[ad_1]
Monetary establishments must be vigilant within the face of a frequently evolving cybersecurity menace panorama. As these have assaults have advanced, regulatory our bodies have up to date their rules to account for the rising menace of cyber danger. In 2015, following a major enhance in nation state and hacktivist assaults on U.S. monetary establishments, the FFIEC launched new steerage and a Cybersecurity Evaluation Instrument for establishments to self assess their dangers and decide their cybersecurity maturity. This was revised in 2017, and this constant framework is meant to have the ability to assist management and the board assess their preparedness and danger over time. This framework is particularly related given the current FFIEC Structure and Operations replace and the Government Order on Cybersecurity from 2021.
The aim of this weblog is to help our IT based mostly prospects and companions with a concise and excessive stage understanding of the FFIEC Cybersecurity Evaluation Instrument and spinoff impacts on their present and future day after day operations. It’s a part of a multipart weblog sequence on monetary rules and tips on how to handle them architecturally, geared in the direction of IT management.
The Cybersecurity Evaluation Instrument is pretty intuitive to make use of and the train shouldn’t be arduous for a company to finish. The evaluation applies ideas of the FFIEC IT Handbook and the NIST Cybersecurity Framework. The intention right here was to be complimentary to current frameworks and supportive of current audit standards. The FFIEC has launched a mapping of the Cybersecurity Evaluation Instrument and the NIST Cybersecurity Framework to the FFIEC IT Handbook.
How the Evaluation works:
The evaluation itself includes two major parts: an establishment first creates an inherent danger profile based mostly upon the character of their enterprise, and figuring out cybersecurity maturity. The inherent danger profile is an establishment’s evaluation of its key applied sciences and operations. These are mapped into classes and embrace:
- Applied sciences and Connection Varieties
- Supply Channels
- On-line Cellular Merchandise and Know-how Providers
- Organizational Traits
- Exterior Threats
The software itself offers steerage on standards to promote assess danger based mostly on the completely different traits of a company, which simplifies completion in addition to consistency. By having express steerage on tips on how to self assess into completely different danger classes, the management for the establishment can guarantee they’ve a constant understanding of what the chance entails.
Beneath is a snippet of the inherent danger profile, of be aware is the intuitive and constant steerage on tips on how to classify danger inside every area.

The second side of the evaluation is knowing cybersecurity maturity. This part will help management perceive the chance and acceptable controls which have been put into place. It creates 5 ranges of maturity, from baseline to modern, and we use these to measure preparedness of the processes and controls for 5 danger domains:
- Cyber Threat Administration and Oversight
- Risk Intelligence and Collaboration
- Cybersecurity Controls
- Exterior Dependency Administration
- Cyber Incident Administration and resilience.

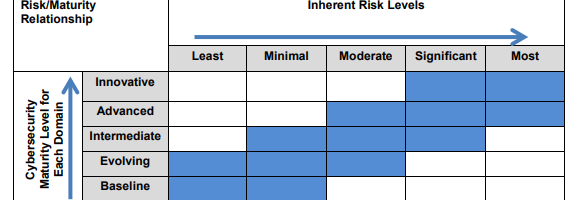
The 5 domains embrace evaluation components and declarative statements to assist administration measure their stage of controls in place. What this implies is there are statements inside every evaluation issue that describe a state. If these descriptive statements matches a monetary methods controls, then they’ll declare that stage of cybersecurity maturity. Of vital be aware nevertheless, as within the image above, the degrees are additive, like a hierarchy of wants. What this implies is that if there’s a assertion in modern that matches a few of your organizations controls, however you haven’t happy the statements within the “superior” steerage, you can’t measure your establishment as modern in that area. Likewise, an intermediate stage of maturity assumes that each one standards within the evolving stage, have been met.
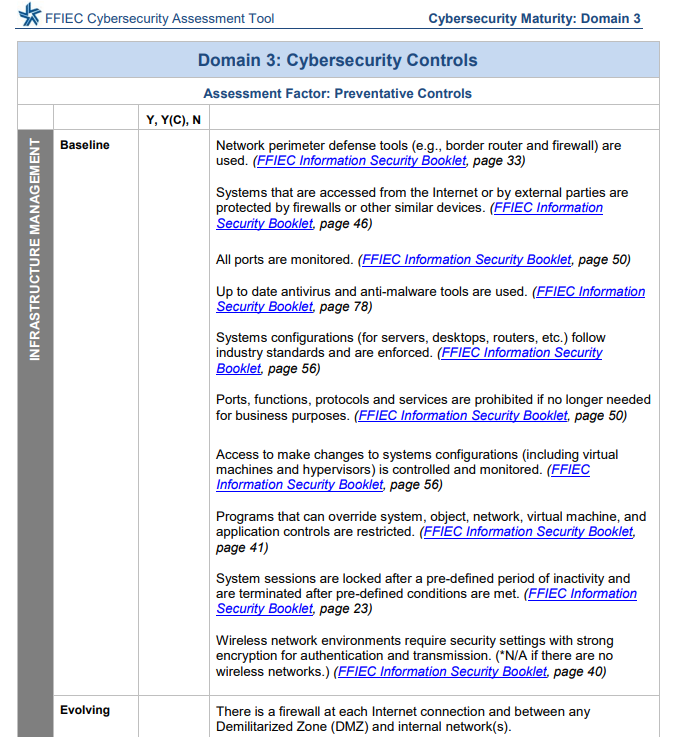
The 5 domains every have numerous evaluation components. For instance, in cybersecurity controls there are evaluation components for preventative, detective, and likewise corrective controls. Every of those evaluation components can have contributing parts that are then measured. An instance of that is throughout the preventative controls evaluation issue, there may be parts comparable to “infrastructure administration” and “entry and knowledge administration”.

It turns into simpler to check when evaluating the evaluation doc and the corresponding parts. As may be seen within the under cybersecurity steerage, there are a selection of express statements that describe maturity at a selected stage and mapping to regulatory necessities. Via satisfying these statements you possibly can appropriately match your establishment to its stage of cybersecurity maturity.
The Subsequent Step
Following completion of an inherent danger profile and cybersecurity maturity a company can decide if they’ve the suitable controls in place to deal with their inherent danger. As inherent danger will increase, clearly the next stage of safety controls must be positioned to supply a stage of management round that danger. A conceptual steerage on how danger ought to map to maturity is printed under. The place this turns into vital shouldn’t be solely in figuring out a time limit deficiency, however understanding that as new initiatives, acquisitions, or the menace atmosphere modifications, management can perceive whether or not will increase in safety controls have to be utilized to adequately deal with a fabric change in danger stage.
Spinoff Impacts on Infrastructure and Safety Groups
The Cybersecurity Evaluation is a great tool for monetary establishments to persistently present management a synopsis of the state of the establishment. However how this interprets downstream to day after day operations of architects will not be express. There are a selection of areas within the Cybersecurity Maturity part the place express steerage is given which we’ve got seen undertaken as initiatives at our prospects, in addition to throughout the trade. Beneath are just a few themes we’ve got seen acquire in prominence for the reason that publishing of the evaluation. These weren’t generated by the evaluation itself, however are widespread themes throughout the trade. Via this weblog, the intent is extra to supply a excessive stage synopsis of how these initiatives affect, and are influenced by, and measured by way of, the regulatory our bodies.
- Segmentation is explicitly referred to as out with steerage given on tips on how to measure. We’ve seen this translated throughout the trade as each Macro and Micro segmentation approaches, and each of those are complimentary. These have pushed applied sciences comparable to SD-Wan, SD-Entry, ACI, and VXLan based mostly segmentation.
- Managing infrastructure and lifecycle {hardware} and software program variations are measured. This apply isn’t particular to simply this evaluation and it has grow to be a standard theme to have the ability to maintain units in patch administration. It’s a shift from some establishments “sweating their belongings” to a proactive mannequin for managing. What had been noticed was “hackers love sweaty belongings”, with most exploits focusing on identified vulnerabilities. This could translate into any new know-how funding having a lifecycle that may guarantee the complete depreciation of the asset whereas sustaining patch administration.
- Analytics and telemetry have pushed important investments in cybersecurity operations staff’s means to grasp and act upon rising threats in actual time. Leveraging current belongings as sensors or sources of significant telemetry is vital as deploying devoted home equipment to the bigger assault surfaces of campuses, branches, and wi-fi nd may be prohibitively costly plus operationally unsupportable.
The above is just some of the various spinoff impacts that have an effect on our infrastructure and safety groups. With rising nation state steerage on safety and privateness, to incorporate the U.S. Government order on Cybersecurity, further tightening of conformance to deal with evolving safety dangers is going on. A whole lot of the elevated focus aligns to areas which happen inside current domains which can be included in current frameworks. The FFIEC Cybersecurity Maturity Evaluation is a simplified software that may assist a board member perceive which safety controls must be addressed first.
The Cybersecurity Evaluation Instrument and corresponding data are nice sources to maintain your establishment’s cybersecurity menace on course.
Share:
[ad_2]

