[ad_1]

The Twitter account beforehand related to the ANOM chat app is posting frivolous tweets this week. However, is it an account hijack, as some could surprise? Maybe not.
ANOM was a faux encrypted messaging platform created as a part of a world sting operation led by the U.S. FBI, Australian Federal Police (AFP), and different regulation enforcement businesses to catch criminals.
Troll away, ANOM!
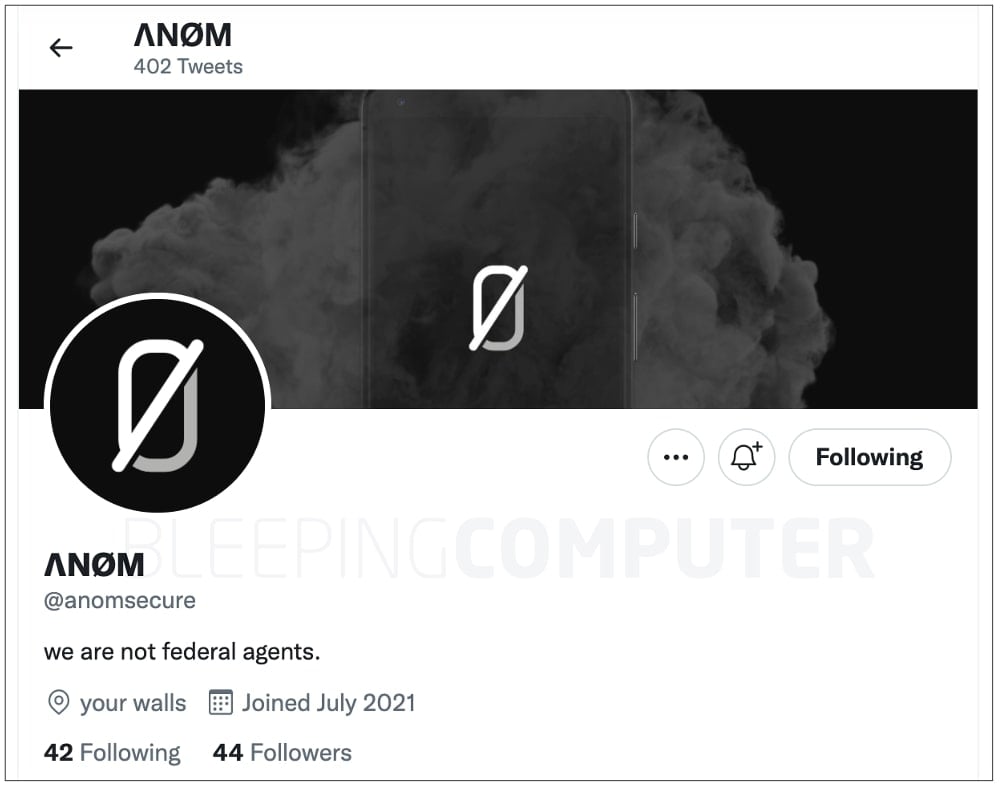
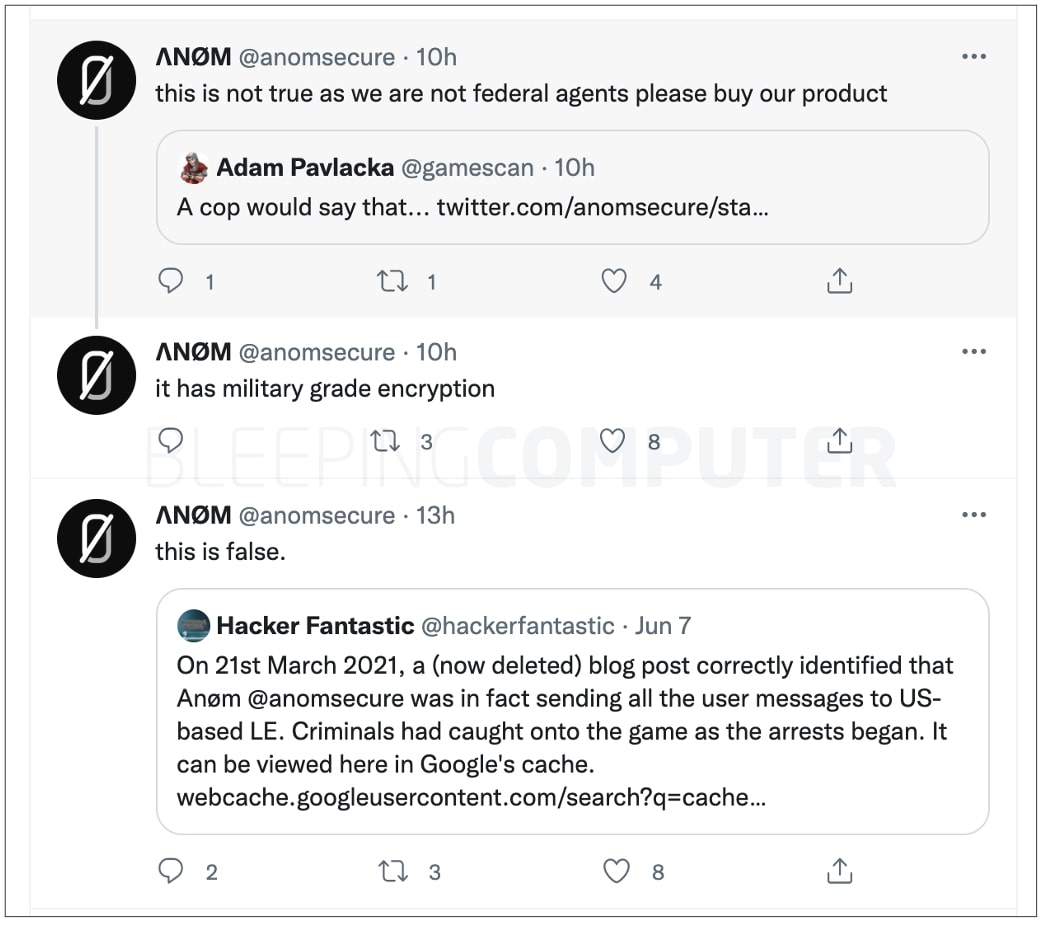
As seen by BleepingComputer immediately, ANOM’s Twitter account @anomsecure carries a revised bio that states “we’re not federal brokers,” in an try to mock ANOM’s goal.
“Somebody has taken over the social media accounts of ΛNØM, an encrypted telephone messaging service that was reportedly used as a regulation enforcement sting, to tweet claims that they don’t seem to be FBI…,” wrote Matthew Hickey aka Hacker Improbable, co-founder of cybersecurity consultancy Hacker Home, referring to the continued tweets printed from the account:
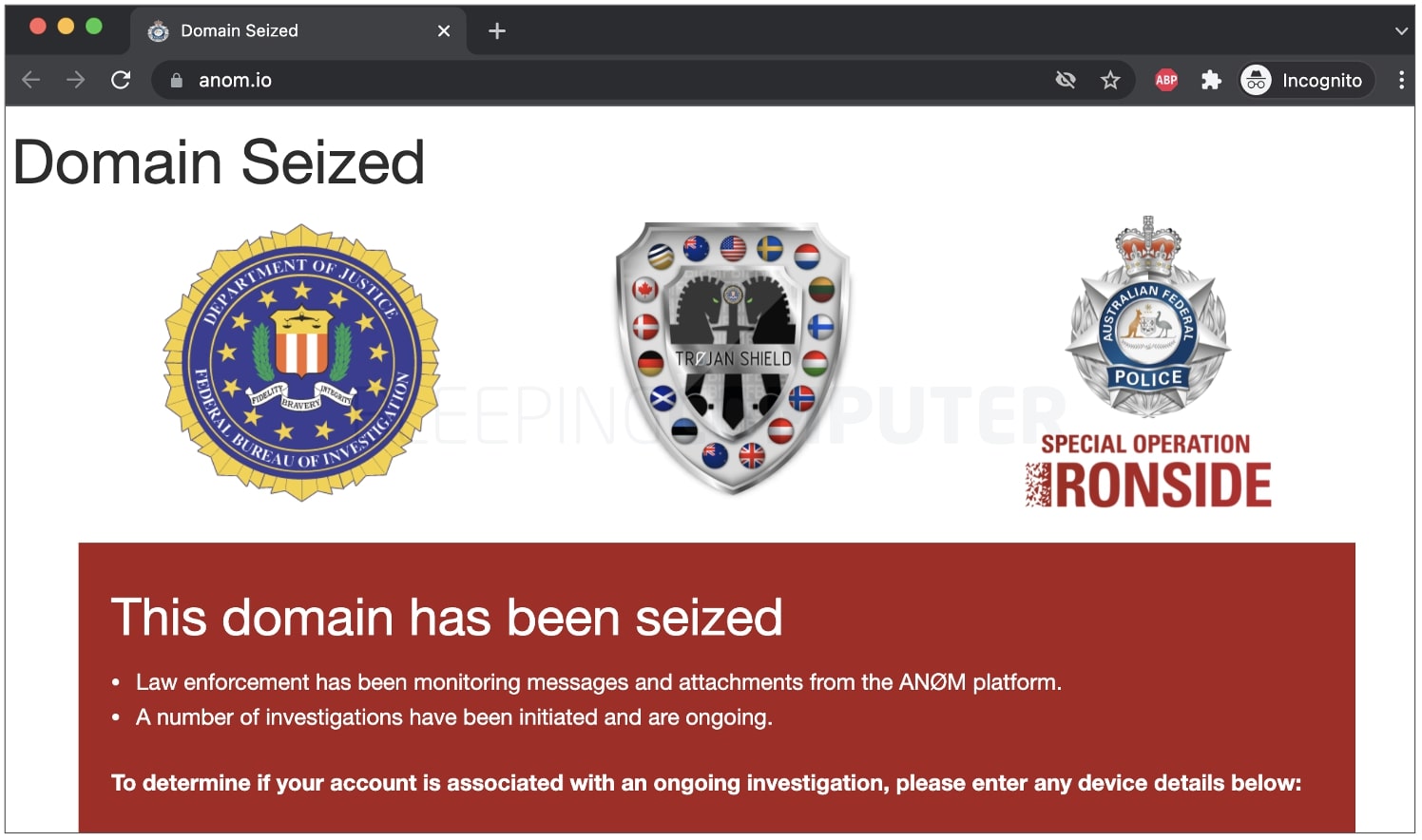
In June, BleepingComputer unveiled ANOM’s inception was a part of a large regulation enforcement initiative dubbed Operation Ironside, or Operation Trojan Defend that ran between 2018 and 2021.
Throughout this time, the FBI, AFP, Europol, and numerous regulation enforcement businesses collaborated to create a faux encrypted messaging platform referred to as Anom that was bought solely to criminals.
The platform allowed the authorities to intercept the messages and conversations between criminals.
After reviewing 27 million messages the place criminals mentioned their actions on the Anom platform, regulation enforcement was capable of arrest 800 individuals and seize 8 tons of cocaine, 22 tons of hashish and hashish resin, 2 tons of artificial medication (amphetamine and methamphetamine), 6 tons of artificial medication precursors, 250 firearms, 55 luxurious automobiles and over $48 million in numerous worldwide currencies and cryptocurrencies.
On the time, Europol acknowledged that many international locations participated within the worldwide coalition: Australia, Austria, Canada, Denmark, Estonia, Finland, Germany, Hungary, Lithuania, New Zealand, the Netherlands, Norway, Sweden, the UK incl. Scotland, and the USA.
This made Operation Ironside the “largest and most refined regulation enforcement operations thus far.”
Twitter account had disappeared in June
Previous to ANOM’s social media account posting mock tweets of immediately, in June, the account’s bio linked to the anom.io area and had a extra plausible description:
“Encrypted Messaging Platform, Maintain Secrets and techniques Protected || App that enforces your Privateness #Anom…”
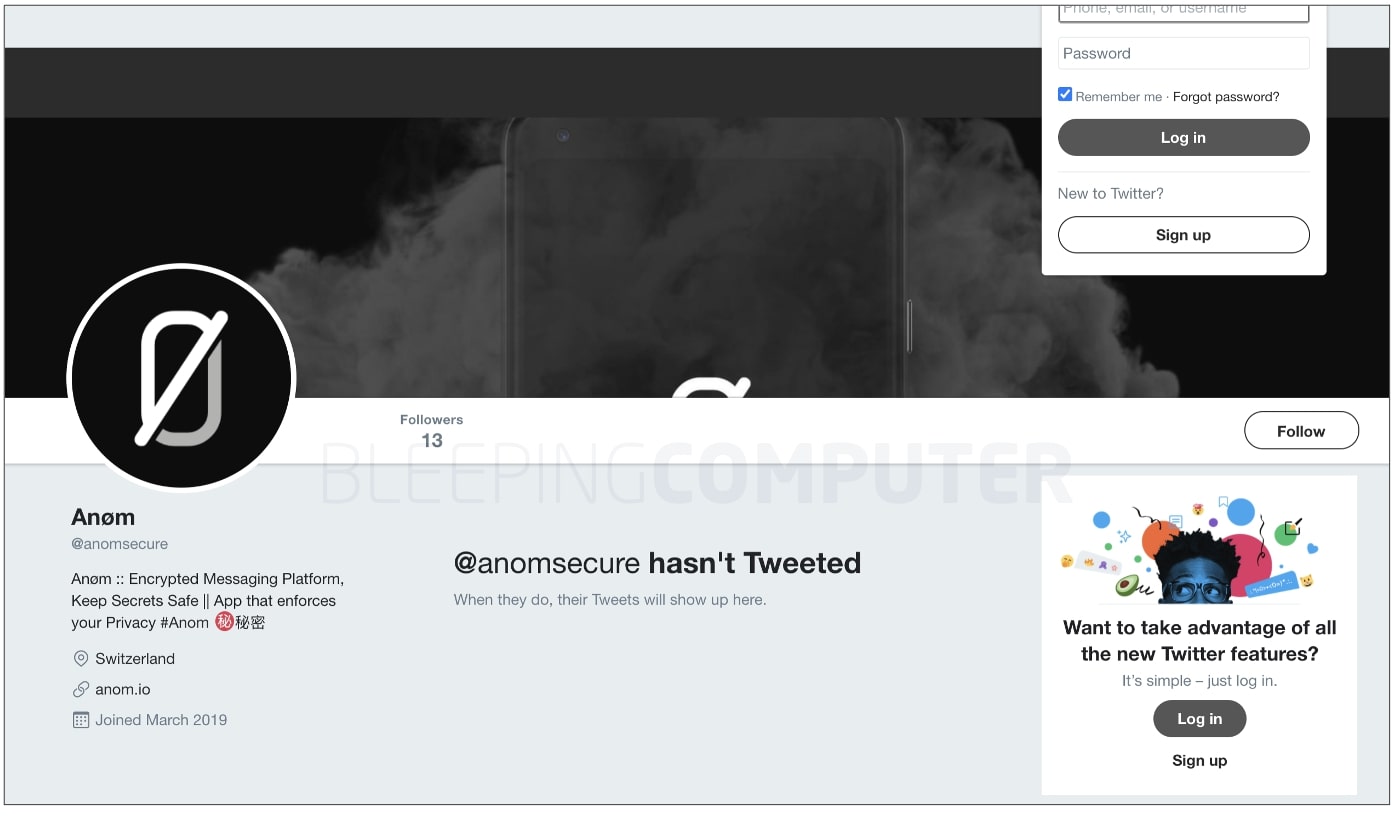
Later in June, the @anomsecure Twitter account had fully disappeared, resulting in a “nothing to see right here… appears like this web page does not exist” message, as confirmed by BleepingComputer.
This might have occurred, for instance, if the Twitter username was modified, and the @anomsecure deal with grew to become obtainable for anybody to assert.
Twitter clearly states that “as soon as you modify your username, your earlier username will instantly be obtainable to be used by another person.”
Across the similar time, as Operation Ironside was being made public information, the anom.io area was set to show a “area seized” discover by the regulation enforcement businesses, which remains to be up immediately.
Since then, the oldest tweet nonetheless obtainable immediately from @anomsecure, as seen by BleepingComputer, dates again to July twenty third. And, the account’s “joined” date states “July 2021,” versus “March 2019” listed within the June screenshot above.
It’s due to this fact trying more and more probably that slightly than an account hijack, that is merely a case of @anomsecure deal with turning into obtainable sooner or later in time, and claimed July 4th, 2021 by a troll who’s behind the brand new bio and mock tweets.
BleepingComputer has reached out to a number of regulation enforcement businesses related to ANOM for remark and we’re awaiting their response.
[ad_2]
