[ad_1]
A newly found botnet able to staging distributed denial-of-service (DDoS) assaults focused unpatched Ribbon Communications (previously Edgewater Networks) EdgeMarc home equipment belonging to telecom service supplier AT&T by exploiting a four-year-old flaw within the community home equipment.
Chinese language tech big Qihoo 360’s Netlab community safety division, which detected the botnet first on October 27, 2021, known as it EwDoor, noting it noticed 5,700 compromised IP addresses positioned within the U.S. throughout a short three-hour window.
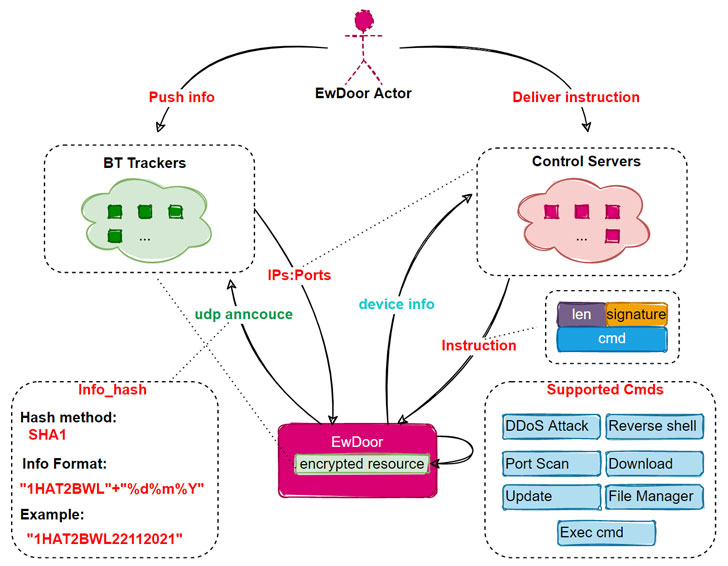
“To date, the EwDoor in our view has undergone three variations of updates, and its fundamental features will be summarized into two fundamental classes of DDoS assaults and backdoor,” the researchers famous. “Primarily based on the attacked gadgets are phone communication associated, we presume that its fundamental goal is DDoS assaults, and gathering of delicate info, equivalent to name logs.”
Propagating by means of a flaw in EdgeMarc gadgets, EwDoor helps quite a lot of options, together with the flexibility to self-update, obtain information, receive a reverse shell on the compromised machine, and execute arbitrary payloads. The vulnerability in query is CVE-2017-6079 (CVSS rating: 9.8), a command injection flaw affecting the session border controllers that might be weaponized to execute malicious instructions.
EwDoor, in addition to gathering details about the contaminated system, additionally establishes communications with a distant command-and-control (C2) server, both straight or not directly utilizing BitTorrent Trackers to fetch the C2 server IP handle, to await additional instructions issued by the attackers.
When reached for a remark, AT&T mentioned “We beforehand recognized this subject, have taken steps to mitigate it and proceed to analyze,” and that “we’ve got no proof that buyer knowledge was accessed.”
[ad_2]