[ad_1]
At the least 17 malware-laced packages have been found on the NPM bundle Registry, including to a current barrage of malicious software program hosted and delivered by open-source software program repositories resembling PyPi and RubyGems.
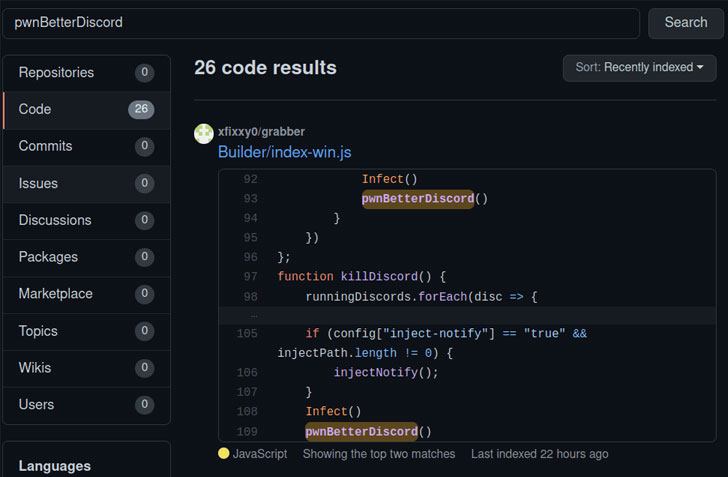
DevOps agency JFrog stated the libraries, now taken down, have been designed to seize Discord entry tokens and surroundings variables from customers’ computer systems in addition to achieve full management over a sufferer’s system.
“The packages’ payloads are assorted, starting from infostealers as much as full distant entry backdoors,” researchers Andrey Polkovnychenko and Shachar Menashe stated in a report revealed Wednesday. “Moreover, the packages have completely different an infection ways, together with typosquatting, dependency confusion and trojan performance.”
The record of packages is under –
- prerequests-xcode (model 1.0.4)
- discord-selfbot-v14 (model 12.0.3)
- discord-lofy (model 11.5.1)
- discordsystem (model 11.5.1)
- discord-vilao (model 1.0.0)
- fix-error (model 1.0.0)
- wafer-bind (model 1.1.2)
- wafer-autocomplete (model 1.25.0)
- wafer-beacon (model 1.3.3)
- wafer-caas (model 1.14.20)
- wafer-toggle (model 1.15.4)
- wafer-geolocation (model 1.2.10)
- wafer-image (model 1.2.2)
- wafer-form (model 1.30.1)
- wafer-lightbox (model 1.5.4)
- octavius-public (model 1.836.609)
- mrg-message-broker (model 9998.987.376)
As prior analysis has established, collaboration and communication instruments like Discord and Slack have turn into useful mechanisms for cybercriminals, with Discord servers built-in into the assault chains for remotely controlling the contaminated machines and even to exfiltrate knowledge from the victims.
“Cyber criminals are utilizing Discord CDN to host malicious information in addition to for command-and-control (C&C) communication,” cybersecurity agency Zscaler famous in an evaluation earlier this February. “As a result of static content material distribution service, it’s extremely common amongst risk actors to host malicious attachments that stay publicly accessible even after eradicating precise information from Discord.”
In mild of those disclosures, it is no shock that the theft of Discord entry tokens might allow risk actors to make use of the platform as a covert knowledge exfiltration channel, distribute malware to different Discord customers, and even promote Discord Nitro premium accounts to different third-parties, who can then use them for their very own campaigns.
Much more troublingly, the bundle “prerequests-xcode” functioned as a full-fledged distant entry trojan, a Node.JS port of DiscordRAT, that is outfitted to seize screenshots, collect clipboard knowledge, execute arbitrary VBScript and PowerShell code, steal passwords, and obtain malicious information, successfully granting the adversary the power to take over the developer’s system.
If something, the event provides to an more and more “disturbing pattern” of utilizing rogue packages as a stealthy compromise vector to facilitate an array of malicious actions, together with supply-chain assaults.
“Public repositories have turn into a useful instrument for malware distribution: the repository’s server is a trusted useful resource, and communication with it doesn’t increase the suspicion of any antivirus or firewall,” the researchers stated. “As well as, the benefit of set up through automation instruments such because the NPM shopper, supplies a ripe assault vector.”
[ad_2]