[ad_1]

We noticed the Maze ransomware builders reemerge briefly this week as they shared the grasp decryption keys for the Egregor, Maze, and Sekhmet ransomware operations.
After the Maze ransomware operation started shutting down in October 2020, it was all the time hoped that they might publicly launch decryption keys to permit remaining victims to recuperate their information.
Tuesday night time, virtually fourteen months later, the alleged ransomware developer launched the decryption keys in a BleepingComputer discussion board put up.
Whereas the developer says they’d all the time deliberate to publish the keys, it’s typically believed that they did it now as a gesture of goodwill as a result of latest arrests and server seizures.
Utilizing these keys, cybersecurity agency Emsisoft created a decryptor permitting victims to recuperate their information totally free.
The opposite massive information is the sentencing of a Netwalker ransomware affiliate from Canada, who obtained greater than $27.6 million by attacking firms worldwide. After pleading responsible, the affiliate was sentenced to 6 years and eight months in jail.
This week’s different attention-grabbing ransomware information consists of publishing LockBit 2.0 ransomware technical particulars by the FBI, a free decryptor for the TargetCompany ransomware, and Puma asserting a knowledge breach as a result of Kronos ransomware assault.
Contributors and those that offered new ransomware data and tales this week embody: @Seifreed, @billtoulas, @malwareforme, @VK_Intel, @BleepinComputer, @FourOctets, @DanielGallagher, @serghei, @malwrhunterteam, @jorntvdw, @fwosar, @Ionut_Ilascu, @PolarToffee, @LawrenceAbrams, @demonslay335, @struppigel, @chainalysis, @emsisoft, @Avast, @LadislavZezula, @coveware, @ddd1ms, @BrettCallow, @pcrisk, @USCERT_gov, and @CISAgov.
February fifth 2022
BlackCat (ALPHV) ransomware linked to BlackMatter, DarkSide gangs
The Black Cat ransomware gang, often known as ALPHV, has confirmed they’re former members of the infamous BlackMatter/DarkSide ransomware operation.
FBI shares Lockbit ransomware technical particulars, protection suggestions
The Federal Bureau of Investigation (FBI) has launched technical particulars and indicators of compromise related to LockBit ransomware assaults in a brand new flash alert printed this Friday.
February sixth 2022
Regulation enforcement motion push ransomware gangs to surgical assaults
The quite a few legislation enforcement operations resulting in the arrests and takedown of ransomware operations in 2021 have pressured menace actors to slender their concentrating on scope and maximize the effectivity of their operations.
February seventh 2022
Free decryptor launched for TargetCompany ransomware victims
Czech cybersecurity software program agency Avast has launched a decryption utility to assist TargetCompany ransomware victims recuperate their information totally free.
Puma hit by knowledge breach after Kronos ransomware assault
Sportswear producer Puma was hit by a knowledge breach following the ransomware assault that hit Kronos, certainly one of its North American workforce administration service suppliers, in December 2021.
New STOP Ransomware variants
PCrisk discovered new STOP ransomware variants that append the .cuag and .avyu extensions.
February eighth 2022
NetWalker ransomware affiliate sentenced to 80 months in jail
Sebastien Vachon-Desjardins, a Canadian man charged by the US for his involvement in NetWalker ransomware assaults, was sentenced to six years and eight months in jail after pleading responsible earlier than an Ontario decide to a number of offenses linked to assaults on 17 Canadian victims.
February ninth 2022
Ransomware dev releases Egregor, Maze grasp decryption keys
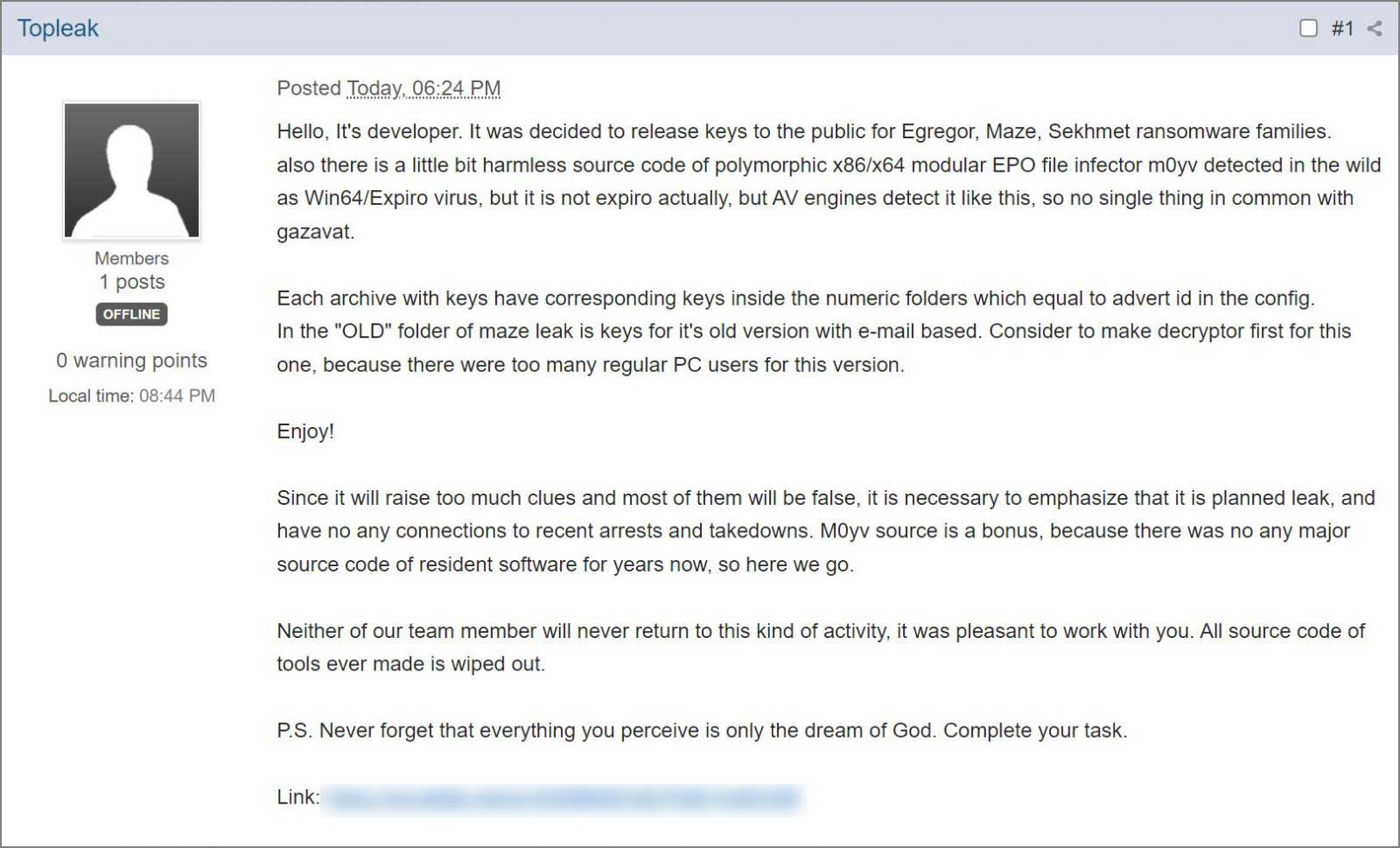
The grasp decryption keys for the Maze, Egregor, and Sekhmet ransomware operations had been launched final night time on the BleepingComputer boards by the alleged malware developer.
Emsisoft releases a decryptor for Maze / Sekhmet / Egregor
Emsisoft created a decryptor permitting Maze, Sekhmet, and Egregor victims to recuperate their information totally free.
New Phobos Ransomware variants
PCrisk discovered a brand new Phobos ransomware variant that appends the .ZOZL extension.
In 2021, cybersecurity authorities in the US,[1][2][3] Australia,[4] and the UK[5] noticed a rise in refined, high-impact ransomware incidents in opposition to important infrastructure organizations globally. The Federal Bureau of Investigation (FBI), the Cybersecurity and Infrastructure Safety Company (CISA), and the Nationwide Safety Company (NSA) noticed incidents involving ransomware in opposition to 14 of the 16 U.S. important infrastructure sectors, together with the Protection Industrial Base, Emergency Providers, Meals and Agriculture, Authorities Amenities, and Data Know-how Sectors. The Australian Cyber Safety Centre (ACSC) noticed continued ransomware concentrating on of Australian important infrastructure entities, together with within the Healthcare and Medical, Monetary Providers and Markets, Increased Training and Analysis, and Power Sectors. The UK’s Nationwide Cyber Safety Centre (NCSC-UK) acknowledges ransomware as the largest cyber menace dealing with the UK. Training is likely one of the prime UK sectors focused by ransomware actors, however the NCSC-UK has additionally seen assaults concentrating on companies, charities, the authorized occupation, and public providers within the Native Authorities and Well being Sectors.
February tenth 2022
As Ransomware Funds Proceed to Develop, So Too Does Ransomware’s Function in Geopolitical Battle
Certain sufficient, we up to date our ransomware numbers a number of occasions all through 2021, reflecting new funds we hadn’t recognized beforehand. As of January 2022, we’ve now recognized simply over $692 million in 2020 ransomware funds — practically double the quantity we initially recognized on the time of writing final 12 months’s report.
Chainalysis In Motion: How FBI Investigators Traced DarkSide’s Funds Following the Colonial Pipeline Ransomware Assault
One month later, there was excellent news: The Division of Justice introduced that it had managed to grab $2.3 million value of Bitcoin from Colonial’s ransom cost following an FBI investigation. Chainalysis is proud to say that our instruments aided the FBI, and that we are able to now share particulars of how investigators tracked the funds following the assault.
February eleventh 2022
.NET ransomware impersonates REvil
Karsten Hahn discovered a .NET ransomware that impersonates REvil by copying the ransom be aware and Tor website.
New STOP Ransomware variants
PCrisk discovered new STOP ransomware variants that append the .iips and .ccps extensions.
That is it for this week! Hope everybody has a pleasant weekend!
[ad_2]
