[ad_1]
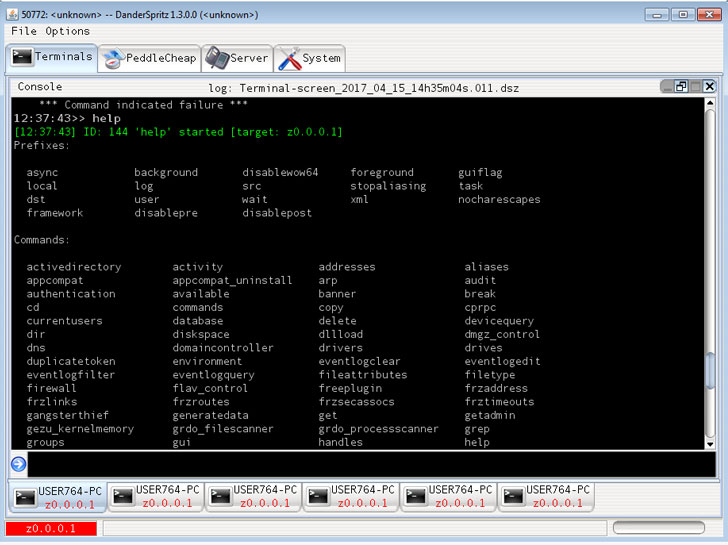
Cybersecurity researchers have provided an in depth glimpse right into a system referred to as DoubleFeature that is devoted to logging the completely different levels of post-exploitation stemming from the deployment of DanderSpritz, a full-featured malware framework utilized by the Equation Group.
DanderSpritz got here to mild on April 14, 2017, when a hacking group generally known as the Shadow Brokers leaked the exploit instrument, amongst others, below a dispatch titled “Misplaced in Translation.” Additionally included within the leaks was EternalBlue, a cyberattack exploit developed by the U.S. Nationwide Safety Company (NSA) that enabled risk actors to hold out the NotPetya ransomware assault on unpatched Home windows computer systems.
The instrument is a modular, stealthy, and totally practical framework that depends on dozens of plugins for post-exploitation actions on Home windows and Linux hosts. DoubleFeature is one amongst them, which capabilities as a “diagnostic instrument for sufferer machines carrying DanderSpritz,” researchers from Verify Level mentioned in a brand new report revealed Monday.
“DoubleFeature might be used as a type of Rosetta Stone for higher understanding DanderSpritz modules, and techniques compromised by them,” the Israeli cybersecurity agency added. “It is an incident response crew’s pipe dream.”
Designed to keep up a log of the varieties of instruments that might be deployed on a goal machine, DoubleFeature is a Python-based dashboard that additionally doubles up as a reporting utility to exfiltrate the logging data from the contaminated machine to an attacker-controlled server. The output is interpreted utilizing a specialised executable named “DoubleFeatureReader.exe.”
A few of the plugins monitored by DoubleFeature embrace distant entry instruments referred to as UnitedRake (aka EquationDrug) and PeddleCheap, a stealthy knowledge exfiltration backdoor dubbed StraitBizarre, an espionage platform referred to as KillSuit (aka GrayFish), a persistence toolset named DiveBar, a covert community entry driver referred to as FlewAvenue, and a validator implant named MistyVeal that verifies if the compromised system is certainly an genuine sufferer machine and never a analysis surroundings.
“Typically, the world of high-tier APT instruments and the world of strange malware can seem to be two parallel universes,” the researchers mentioned. “Nation-state actors are inclined to [maintain] clandestine, gigantic codebases, sporting an enormous gamut of options which were cultivated over many years resulting from sensible want. It seems we too are nonetheless slowly chewing on the 4-year-old leak that exposed DanderSpritz to us, and gaining new insights.”
[ad_2]