[ad_1]

Menace actors behind the Qlocker ransomware are as soon as once more focusing on Web-exposed QNAP Community Hooked up Storage (NAS) units worldwide.
Qlocker has beforehand focused QNAP clients in a huge ransomware marketing campaign that began in the course of the week of April 19, shifting victims’ recordsdata inside password-protected 7-zip archives with the .7z extension after breaching their NAS units.
QNAP warned that the attackers have been exploiting the CVE-2021-28799 hard-coded credentials vulnerability within the HBS 3 Hybrid Backup Sync app to hack into customers’ units and lock their recordsdata.
Nevertheless, for some QNAP clients focused in final yr’s Qlocker ransomware marketing campaign, the warning got here approach too late after the attackers extorted a whole lot of QNAP customers.
In complete, affected QNAP customers misplaced roughly $350,000 inside a single month after paying ransoms of 0.01 bitcoins (price roughly $500 on the time) to get the password wanted to recuperate their information.
Qlocker returns in new 2022 marketing campaign
The brand new Qlocker ransomware marketing campaign started on January 6 and it drops ransom notes named !!!READ_ME.txt on compromised units.
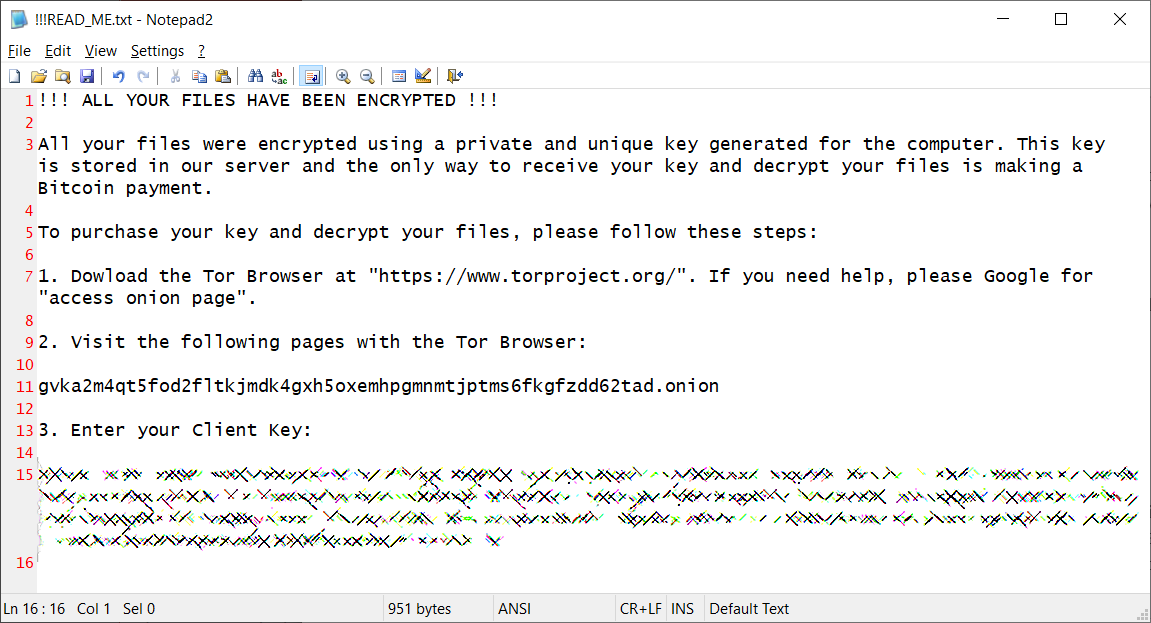
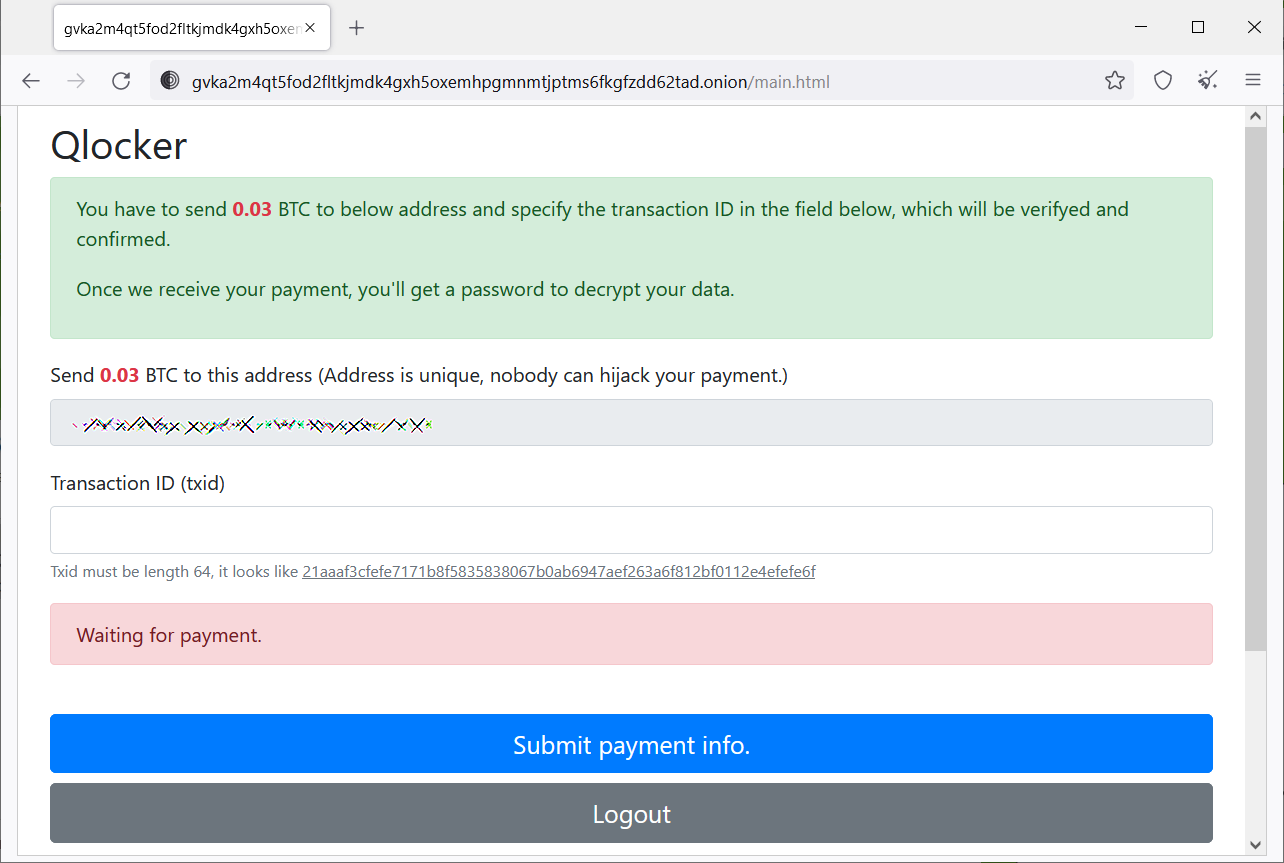
These ransom notes additionally embrace the Tor website deal with (gvka2m4qt5fod2fltkjmdk4gxh5oxemhpgmnmtjptms6fkgfzdd62tad.onion) the victims are prompted to go to to realize extra info on how a lot they must pay to regain entry to their recordsdata.
Tor sufferer pages seen by BleepingComputer since this new collection of Qlocker assaults began show ransom calls for ranging between 0.02 and 0.03 bitcoins.
Extra info on what to do if the QLocker2 ransomware marketing campaign has hit you might be present in this help subject (the subject for the 2021 Qlocker marketing campaign might be discovered right here).
You too can take a look at the outdated information on easy methods to recuperate information from NAS units compromised in final yr’s Qlocker ransomware assaults.
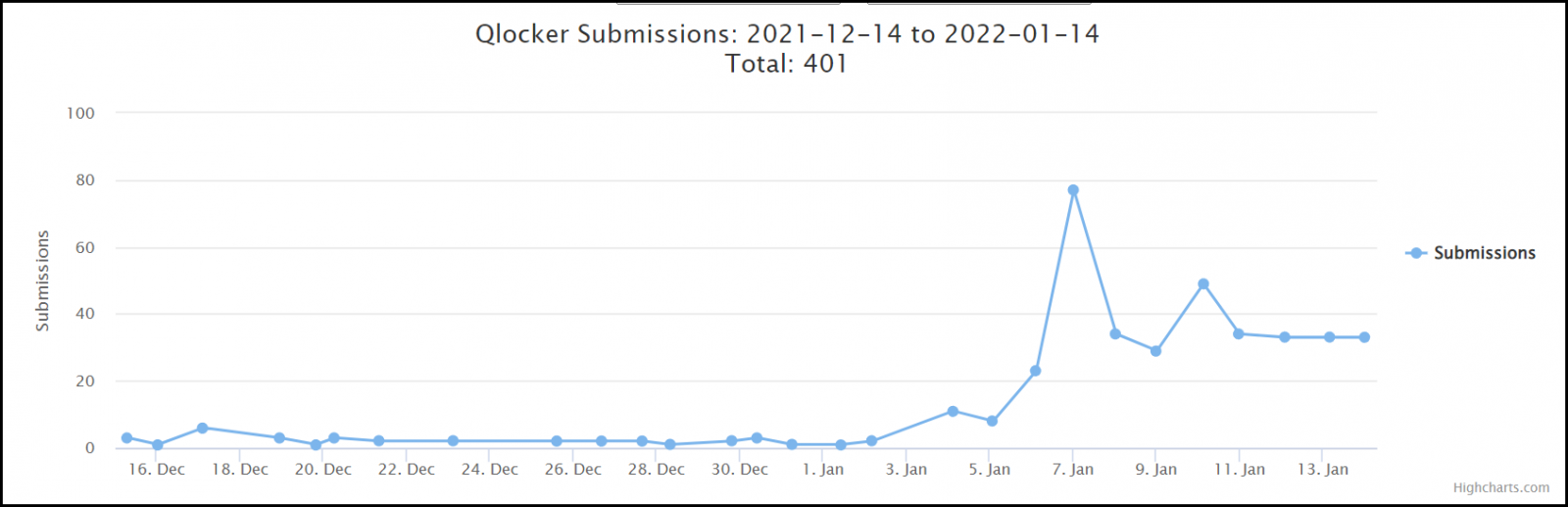
Since Qlocker returned on January 6, dozens of ransom notes and encrypted recordsdata have been submitted to the ID-Ransomware service by affected QNAP customers.
Sadly, Qlocker isn’t the one ransomware focusing on QNAP NAS units, as proven by a surge of ech0raix ransomware assaults that began proper earlier than Christmas.
Earlier this month, the corporate additionally warned its clients to safe Web-exposed NAS units from ongoing ransomware and brute-force assaults by disabling Port Forwarding on their routers and their units’ UPnP operate.
QNAP additionally notified clients final yr to safe their units in opposition to incoming assaults, together with Agelocker and eCh0raix ransomware campaigns.
The NAS maker recommends implementing the next greatest practices if you wish to safe your QNAP gadget from additional assaults.
[ad_2]
