[ad_1]

One of many largest Vietnamese crypto buying and selling platforms, ONUS, just lately suffered a cyber assault on its cost system working a weak Log4j model.
Quickly sufficient, menace actors approached ONUS to extort a $5 million sum and threatened to publish the shopper information ought to ONUS refuse to conform.
After the corporate’s refusal to pay the ransom, menace actors put up information of almost 2 million ONUS clients on the market on boards.
Cost software program ran a weak log4j model
On December ninth, the PoC exploit for the infamous Log4Shell vulnerability (CVE-2021-44228) leaked on GitHub. And, that obtained the eye of opportunistic attackers who started mass-scanning the web for weak servers.
Between December eleventh and thirteenth, menace actors efficiently exploited the Log4Shell vulnerability on a Cyclos server of ONUS and planted backdoors for sustained entry.
Cyclos offers a variety of point-of-sale (POS) and cost software program options, and like most distributors, was utilizing a weak log4j model of their software program.
Though Cyclos did situation an advisory on the thirteenth and reportedly knowledgeable ONUS to patch their methods, it was too late.
Regardless of ONUS having patched their Cyclos occasion, the publicity window allowed adequate time for menace actors to exfiltrate delicate databases.
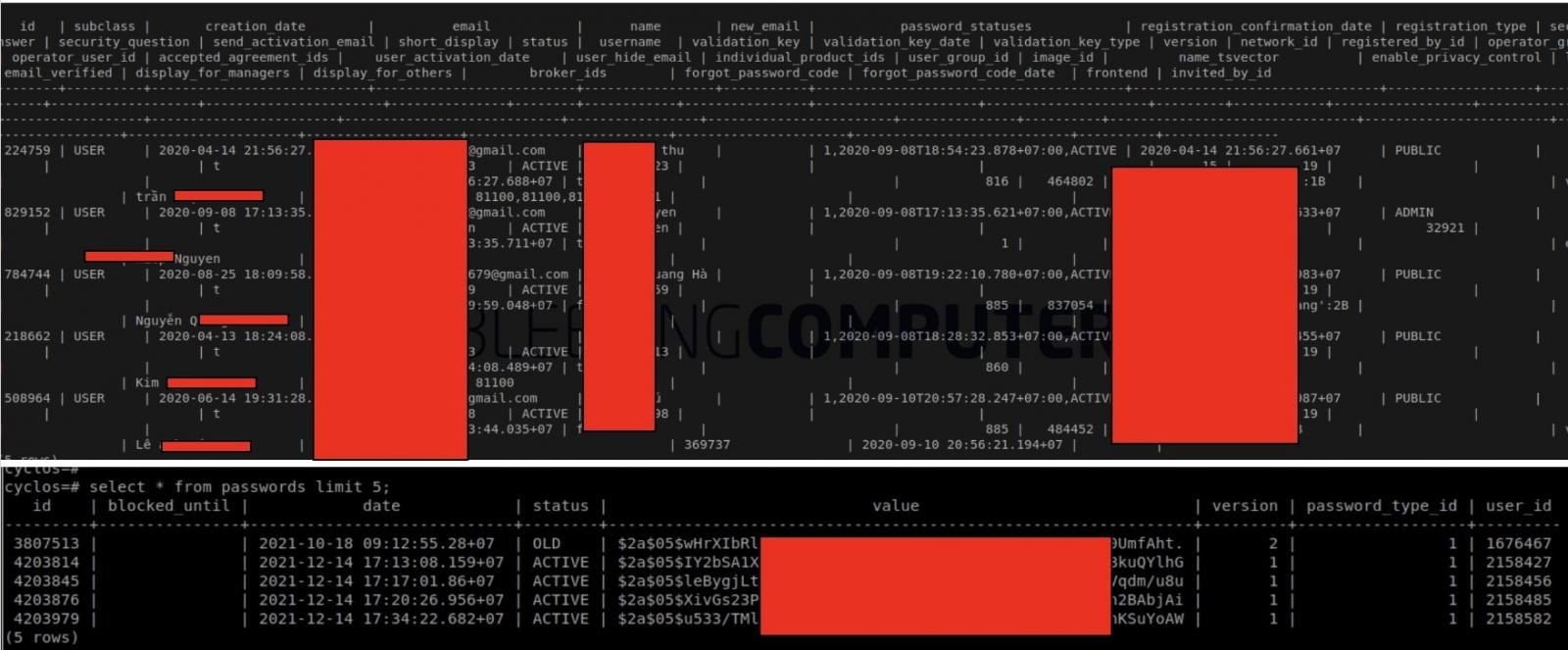
These databases contained almost 2 million buyer information together with E-KYC (Know Your Buyer) information, private info, and hashed passwords.
E-KYC workflows utilized by banks and FinTech corporations usually contain procuring some type of identification paperwork and proofs from the clients, together with a ‘video selfie’ for automated verification.
Curiously, the Log4Shell vulnerability existed on a sandbox server used “for programming functions solely” however allowed attackers additional entry into delicate information storage places (Amazon S3 buckets) with manufacturing information, because of a system misconfiguration.
ONUS was then reportedly slapped with a $5 million extortion demand that they declined to fulfill. As a substitute, the corporate selected to reveal the assault to their clients through a personal Fb group.
“As an organization that places security first, we’re dedicated to offering our clients with transparency and integrity in enterprise operations,” acknowledged ONUS CEO Chien Tran.
“That’s the reason, after cautious consideration, the suitable factor we have to do now’s to tell the complete ONUS group about this incident.”
A replica of the disclosure has been obtained by BleepingComputer, together with a tough English translation appended:
Misconfigured Amazon S3 buckets
The hack itself is a bit more than only a Log4j downside alone. Log4j exploit might have been the entry level for attackers, however improper entry management on ONUS’ Amazon S3 buckets allowed attackers undue entry.
“The hacker took benefit of a vulnerability in a set of libraries on the ONUS system to get into the sandbox server (for programming functions solely),” explains ONUS.
“Nonetheless, because of a configuration downside, this server incorporates info that gave unhealthy guys entry to our information storage system (Amazon S3) and stole some important information. This results in the danger of leaking the non-public info of numerous customers.”
The shopper info retrieved by menace actors contains:
- Title
- E-mail and Cellphone quantity
- Handle
- KYC info
- Encrypted password
- Transaction historical past
- And another encrypted info
Cybersecurity agency CyStack, which supplied companies to ONUS, has performed a radical investigation and launched their findings on the assault mechanics and the backdoor planted by the attackers.
Practically 2 million buyer information put up on the market
By December twenty fifth, after failing to safe the extortion quantity from ONUS, menace actors put up the shopper information on the market on a knowledge breach market, as seen by BleepingComputer:
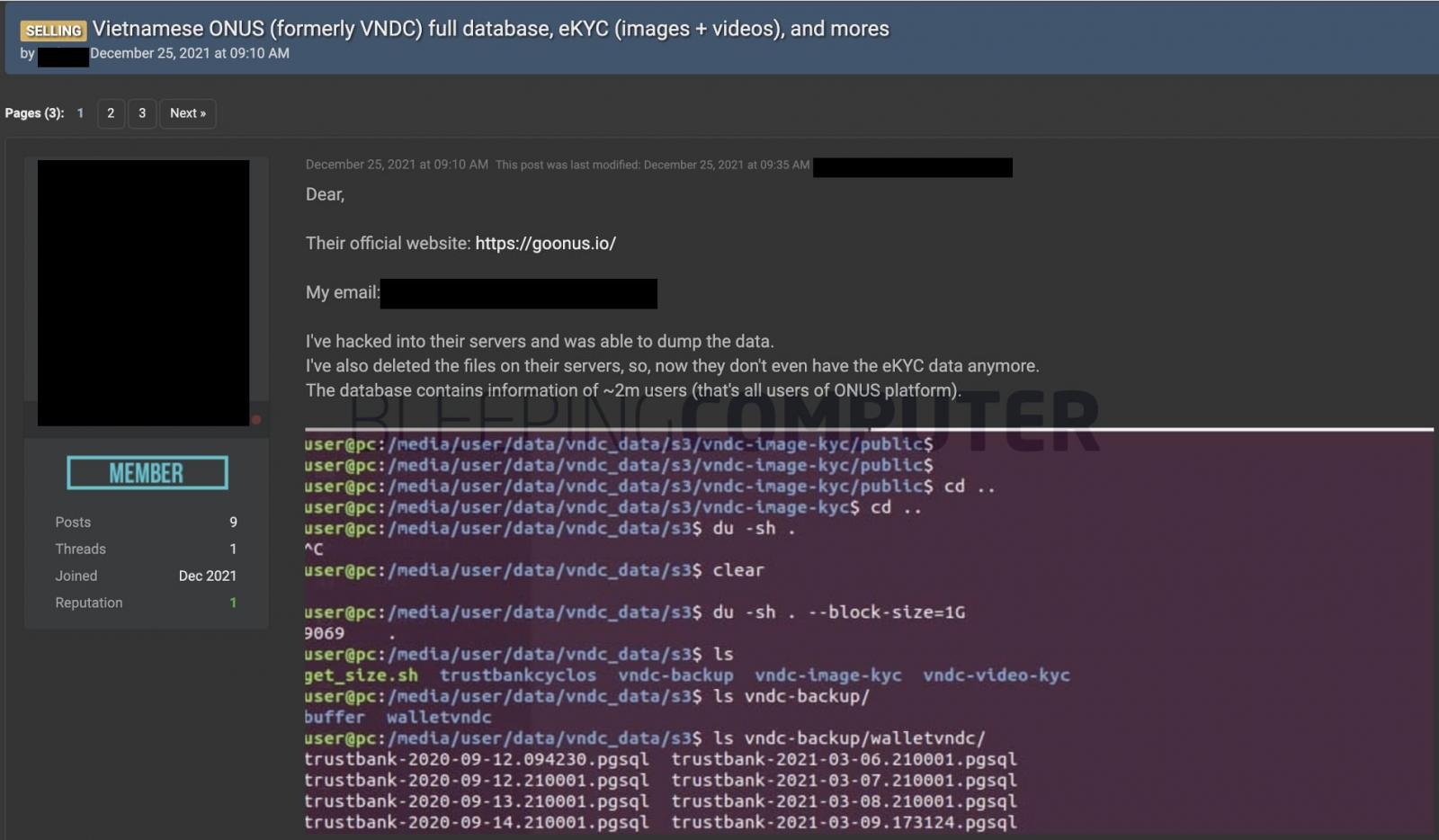
The menace actors declare to have copies of 395 ONUS database tables with clients’ private info and hashed passwords of their possession.
Samples of such information have been printed by the menace actor in the discussion board submit seen by BleepingComputer.
The samples additionally included photos of shoppers’ ID playing cards, passports, and customer-submitted video selfie clips procured throughout the KYC course of.
“We sincerely apologize and hope in your understanding,” states ONUS.
“That is additionally a possibility for us to evaluate ourselves, improve and additional excellent the system to guarantee the security of our customers, particularly in the course of the transition from VNDC to ONUS.”
CyStack’s suggestions to ONUS included patching the Log4Shell vulnerability in Cyclos–as instructed by the seller, deactivating leaked AWS credentials, correctly configuring AWS entry permissions, blocking public entry to all delicate S3 buckets, and imposing further restrictions.
By now log4j vulnerabilities have been exploited by all types of menace actors from state-backed hackers to ransomware gangs and some others to inject crypto miners on weak methods.
The Conti ransomware gang has additionally been seen eying weak VMWare vCenter servers for exploitation.
Log4j customers ought to instantly improve to the newest model 2.17.1 (for Java 8) launched yesterday. Backported variations 2.12.4 (Java 7) and a pair of.3.2 (Java 6) containing the repair are anticipated to be launched shortly.
[ad_2]
