[ad_1]
Lazarus, the North Korea-affiliated state-sponsored group, is trying to as soon as once more goal safety researchers with backdoors and distant entry trojans utilizing a trojanized pirated model of the favored IDA Professional reverse engineering software program.
The findings have been reported by ESET safety researcher Anton Cherepanov final week in a collection of tweets.
IDA Professional is an Interactive Disassembler that is designed to translate machine language (aka executables) into meeting language, enabling safety researchers to research the inside workings of a program (malicious or in any other case) in addition to operate as a debugger to detect errors.
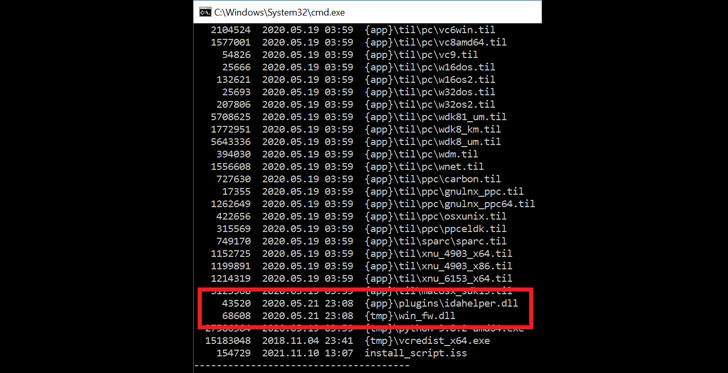
“Attackers bundled the unique IDA Professional 7.5 software program developed by [Hex-Rays] with two malicious parts,” the Slovak cybersecurity agency stated, considered one of which is an inside module referred to as “win_fw.dll” that is executed throughout set up of the functions. This tampered model is then orchestrated to load a second element named “idahelper.dll” from the IDA plugins folder on the system.
Upon profitable execution, the “idahelper.dll” binary connects to a distant server at “www[.]devguardmap[.]org” to retrieve subsequent payloads. The area can be notable for the truth that it has been beforehand linked to an identical North Korea-backed marketing campaign aimed toward safety professionals and disclosed by Google’s Menace Evaluation Group earlier this March.
The covert operation concerned the adversaries establishing a faux safety firm often called SecuriElite alongside plenty of social media accounts throughout Twitter and LinkedIn in an try to trick unsuspecting researchers into visiting the corporate’s malware-laced web site in order to set off an exploit that leveraged a then zero-day in Web Explorer browser. Microsoft ultimately addressed the problem in its Patch Tuesday replace for March 2021.
Additionally identified by the monikers APT38, Hidden Cobra, and Zinc, the Lazarus Group is understood to be energetic as early as 2009 and linked to a string of assaults for monetary achieve and harvesting delicate data from compromised environments.
“North Korea’s cyber program poses a rising espionage, theft, and assault menace,” in accordance to the U.S. Workplace of the Director of Nationwide Intelligence 2021 Annual Menace Evaluation printed earlier this April.
“North Korea has carried out cyber theft towards monetary establishments and cryptocurrency exchanges worldwide, doubtlessly stealing a whole bunch of thousands and thousands of {dollars}, most likely to fund authorities priorities, similar to its nuclear and missile applications.”
[ad_2]