[ad_1]
As a CISO, some of the difficult inquiries to reply is “How properly are we protected proper now?” Between the acceleration of hackers’ offensive capabilities and the dynamic nature of knowledge networks, a drift within the safety posture is unavoidable and must be constantly compensated. Due to this fact, answering that query implies constantly validating the safety posture and being ready to test it together with, towards the most recent rising threats.
But, the majority of cybersecurity is targeted on defensive instruments. The mix of the fast evolution of expertise and the multiplication of expertise layers, mixed with the professionalization of the risk panorama, has led to a profusion of cybersecurity instruments tackling completely different safety elements.
Checking the cybersecurity answer stack effectivity is often executed by means of pen-testing or, extra lately, by means of crimson teaming – an train aimed to map potential loopholes that might lead to a knowledge breach. When carried out a couple of times a 12 months solely, these exams would possibly fulfill the compliance regulators. Nonetheless, as new threats emerge every day, they fail to tell in regards to the setting’s present safety posture successfully.
As well as, these rare exams fail to tell about potential device overlaps and should not designed to forestall device sprawl, a frequent prevalence in a area the place over half of SOC facilities are overrun with redundant safety instruments and are swamped by too many alerts.
Unrationalized safety stacks should not solely unnecessarily expensive, however additionally they generate extra false-positive calls, needlessly taxing safety workers stamina and rising the danger of lacking a crucial alert.
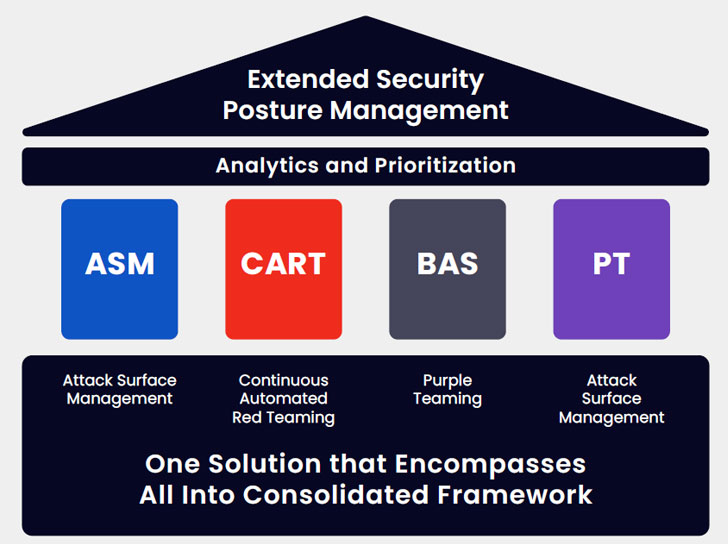
The flexibility to measure every device’s efficacy, remove overlap and keep steady management over safety baseline variability depends on steady entry to quantified knowledge. That is on the core of what Prolonged Safety Posture Administration (XPSM) brings to the desk.
Understanding Prolonged Safety Posture Administration
Prolonged Safety Posture Administration (XSPM) is a multilayered course of combining the capabilities of Assault Floor Administration (ASM), Breach and Assault Simulation (BAS), Steady Automated Purple Teaming (CART), and Purple Teaming to constantly consider and rating the infrastructure’s total cyber resiliency.
This up-to-date complete snapshot of the energetic safety posture, mixed with detailed remediation course of suggestions, is conducive to creating rational enterprise choices primarily based on laborious knowledge.
Utilizing the granular analysis of every particular person device and of the safety management configuration, an XSPM answer gives granular details about every answer used, the eventual overlap between two or extra options and the remaining safety gaps. It then gives detailed suggestions in regards to the remediation course of for every hole and optimization choices for recognized overlaps.
The Benefit of a Consolidated, Intensive Baseline
Safety groups are systematically impressed by the distinction in having actionable knowledge made, each in enhancing the safety posture and in rationalizing cybersecurity spending.
XSPM helps the safety crew to take care of the fixed content material configuration churn and leverages telemetry to assist determine the gaps in safety by producing up-to-date rising threats feeds and offering extra check instances emulating TTPs that attackers would use, saving DevSocOps the time wanted to develop these check instances. When working XSPM validation modules, understanding that the exams are well timed, present, and related allows reflecting on the efficacy of safety controls and understanding the place to make investments to make sure that the configuration, hygiene and posture are maintained by means of the fixed adjustments within the setting.
By offering visibility and maximizing relevancy, XSPM helps confirm that every greenback spent advantages threat discount and gear efficacy by means of baselining and trending and mechanically producing studies containing detailed suggestions overlaying safety hardening and gear stack optimization; it dramatically facilitates conversations with the board.
The change from rare to common testing, made potential by automation, allows each the continual baseline variability monitoring and the quantified calculation of ROI achieved by means of device stack rationalization.
Moreover, it allows creating attack-based vulnerability administration by leveraging the outcomes to prioritize patching.
As a bonus, checking an setting’s potential to face up to the most recent assaults could be executed nearly at a click on, and, if wanted, really useful mitigation processes could be pushed ahead within the prioritized patching schedule.
George Washington’s adage “The very best protection is an effective offense” positively applies to cybersecurity, and the continual offense is the one option to keep forward of the attackers’ progress persistently.
Be aware: This text was written by Arien Seghetti, Answer Architect at Cymulate. For extra data, go to www.cymulate.com and register for a Free Trial.
[ad_2]