[ad_1]
DevSecOps practices, together with continuous-integration/continuous-delivery (CI/CD) pipelines, allow organizations to reply to safety and reliability occasions shortly and effectively and to provide resilient and safe software program on a predictable schedule and price range. Regardless of rising proof and recognition of the efficacy and worth of those practices, the preliminary implementation and ongoing enchancment of the methodology could be difficult. This weblog submit describes our new DevSecOps adoption framework that guides you and your group within the planning and implementation of a roadmap to useful CI/CD pipeline capabilities. We additionally present perception into the nuanced variations between an infrastructure crew centered on implementing a DevSecOps paradigm and a software-development crew.
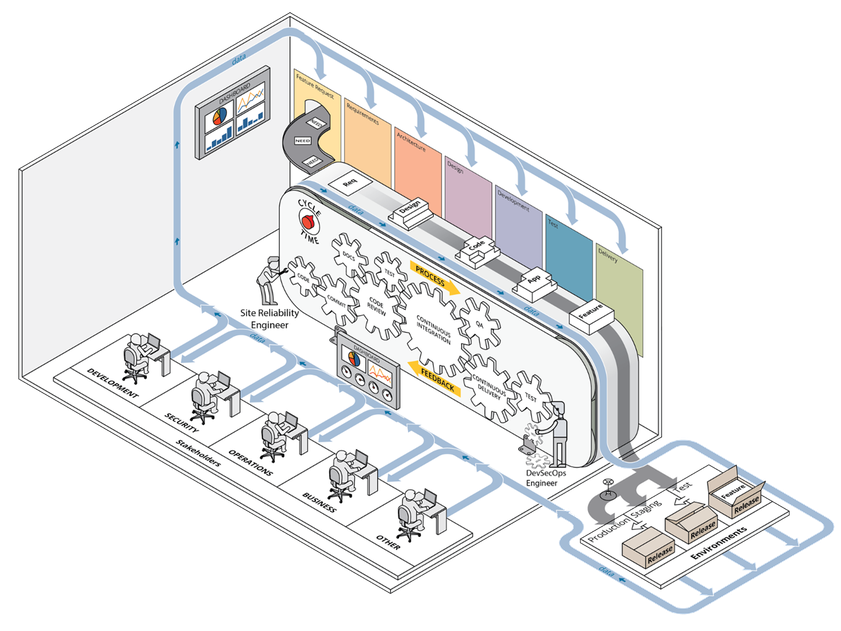
A earlier submit introduced our case for the worth of CI/CD pipeline capabilities and we launched our framework at a excessive stage, outlining the way it helps set priorities throughout preliminary deployment of a growth atmosphere able to executing CI/CD pipelines and leveraging DevSecOps practices. Determine 1 beneath depicts the DevSecOps ecosystem, with the complete integration of all parts of a CI/CD pipeline involving stakeholders from a number of departments or teams.
Determine 1: DevSecOps Ecosystem
Our framework builds on derived rules of DevSecOps, comparable to automation by the inclusion of configuration administration and infrastructure as code, collaboration, and monitoring. It supplies steering for making use of these DevSecOps rules to infrastructure operations in a computing atmosphere by offering an ordered strategy towards implementing important practices within the phases of adoption, implementation, enchancment, and upkeep of that atmosphere. Our framework additionally leverages automation all through the method and is particularly focused on the growth and operations groups, typically known as site-reliability engineers, who’re charged with managing the computing atmosphere in use by software-development groups.
The practices we define are based mostly on the precise experiences of SEI employees members supporting on-premises growth environments tailor-made to the missions of the sponsoring organizations. Our framework applies whether or not your infrastructure is working on-premises in a bodily or digital atmosphere or leveraging commercially accessible cloud companies.
The Framework in Element
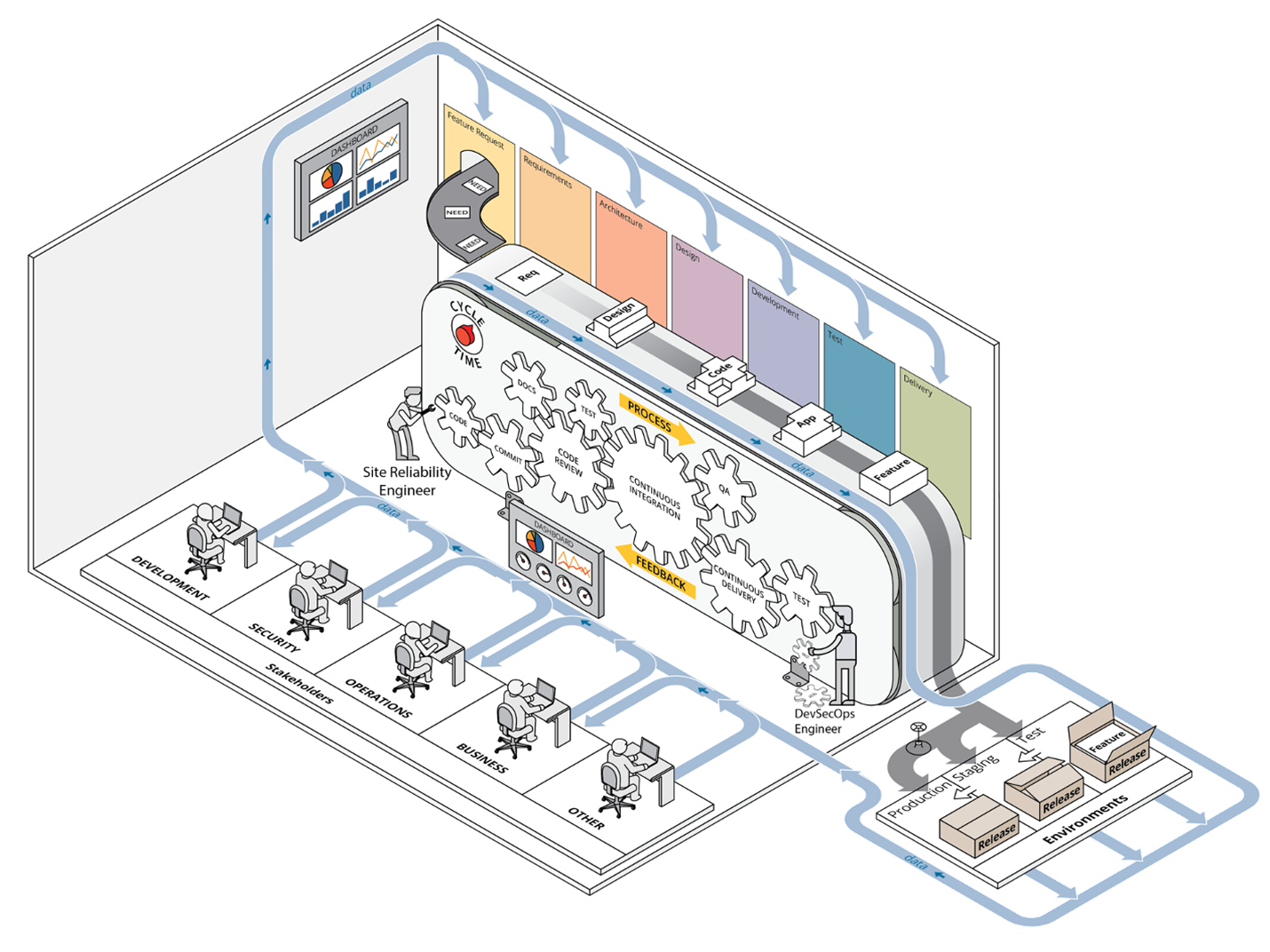
The phases of our framework, proven in Determine 2, are
0. constructing the inspiration
1. normalization
2. standardization
3. steady integration and steady testing
4. infrastructure as code (IaC) and steady supply
5. automated safety and compliance as code
6. automated compliance reporting and vulnerability remediation
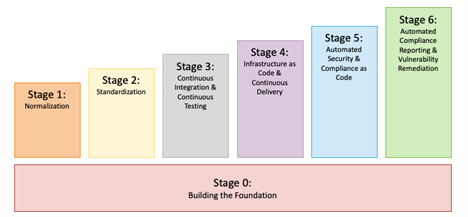
Determine 2: Our DevSecOps Adoption Framework
Breaking the work down on this means ensures that effort is spent implementing primary DevSecOps practices first, adopted by extra superior processes later. This strategy is in step with the Agile apply of manufacturing small, frequent releases in assist of finish customers, which on this case are software-development groups. Not solely are there dependencies within the early phases, but in addition a particular development within the complexity and issue of the practices in every stage. As well as, our framework permits adaptation to altering necessities and supplies ample alternatives for downside fixing as a result of many items of {hardware} and software program have to be built-in collectively to realize the objective of implementing a totally automated CI/CD pipeline.
Our framework addresses technical actions that may probably be applied by technical employees. It doesn’t particularly handle the group’s cultural adjustments that may even be required to efficiently transition to DevSecOps. Such cultural shifts inside organizations are difficult to implement and require a distinct set of expertise and organizational mettle to implement than the practices in our technical framework. Whilst you could observe some overlap within the technical and cultural practices—as a result of it’s arduous to separate the 2 fully—our framework focuses on the technical practices that allow your DevSecOps ecosystem to evolve and mature. To learn extra about spearheading a profitable cultural shift, learn this weblog submit.
The next sections describe practices we think about as key to every stage, based mostly on our experiences deploying, working, and sustaining computing infrastructure in assist of growth groups. A typical theme throughout all of the phases is the significance of monitoring. There are myriad monitoring options, each handbook and computerized. Paying shut consideration to a crew’s present scenario is invaluable to creating sound selections. Your monitoring strategies should subsequently evolve alongside along with your DevSecOps and CI/CD capabilities at every stage.
Stage 0—Constructing the Basis
We’ve numbered this Stage 0 as a result of it’s a prerequisite for all CI/CD actions, although it doesn’t straight comprise practices particularly associated to CI/CD pipelines.
Earlier than you may have any capability to construct a pipeline, you could have collaboration instruments in place, together with a wiki, an issue-tracking system, and a version-control system. You need to have your identity-management system applied accurately and be able to gathering logs of system and utility occasions and observing the well being of your collaboration instruments. These are the primary steps to enabling stable monitoring capabilities in later phases. For extra details about the method of deploying a computing atmosphere from scratch in an on-premises or co-located knowledge heart, learn our technical be aware.
Stage 1—Normalization
This stage focuses on getting organized by means of the adoption of DevSecOps practices and the minimization of redundancy (comparable to when performing database normalization). Encourage (or require) groups chargeable for the deployment and operation of your computing atmosphere to make use of the collaboration instruments you arrange in stage 0. The normalization stage is the place builders begin monitoring code adjustments in a version-control system. Likewise, operations groups retailer all scripts in a version-control system.
Furthermore, everybody—the groups managing the infrastructure and the event groups they assist—begins monitoring system points, bugs, and consumer tales in an issue-tracking system. Any deployments or software program installations that aren’t scripted and saved in model management ought to be documented in a wiki or different collaborative documentation system. The infrastructure crew must also doc repeatable processes within the wiki that can not be automated.
On this stage, try to be cognizant of the variables inside your atmosphere that could possibly be redundant. For instance, it is best to start to restrict assist of various working system (OS) platforms. Every supported OS provides a big burden in relation to configuration administration and compliance. Builders ought to develop on the identical OS on which they’ll deploy. Likewise, operations groups ought to use an OS that’s suitable with—and supplies good assist for—the methods they’ll be administering. You’ll want to monitor different affordable alternatives to eradicate overhead.
Stage 2—Standardization
This stage focuses on eradicating pointless variations in your atmosphere. Be sure that your infrastructure and pipeline parts are nicely monitored to take away the big variable of questioning whether or not your methods are wholesome. Infrastructure monitoring can embody automated alerts concerning system points (e.g., low disk-space availability) or periodically generated experiences that element the general well being of the infrastructure. Outline and doc in your wiki commonplace working procedures for frequent points to empower everybody on the crew to reply when these points come up. Use constant system configurations, ideally managed by a configuration-management system.
For instance, all of your Linux methods may use the identical configuration settings for log assortment, authentication, and monitoring, it doesn’t matter what companies these methods present. Scale back the complexity and overhead of working your computing atmosphere by adopting commonplace applied sciences throughout groups. Particularly, have all of your growth groups use a single database product on the again finish of their purposes or the identical visualization instrument for metrics gathering. Lastly, institute units of normal standards for the definition of finished to make sure that groups have accomplished all crucial work to think about their duties absolutely full. Along with monitoring the infrastructure, proceed monitoring remaining alternatives to normalize and standardize instrument utilization throughout groups.
Stage 3—Steady Integration and Steady Testing
This stage focuses on implementing steady integration, which permits the aptitude of steady testing. Steady integration is a course of that regularly merges a system’s artifacts, together with source-code updates and configuration gadgets from all stakeholders on a crew, right into a shared mainline to construct and check the developed system. This definition can simply be expanded for operations groups to imply frequent updates to configuration-management settings within the version-control system. All stakeholders ought to regularly replace documentation within the groups’ wiki areas and in tickets when acceptable, based mostly on the kind of work being documented. This strategy permits and encourages the codification and reuse of deployment patterns helpful for constructing purposes and companies.
Modifications made to a codebase within the version-control system ought to then set off construct and check procedures. Steady testing is the apply of working builds and exams every time a change is dedicated to a repository and ought to be a regular apply for software program builders and DevSecOps engineers alike. Testing ought to embody all forms of adjustments, together with code for software program tasks, shell scripts supporting system operation, or infrastructure as code (IaC) manifests. Steady testing allows you to get frequent suggestions on the standard of the code that’s dedicated.
Unit, useful, and integration exams ought to all be triggered when code is dedicated. You need to monitor the outcomes of your automated exams to acquire correct suggestions about whether or not the builds had been profitable. Likewise, these exams improve confidence that code is working accurately earlier than pushing it into manufacturing.
Our expertise reveals that it’s straightforward to overlook sure failure modes and move non-functioning code, notably while you’re not diligent about including error checking and testing for frequent failures. In different phrases, your monitoring methods have to be mature and strong sufficient to speak when issues are occurring with the adjustments made to infrastructure or code. Furthermore, groups’ definition-of-done standards ought to evolve to make sure that commonplace practices additionally evolve based mostly on particular person and crew experiences to keep away from frequent failure modes from occurring regularly.
Stage 4—Infrastructure as Code and Steady Supply
This stage accelerates your automated deployment processes by integrating infrastructure as code (IaC) and steady supply. IaC is the aptitude of capturing infrastructure deployment directions in a textual format. This strategy allows you to shortly and reliably deploy components of your atmosphere on both a bare-metal server, a digital machine, or a container platform.
Steady supply is the apply of mechanically making use of adjustments (options, configurations, bug fixes, and many others.) into manufacturing. IaC promotes atmosphere parity by eliminating creeping configuration adjustments throughout methods and environments that would produce totally different outcomes. The chief good thing about utilizing IaC and steady supply collectively is reliability. The IaC functionality can improve confidence in your atmosphere deployments. Likewise, the continuous-delivery functionality will increase confidence in your automated change supply to these environments. Launching these two capabilities creates many potentialities.
Because you began leveraging automated testing in Stage 3, Stage 4 allows you to implement the requirement that each one exams achieve success earlier than adjustments are deployed into manufacturing. In flip, this allows you to
- leverage these capabilities to handle community units with code in your version-control system
- check newly constructed software program merchandise by deploying them into newly constructed digital environments or current environments
- deploy into manufacturing when these adjustments are confirmed out
- mechanically provision hosts to broaden your present compute capabilities.
At this level, your infrastructure and the product below growth change into a tightly built-in system that allows you to absolutely perceive the general state of your system. To repeat a key apply from the earlier stage, all these potentialities are enabled by a sturdy monitoring system. Actually, advancing previous this stage into the subsequent stage is nearly inconceivable with no steady monitoring functionality that shortly and precisely supplies details about the state of the system and the system’s parts.
Stage 5—Automated Safety and Compliance as Code
This stage advances your automation capabilities past infrastructure and code deployments by including safety automations and compliance as code. Compliance as code means you’re monitoring your compliance controls in scripts and configuration administration in order that instruments can mechanically make sure that your methods are compliant with relevant rules and concern an alert when non-compliance is detected. These efforts mix the work of the safety groups and the DevSecOps groups as a result of your safety groups will possible outline necessities for the safety controls, which supplies the chance for technical folks to automate adherence to these controls. There are lots of software program items that come collectively to make this work, so you really want the earlier 4 phases in place earlier than endeavor this effort on this stage.
One instrument that’s important on this stage is a devoted vulnerability-scanning instrument. You’ll additionally need your monitoring system to alert the right set of individuals when safety points are detected mechanically. Different instruments could be leveraged to mechanically set up system and utility updates and to mechanically detect and take away pointless software program.
Stage 6—Automated Compliance Reporting and Vulnerability Remediation
This ultimate stage is the final word in supporting DevSecOps ecosystems as a result of now that you just’ve automated your system configurations, testing, and builds, you may deal with automating safety patches and steady suggestions via automated report technology or notifications throughout DevSecOps pipelines. Compliance with safety rules typically entails periodic evaluations and assessments, and having experiences available which were mechanically generated can vastly scale back the trouble required to organize for an evaluation. Precisely what experiences ought to be generated is dependent upon your particular atmosphere, however a couple of examples of helpful experiences embody
- the output of automated vulnerability scans over time
- logs aggregated out of your identity-management system
- data of patches utilized to system firmware and software program
- a abstract out of your community anomaly-detection system.
Furthermore, new vulnerabilities typically change into identified at random intervals based mostly on vendor releases and analysis bulletins. The power to mechanically generate experiences about system standing, safety points, and the impression of recent vulnerabilities in your methods and purposes signifies that your crew can shortly and effectively prioritize the work that have to be finished to make sure that your computing atmosphere is as safe appropriately. Furthermore, automating the set up of safety patches to your methods and software program helps to scale back the quantity of handbook effort spent sustaining compliant system and utility configurations and might scale back the variety of findings in your automated vulnerability scans. Likewise, having the ability to mechanically monitor the outcomes of all these automated processes ensures that the folks in your crew can step in to restore issues as they come up.
Divergence from Conventional DevSecOps Views
As talked about above, we created our DevSecOps adoption framework particularly to assist groups that deploy and keep computing environments upon which different groups will design and use CI/CD pipelines. This angle is much like—however in the end contrasts with—the everyday use of DevSecOps practices. Determine 3 beneath focuses on the functionality supply department, whereas most builders and DevSecOps practitioners are centered on the merchandise department.
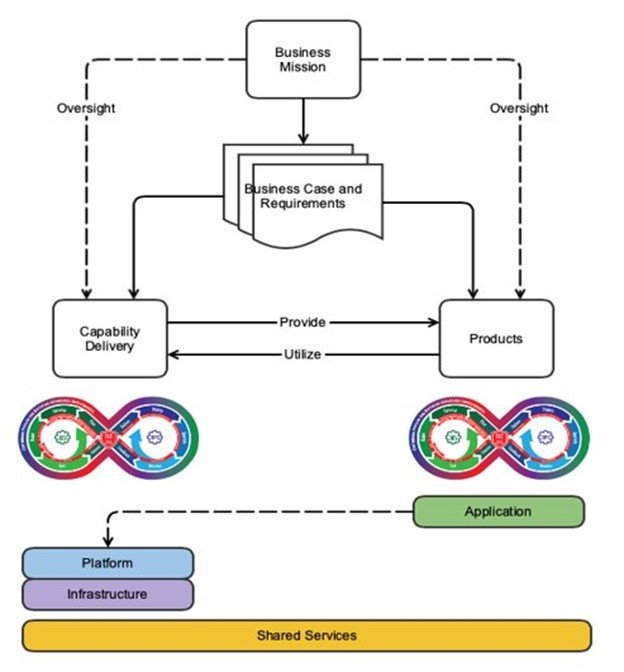
Determine 3: DevSecOps Platform-Unbiased Mannequin
The DevSecOps Platform-Unbiased Mannequin proven in Determine 3 explores this idea at an summary stage. Each the functionality supply department and the merchandise department are designed to fulfill the mission wants of the enterprise, however their designs produce two totally different plans: a system plan and a product plan. There are two distinct plans as a result of there are two distinct entities at play right here: the pipeline/system and the product that’s being developed. Although they’re associated, they’re distinct. Right here we provide one instance of the excellence between the 2, which is the huge distance between the product operators and the builders of these merchandise.
In an instance of a DevSecOps crew centered on the merchandise department, operations personnel work to assist the manufacturing atmosphere on which the software program product is deployed. This expertise permits for attention-grabbing insights, like “Launch X triggered instability at manufacturing scale as a result of it elevated CPU utilization by 50 %.” This perception can then be shortly and effectively fed again to the builders who can work to deal with the underlying concern. In different phrases, the operations personnel and the event personnel are related carefully via the DevSecOps suggestions loop. Finally, builders, safety personnel, and operational personnel are carefully knit by a typical enterprise mission and work towards a typical objective of offering the very best software program product.
Conversely, the DevSecOps groups centered on the functionality supply department are chargeable for the operation and upkeep of a growth computing atmosphere, they usually work to offer entry to a big variety of instruments to numerous stakeholders. The event personnel require entry to growth instruments and software program libraries. The safety personnel require entry to vulnerability-scanning instruments and reporting instruments. The operations personnel themselves require entry to monitoring instruments, visualization instruments, and hardware-management instruments.
Few if any of those instruments are developed in-house—as a substitute they’re both open-source or commercial-off-the-shelf instruments. This dynamic supplies an essential separation of the operations crew from the product-development crew. In distinction to the everyday state of affairs described above, when the operations crew notices {that a} new launch breaks one thing of their atmosphere, they’ll enchantment to the builders of the product for a repair that would get applied if it impacts sufficient prospects. In different phrases, the operations groups don’t collaborate with the event groups below the identical enterprise mission, however as a substitute are merely prospects of the distributors who present the merchandise in use.
What’s extra, when the unpredictability of infrastructure failures and consumer hassle tickets are added, they’ll disrupt the Agile practices of backlog grooming, dash planning, and the metric of velocity. These dynamics are totally different from a pure DevSecOps technique they usually could also be uncomfortable for folks used to working in a growth atmosphere, the place the whole crew is concentrated a hundred percent of the time on a single mission. However with a couple of variations to that conventional DevSecOps mannequin, this framework could be utilized to offer the advantages of DevSecOps practices in an operationally centered atmosphere.
Realizing the Promise of DevSecOps and CI/CD Pipelines
The objective of implementing a resilient computing atmosphere that may assist a DevSecOps ecosystem is bold, in the identical means that “develop working software program” is an bold—but important—objective. Nevertheless, the advantages of implementing DevSecOps practices—together with CI/CD pipelines—typically outweigh the prices of these difficulties.
Correct planning on the early phases could make the later phases simpler to implement. Our framework subsequently advocates for breaking the method down into small, manageable duties, and prioritizing repeatability first, automation second. Our framework orders the duties in a logical development in order that the basic constructing blocks for automation are put in place earlier than the automation itself.
The development by means of the phases is just not a one-time effort. These practices require ongoing effort to maintain your growth atmosphere and software program merchandise updated with the newest in technological developments. You need to periodically consider your present practices towards the accessible data, instruments, and sources, and modify as essential to proceed to assist your group’s mission in the best means attainable.
[ad_2]