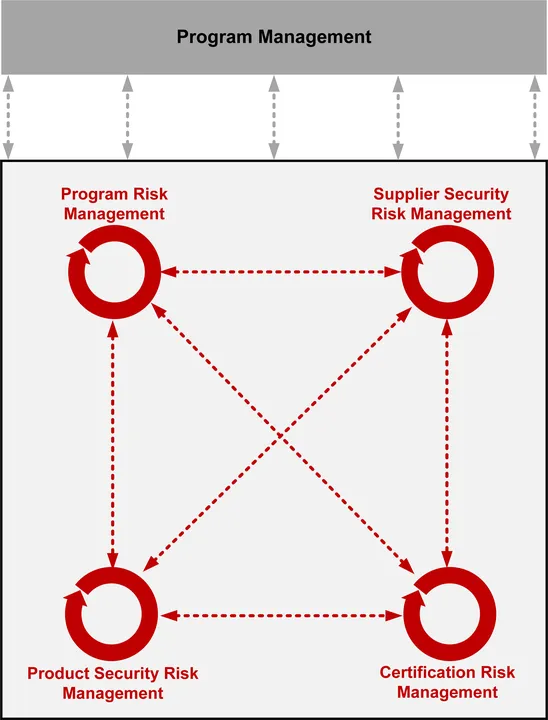
Determine 1: Managing Threat Requires an Built-in, Collaborative, Knowledge-Pushed Method Throughout the Lifecycle and Provide Chain.
SBOMs and Alternatives for Their Use
The U.S. Division of Commerce (DOC) defines an SBOM as follows in its paper The Minimal Components for a Software program Invoice of Supplies (SBOM):
An SBOM is a proper document containing the main points and provide chain relationships of varied elements utilized in constructing software program.
Program mangers more and more depend on SBOM-driven strategies for gathering details about the elements, and their sources or suppliers, that comprise software program techniques. Early efforts to innovate SBOM strategies centered on defining knowledge parts and managing identified vulnerabilities. Because of this, a number of info and danger administration strategies have emerged that determine vital knowledge and join assist groups, suppliers, and stakeholders to cut back danger.
The SBOM gained added significance with Govt Order (EO) 14028, Bettering the Nation’s Cybersecurity. Issued on Might 12, 2021, EO 14028 requires U.S. authorities businesses to boost software program provide chain safety and integrity, with a precedence on addressing vital software program. s A key part to reaching software program provide chain safety and integrity is transparency, and SBOMs for vital software program can assist set up this transparency within the software program provide chain. This is the reason EO 14028 requires requirements, procedures, and standards for offering SBOMs for merchandise instantly or publishing them on a public web site.
Our survey of SBOM publications and steerage revealed a robust emphasis on defining the content material and format of SBOMs. Whereas establishing a typical for SBOM content material is necessary, organizations additionally want steerage on how you can plan for, develop, deploy, and use SBOMs. Consequently, we centered our analysis actions on the SBOM lifecycle (i.e., the set of actions required to plan for, develop, and use an SBOM). Nonetheless, SBOMs should additionally assist (1) proactively contemplating how you can finest handle dangers posed by third events, and (2) growing efficient mitigations as new threats and vulnerabilities emerge.
There’s broad assist for growing the utility of SBOMs. A vital subsequent step is to develop main practices and supporting processes. Creating extra complete and collaborative SBOM apply frameworks will provide strategies for successfully establishing and managing proactive software program info and danger administration applications. SBOMs can even present software program builders, integrators, and danger managers a singular alternative to gather info they will analyze, monitor, and act on to handle software program elements, suppliers, dependencies, provenance, vulnerabilities, and extra—the chances are countless.
We additionally acknowledge that the SBOM lifecycle doesn’t exist in isolation. Fairly, it’s carried out in an organizational context. Along with the core lifecycle actions, we should think about enabling and supporting different actions, resembling these carried out by program administration, organizational assist (e.g., info know-how, danger administration, and alter administration), and third events. Going ahead, it is very important look creatively at how SBOM knowledge can be utilized to handle software program danger and effectivity, and the way it can present assist to groups that may profit from collaborative efforts to unravel issues.
Constructing the SBOM Framework
We began growing the SBOM Framework by reviewing printed use circumstances. Primarily based on this overview, we developed core SBOM practices, which centered totally on growing SBOMs and utilizing them to handle identified safety vulnerabilities and related dangers. We then expanded on this preliminary set of practices by contemplating a lifecycle perspective, which recognized practices for specifying necessities, growing plans, and allocating sources wanted to construct and use SBOMs. Lastly, we recognized practices for actions that allow and assist operational use of SBOM knowledge, together with administration and assist practices, third-party practices, and infrastructure practices. The result’s an SBOM Framework comprising the next targets (with third-party practices included within the Necessities and Handle/Assist targets):
- Necessities
- Planning
- Constructing/Development
- Deployment/Use
- Administration/Assist
Our SBOM framework supplies a place to begin for integrating SBOMs with a program’s safety danger administration practices. As we acquire classes discovered from piloting the framework and suggestions from the neighborhood, we’ll replace the framework’s targets and practices as acceptable.
Leveraging SBOM Data
SBOMs have been primarily designed to assist organizations construct extra construction into the administration of software program dangers. Administration practices should not solely determine, however successfully mitigate, safety and resilience dangers in techniques. Nonetheless, knowledge and knowledge from SBOMs, whereas a key consider managing danger, has many different attainable makes use of and improvements.
Reaching efficient SBOM outcomes requires planning, tooling to scale, sources educated to do the job, measurement, and/or monitoring. Data gathered from an SBOM can provide insights into the challenges confronted by the teams engaged in managing a system. Determine 2 presents among the assist groups that would use and profit from SBOM info and key questions this info can handle to enhance software program and techniques.

Determine 2: Groups That Can Profit from SBOM Data.
Knowledge about software program dangers and vulnerabilities is wealthy and intensive. Sadly, the chance info that SBOMs include solely provides to an already overwhelming movement of knowledge. Organizing and prioritizing that info is a problem, however we anticipate the SBOM Framework to assist customers with these duties.
SBOM knowledge evaluation can even assist visualize laborious or, in some circumstances, unseen relationships and dependencies. These relationships and dependencies may be invaluable to groups who handle software program in ever extra complicated technical environments. That profit was described in The Minimal Components for a Software program Invoice of Supplies (SBOM):
An SBOM ought to include all major (high degree) elements, with all their transitive dependencies listed. At a minimal, all top-level dependencies should be listed with sufficient element to hunt out the transitive dependencies recursively.
Going additional into the graph will present extra info. As organizations start SBOM, depth past the first elements will not be simply out there as a result of present necessities with subcomponent suppliers. Eventual adoption of SBOM processes will allow entry to extra depth via deeper ranges of transparency on the subcomponent degree.
With this name for improved knowledge visualization in thoughts, we supplemented our improvement of the SEI SBOM Framework with a facet venture aimed toward graphing knowledge exported from an SBOM software. We ingest the info to create the graphical prototypes for additional analysis and evaluation (in SDPX format, which is an open customary for speaking SBOM info).
A Framework for Increasing the Utility of SBOMs
SBOMs have gotten essential in managing software program and system danger and resilience. Motivated by EO 14028, a number of efforts are underway to increase their use. Extra importantly, there’s broad and rising recognition that the dangers posed by an absence of transparency in software program should be addressed to assist guarantee safety and promote system resilience. We consider the practices and processes outlined in our SBOM Framework can present a place to begin to construction for SBOM efforts. This framework addresses the institution of processes to handle a number of SBOMs and the huge knowledge that they will present; nevertheless, these processes will probably require additional tuning as pilot-related actions present enter about enhancements and tooling.
We hope our SBOM Framework will assist promote the usage of SBOMs and set up a extra complete set of practices and processes that organizations can leverage as they construct their applications. In the meantime, we’ll proceed speaking broadly about the advantages and potential makes use of of SBOMs and collect suggestions from pilots. We can even proceed to discover pilot alternatives. The place adoption of the SBOM Framework has occurred, we’ll examine the teachings discovered to assist us in making refinements.
For a extra complete dialogue of the SEI SBOM Framework, we encourage you to learn our white paper, Software program Invoice of Supplies Framework: Leveraging SBOMs for Threat Discount. When you’re serious about piloting the framework or collaborating on future work, contact us at data@sei.cmu.edu.
[ad_2]

