[ad_1]

Cybercriminals and nation-state actors tailored to defenders’ ways and have become extra environment friendly in 2021, with attackers relying extra on information leaks mixed with ransomware to extort growing sums of cash from corporations — and in some circumstances utilizing information leaks with out encrypting information to power an organization to pay, in accordance with two analyses revealed this week.
Knowledge leaks related to ransomware jumped 82% in 2021, in contrast with the earlier yr, in accordance with cybersecurity agency CrowdStrike’s annual “World Risk Report,” revealed Wednesday. Virtually two-thirds (62%) of attackers averted utilizing malware for the preliminary compromise, and in 45% of incidents, the attackers used interactive intrusion — with fingers on the keyboard — to contaminate programs.
Up to now, corporations use to have the ability to blame “refined actors” for breaches, present clients with credit-monitoring providers, and basically keep away from any main penalties of a breach, however now the adversaries are taking management of the disclosure and the negotiation, says Adam Meyers, senior vice chairman for intelligence at CrowdStrike.
“Organizations want to grasp that the risk actors should not simply going after programs,” he says. “They’re going after their information and they’re utilizing it in opposition to them in methods which can be much more harmful than simply encrypting it.”
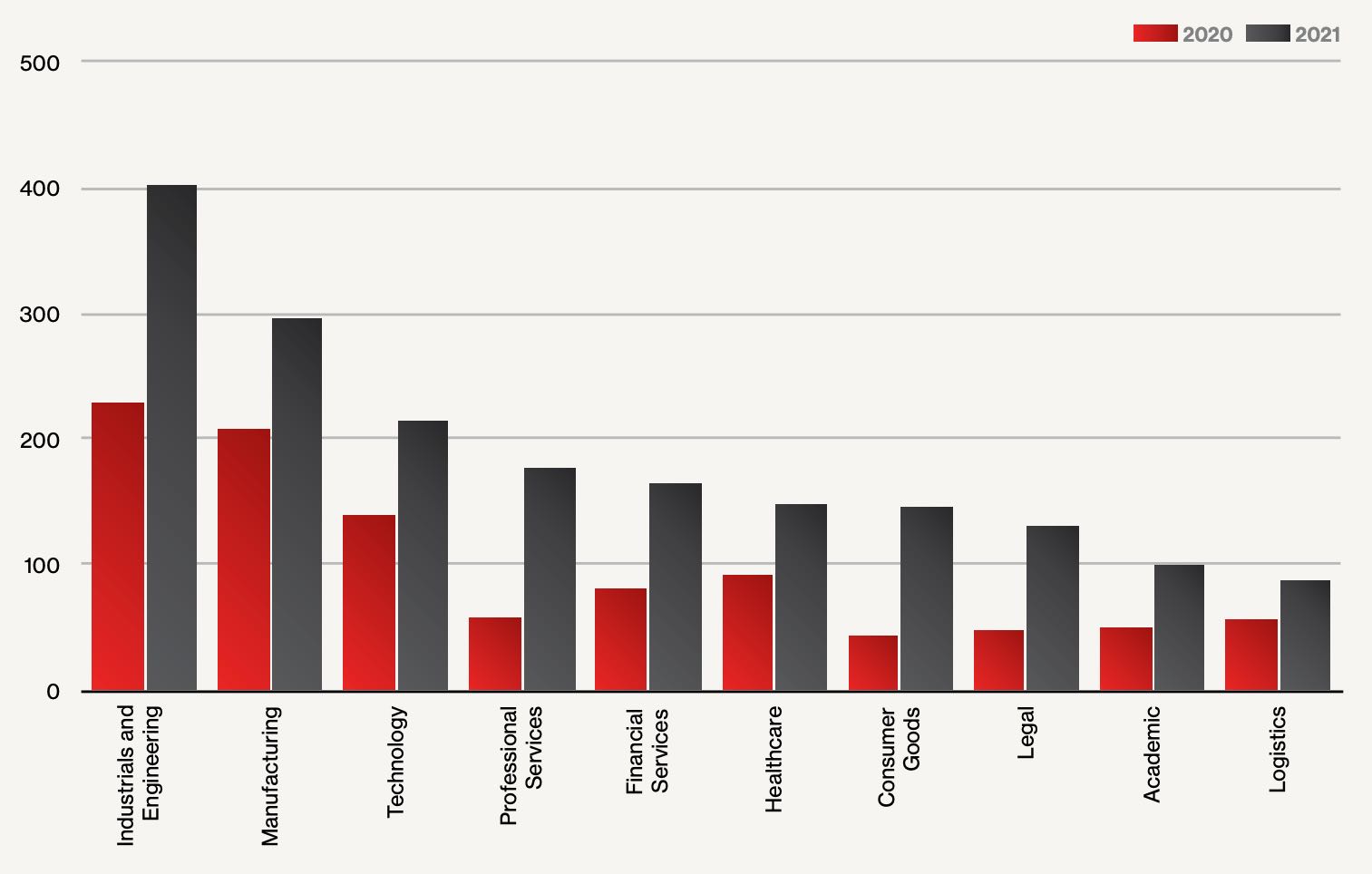
The adoption of knowledge extortion highlights how assaults change to adapt to defenders ways, with information leaks hitting each business in larger numbers in 2021 than the earlier yr. The commercial and engineering sector suffered probably the most assaults, with ransomware-linked information leaks rising above 400 incidents, in contrast with about 230 in 2020. The second most focused business, manufacturing, had virtually 300 information leaks, whereas know-how companies suffered greater than 200, in accordance with the CrowdStrike report.
In 2021, the corporate investigated extra focused assaults, which elevated to 18% of the overall incidents investigated, up from 13% in 2020. The share of hacktivism-related threats remained the identical at 1%, whereas e-crime and unattributed threats, which make up nearly all of incidents — a half and a 3rd, respectively — fell barely.
A key theme for 2021 is that attackers proceed to maneuver operations to new approaches or malware wherever attainable, the report states.
“New ways, strategies and procedures (TTPs) utilized in information theft assaults in 2021 aided adversaries in extorting their victims — for instance, [one group] averted utilizing publicly accessible exfiltration instruments by creating their very own,” CrowdStrike states within the report. “One other main growth was elevated information theft and extortion with out using ransomware, resulting in the institution of recent marketplaces devoted to promoting and promoting sufferer information.”
Knowledge Weaponization
Whereas many organizations have refused to pay ransoms to cybercriminals, the attackers have tried to take management of negotiations again from victims by including information leaks — and in some circumstances, denial-of-service assaults — to their repertoire. Organizations that don’t adjust to calls for will discover delicate information leaked to the general public, Meyer says.
“Knowledge is more and more being weaponized, and increasingly actors are doing information weaponization as a result of it offers the attacker a management lever with the sufferer,” he says. “It turns into a manner for the risk actor to take management of the state of affairs in a manner that they might not after they solely encrypted the information.”
Attackers’ shift of their assaults is a theme of one other report revealed this week by safety advisory agency Kroll. Exploitation of vulnerabilities jumped to the second most-used technique of preliminary entry, up from fifth place, with 27% of assaults within the fourth quarter utilizing exploits, in accordance with Kroll’s “This autumn 2021 Risk Panorama” report. The highest technique of preliminary entry continues to be phishing assaults that steal credentials, the corporate states.
Ransomware and e-mail compromises, together with phishing, proceed to be the most typical kinds of risk incidents, collectively accounting for two-thirds of all incidents, in accordance with Kroll. Firms have to develop into extra agile in how they check and apply patches for essential programs, in accordance with Keith Wojcieszek, managing director in Kroll’s cyber danger observe.
“Whereas legislation enforcement made important headway in disrupting attackers, the truth that we noticed new ransomware variations and extortion websites, mixed with splinter ransomware teams, demonstrates the agile operations and malicious intent of those prison teams,” he stated in an announcement. “Add this to the upper variety of software program vulnerabilities being exploited by ransomware operators and the velocity at which they’re compromised, and it underlines the significance of legislative motion in opposition to attackers to take them out of operation utterly.”
Attackers proceed to present defenders little or no time to react to a breach. A technique CrowdStrike measures the velocity and agility of attackers is the so-called “breakout time,” which is the period of time it takes for an attacker to maneuver from the preliminary compromise to contaminate different computer systems on the community. Between 2022 and 2021, the breakout time remained almost the identical, with attackers averaging 1 hour and 38 minutes in 2021 and 1 hour and 32 minutes the earlier yr.
[ad_2]